Building a Cloud Security Strategy in 2023
A cloud security strategy is a comprehensive plan that outlines the policies, processes, technologies, and practices an organization adopts to protect its cloud-based infrastructure, applications, and data.
What Is a Cloud Security Strategy?
A cloud security strategy is a comprehensive plan that outlines the policies, processes, technologies, and practices an organization adopts to protect its cloud-based infrastructure, applications, and data. The strategy aims to mitigate risks, prevent security breaches, ensure compliance with relevant regulations, and maintain the confidentiality, integrity, and availability of data in the cloud environment.
Developing a robust cloud security strategy requires a thorough understanding of the organization’s cloud environment, business objectives, and unique risk factors. In addition, it should be informed by new industry paradigms that can positively impact cloud security. We’ll review several important paradigms, and describe the key elements of a successful cloud security strategy.
In this article:
Industry Paradigms that Should Inform Your Cloud Security Strategy
The security industry is rapidly advancing, and new approaches are being introduced that have a significant impact on cloud security. Here are three new paradigms that are being widely introduced in the industry, and should probably play a role in your cloud security strategy.
Shared Responsibility
When using cloud services, security is a shared responsibility between the cloud service provider and the user. Cloud providers are generally responsible for securing the underlying infrastructure, while users are responsible for securing the data they put on the cloud and how they use cloud services. Understanding this model is vital to ensure no aspects of security are overlooked.
Zero Trust
Zero trust is a security model that assumes no user or device is trustworthy by default, regardless of whether they are located inside or outside the network perimeter. It suggests that each access request should be validated, authenticated, and encrypted.
Implementing a Zero trust model in your cloud strategy can help prevent unauthorized access, minimize the potential impact of security breaches, and provide greater visibility into network traffic. Key components of a zero trust strategy include multi-factor authentication (MFA), least privilege access, and continuous monitoring and validation.
DevSecOps
DevSecOps, the practice of integrating security into the DevOps process, is critical for a robust cloud security strategy. It emphasizes the need to build security practices into the entire lifecycle of application development and deployment, rather than being treated as an afterthought or a separate phase.
Key considerations when implementing DevSecOps include automated security checks, code reviews, vulnerability scanning, and regular security training for the DevOps team.
Related content: Read our guide to cloud infrastructure security
4 Key Elements of an Effective Cloud Security Strategy
Here are the key elements you should include in your organization’s cloud security strategy.
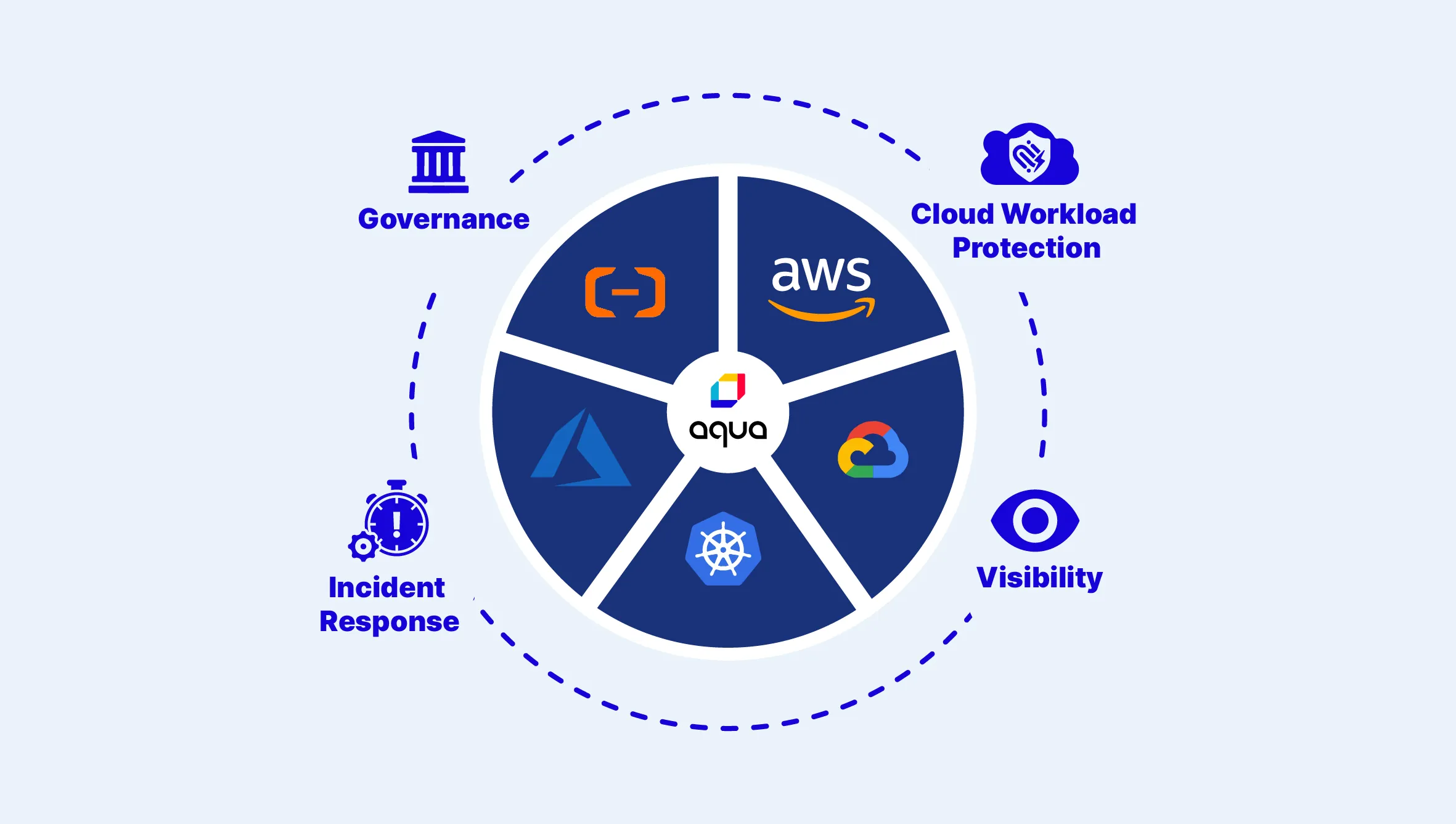
1. Visibility
Visibility enables organizations to monitor and maintain control over their cloud assets. This includes having a clear understanding of the cloud environment, including the data, applications, and infrastructure being used, as well as the users and devices accessing these resources. Achieving visibility in a cloud environment can be challenging due to its dynamic and multi-tenant nature, but it is essential for identifying potential risks and vulnerabilities and ensuring that adequate security controls are in place.
There are several tools and technologies available to help organizations achieve visibility in their cloud environment, including cloud access security brokers (CASBs), cloud security posture management (CSPM) solutions, and cloud-native monitoring and logging services. These tools can provide real-time visibility into the organization’s cloud assets and help identify potential security issues, such as misconfigurations, unauthorized access, or suspicious activity.
2. Governance
Effective governance involves implementing a set of policies, processes, and controls that help ensure that the organization’s cloud assets are protected and that security risks are managed effectively. Governance also involves ensuring that the organization’s security policies and procedures are aligned with industry regulations and standards, as well as with the organization’s risk tolerance and security objectives.
Some essential aspects of security posture and governance in a cloud environment include:
- Implementing a formal cloud security governance framework that outlines the organization’s policies, processes, and controls for managing cloud security risks.
- Ensuring that security policies and procedures are regularly reviewed and updated to reflect changes in the organization’s cloud environment and the threat landscape.
- Establishing clear lines of responsibility and accountability for cloud security within the organization, including the division of responsibilities between the organization and the cloud service provider.
- Regularly conducting security assessments, audits, and penetration tests to evaluate the effectiveness of the organization’s cloud security controls and identify areas for improvement.
3. Cloud Workload Protection
Cloud workload protection involves establishing security measures for applications, services, and data hosted in the cloud. Cloud workloads can vary significantly in terms of their security requirements and potential vulnerabilities, and workload protection should take into account the unique aspects of each workload.
Some key aspects of cloud workload protection include:
- Implementing appropriate encryption and data protection measures to ensure that sensitive data is protected both at rest and in transit.
- Using application security best practices, such as secure coding techniques and regular vulnerability assessments, to minimize the risk of application-level vulnerabilities.
- Employing container and microservices security measures, such as container runtime security and monitoring tools, to protect cloud-native applications and services.
- Leveraging network segmentation and zero-trust networking principles to minimize the potential impact of a security breach on cloud workloads.
4. Incident Response
A robust incident response plan ensures that organizations are prepared to effectively manage and respond to security incidents in their cloud environment. Having a well-defined and tested incident response plan in place can help organizations minimize the potential damage and disruption caused by a security breach, as well as meet their legal and regulatory obligations.
Key aspects of an effective cloud incident response plan include:
- Clearly defining the roles and responsibilities of the incident response team, including the involvement of external stakeholders such as cloud service providers, law enforcement agencies, and regulatory bodies.
- Establishing a clear process for identifying, reporting, and managing security incidents, including the use of automated incident detection and response tools to speed up the response process.
- Ensuring that the incident response plan is regularly reviewed and updated to reflect changes in the organization’s cloud environment, the threat landscape, and industry best practices.
- Conducting regular incident response drills and exercises to test the effectiveness of the plan and identify areas for improvement.
