What Is Risk Posture, Solutions & Best Practices for Improving It
Risk posture refers to an organization's overall approach to managing risks related to cybersecurity and information technology.
What is Risk Posture?
Risk posture refers to an organization’s overall approach to managing cybersecurity risks. It encompasses the organization’s attitude towards risk, the level of risk it is willing to tolerate, and the strategies and controls it employs to manage and mitigate those risks.
An organization’s risk posture is shaped by a number of factors, including its business objectives, regulatory requirements, industry best practices, and the threat landscape it faces. It is typically informed by a formal risk management process that involves identifying and assessing risks, prioritizing them based on their potential impact and likelihood, and developing and implementing risk mitigation strategies.
This is part of a series of articles about vulnerability management.
In this article:
- Why Is Risk Posture Important?
- What Is a Risk Posture Assessment?
- Types of Cybersecurity Posture Management
- Cloud Security Posture Management (CSPM)
- Application Security Posture Management (ASPM)
- Data Security Posture Management (DSPM)
- Kubernetes Security Posture Management (KSPM)
- Risk Posture Best Practices
- Inventory All Assets
- Track Security Metrics
- Implement Automated Cybersecurity Solutions
- Create an Incident Response Plan
Why Is Risk Posture Important?
Risk posture is important for several reasons:
- Risk posture helps organizations to identify and prioritize risks: By defining their risk posture, organizations can better understand the types of risks they face and prioritize their risk management efforts accordingly. This can help organizations to allocate resources more effectively and efficiently, and to focus on the risks that pose the greatest threat to their operations, reputation, or bottom line.
- Risk posture helps organizations to set risk management objectives: By defining their risk posture, organizations can establish clear objectives for risk management that align with their overall goals and strategy. This can help organizations to develop risk management plans that are tailored to their unique needs and circumstances, and that provide a clear roadmap for achieving their risk management objectives.
- Risk posture helps organizations to establish risk culture: By defining their risk posture, organizations can establish a risk culture that is consistent with their values, vision, and mission. This can help organizations to foster a culture of risk awareness, responsibility, and accountability, and to encourage employees to take ownership of risk management.
- Risk posture helps organizations to communicate with stakeholders: By defining their risk posture, organizations can communicate their risk management approach and priorities to stakeholders, such as investors, regulators, customers, and employees. This can help organizations to build trust and confidence with stakeholders, and to demonstrate their commitment to responsible risk management.
- Risk posture helps organizations to adapt to changing risks: By defining their risk posture, organizations can establish a framework for monitoring and managing risks over time, and for adapting their risk management approach as risks evolve or new risks emerge. This can help organizations to stay ahead of the curve, anticipate and respond to risks more effectively, and ensure their long-term success and sustainability.
What Is a Risk Posture Assessment?
A risk posture assessment is a process that evaluates an organization’s overall approach to managing risks related to cybersecurity and information technology. The assessment is typically performed by a cybersecurity or risk management professional and involves a comprehensive review of the organization’s policies, procedures, and controls related to risk management.
It typically involves identifying assets, evaluating existing controls, locating security gaps, and prioritizing risks. It provides organizations with a comprehensive understanding of their cybersecurity risk exposure and identifies areas for improvement. This assessment can help organizations better protect their critical assets and reduce their risk of a cybersecurity incident.
Cybersecurity Posture Management Solutions
There are several types of technological solutions that can help organizations manage their risk posture. These include:
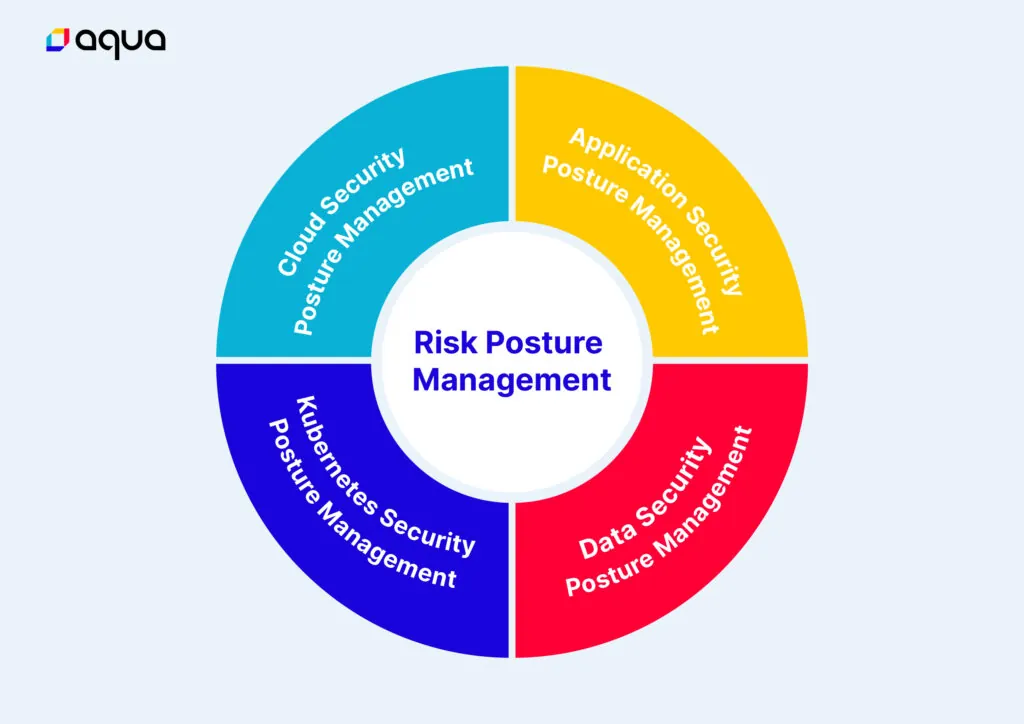
Cloud Security Posture Management (CSPM)
Cloud environments are dynamic and complex, which can make it challenging to maintain a strong security posture. CSPM involves using specialized tools to scan cloud-based infrastructure, applications, and data to identify misconfigurations, vulnerabilities, and other risks. CSPM can help organizations maintain a strong security posture in the cloud by providing continuous monitoring and automated remediation of security issues.
Application Security Posture Management (ASPM)
Application security posture management (ASPM) solutions are a type of security software that helps organizations manage the security posture of their applications. ASPM solutions work by scanning an organization’s application environment, identifying potential security risks and vulnerabilities, and providing recommendations on how to remediate or mitigate those risks.
Data Security Posture Management (DSPM)
DSPM solutions refer to a novel approach to securing cloud data by prioritizing data protection. The increasing amount of data in modern multi-cloud organizations has resulted in a higher risk of sensitive data loss or compromise. This makes cloud data security the primary concern for security stakeholders, particularly those employing outdated security strategies.
DSPM offers a modern approach to comprehensively understanding all factors that impact the security posture of your data. By using DSPM, you can easily locate sensitive data across your cloud environment, control who has access to it, and assess the security posture of such data.
Kubernetes Security Posture Management (KSPM)
KSPM solutions are software tools or platforms designed to help organizations secure their Kubernetes environments by providing visibility, compliance, and risk management capabilities. These solutions leverage the Kubernetes API to collect data about the cluster’s configuration, deployment, and runtime activities. They use this data to assess the security posture of the Kubernetes environment, identify security risks and compliance gaps, and provide recommendations for remediation.
Risk Posture Best Practices
Inventory All Assets
Conducting a comprehensive inventory of all the organization’s assets is the foundation of effective risk management. This involves identifying all hardware, software, and data used by the organization, including those used by employees, contractors, and third-party vendors. By knowing what assets are in use, organizations can better understand their risk exposure and ensure that all assets are protected appropriately.
Track Security Metrics
Organizations should establish metrics for measuring the effectiveness of their cybersecurity program. These metrics can include the number of incidents detected and resolved, the time it takes to detect and respond to incidents, and the effectiveness of security controls. By tracking these metrics, organizations can identify areas for improvement and continuously improve their cybersecurity posture.
Implement Automated Cybersecurity Solutions
Automated cybersecurity solutions, such as firewalls, intrusion detection and prevention systems, and endpoint protection software, can help identify and respond to threats more quickly and effectively. These solutions can be configured to detect and respond to threats automatically, freeing up security personnel to focus on more complex issues.
Create an Incident Response Plan
An incident response plan is a formal document that outlines the steps to be taken in the event of a cybersecurity incident. The plan should include procedures for detecting and containing the incident, assessing the impact, and communicating with stakeholders. By having a formal incident response plan in place, organizations can respond more quickly and effectively to incidents, minimizing the impact on the organization.
