What Is Cloud Security Posture Management (CSPM)?
CSPM, or Cloud Security Posture Management, is a category of security solutions that offer continuous compliance monitoring, visibility into cloud infrastructure, and remediation of security risks. These tools are designed to manage the security posture of a cloud environment, helping organizations identify and address potential security gaps before they can be exploited.
What is CSPM?
The main aim of CSPM is to prevent misconfigurations in the cloud—a significant cause of data breaches. Misconfigurations can occur due to the complexity of cloud infrastructure and the rapid pace of change in deploying and updating cloud resources. With CSPM, businesses can ensure their cloud configurations align with security best practices and policies.
CSPM tools automate the detection and remediation of security risks in the cloud, reducing the manual effort required to maintain a robust security posture. They also provide a centralized platform for managing security across multiple cloud environments, making them essential for organizations leveraging a multi-cloud strategy. Furthermore, these tools help organizations meet compliance requirements by providing automated compliance checks and generating detailed reports for audit purposes.
In this article:
The Need for CSPM
Growing Adoption of Cloud Services
The adoption of cloud services is on the rise across all industries. According to a recent Gartner report, the worldwide public cloud services market is projected to grow by 21% in 2023, reaching a total of $591.8 billion. This growth is driven by the need for organizations to scale their operations rapidly and cost-effectively.
However, with this increased usage of cloud services, the risk of security breaches also rises. Traditional security measures are not equipped to handle the unique threats that the cloud environment presents. By providing a comprehensive view of the entire cloud environment, CSPM tools help organizations identify and mitigate potential security risks.
Increased Complexity of Multi-Cloud Environments
As organizations continue to embrace digital transformation, they often find themselves managing multiple cloud environments from different cloud providers. This multi-cloud approach offers many benefits, including improved reliability, cost optimization, and increased flexibility. However, it also increases complexity, making it harder to maintain a robust security posture.
CSPM tools can help manage the complexity of multi-cloud environments by providing a centralized platform for monitoring and managing security. They provide visibility into all cloud environments, regardless of the service provider, making it easier to identify and address potential vulnerabilities.
Learn more in our detailed guide to multi-cloud strategy
Prevalence of Misconfigurations in Cloud Security
Misconfigurations are a significant source of security risks in cloud environments. For example, a recent report by Aqua’s Nautilus research team uncovered misconfigurations in the registries of five Fortune 500 companies, exposing more than 250 million software artifacts.
This highlights the critical need for CSPM tools, which can continuously monitor cloud environments for misconfigurations and help remediate them to prevent breaches.
Compliance Requirements
Organizations that handle sensitive data, such as financial or health information, are subject to stringent compliance requirements. Non-compliance can result in hefty fines and significant damage to an organization’s reputation. CSPM tools play a crucial role in ensuring compliance in the cloud by providing automated compliance checks and generating detailed reports that can be used for audit purposes.
10 Key Features of CSPM Tools
1. Auto-Discovery of Cloud Resources
CSPM tools can identify all assets in your cloud environment, regardless of where they are hosted or how they are configured. This feature is essential because it allows for a complete and accurate inventory of your cloud assets.
CSPM tools can identify a wide range of resources and services, including virtual machines (VMs), containers, serverless functions, Kubernetes clusters, and more. They can also discover resources across multiple cloud platforms, such as Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform. This unified visibility is crucial as it allows organizations to manage their cloud assets effectively and ensure they are secure.
Furthermore, the auto-discovery feature helps to keep your inventory up-to-date. CSPM tools can continuously scan your cloud environment to detect changes or new resources. This ensures that your inventory remains accurate and current, enabling you to manage your cloud security effectively.
Learn more in our detailed guide to cloud security scanner
2. Visibility into Cloud Infrastructure and Workloads
CSPM tools can provide a centralized view of your cloud environment, helping you to understand your cloud infrastructure and workloads and manage your risk posture effectively.
CSPM tools can provide detailed insights into your cloud risks, including workload configurations, relationships, and dependencies between workloads. They also provide visibility into your workload risks, including vulnerabilities, exposed secrets, malware, and compliance status. This can help you to identify any issues and take corrective action.
Furthermore, CSPM tools can also provide visibility across multiple cloud platforms. This is especially important for organizations that use a multi-cloud strategy, as it allows them to manage their cloud security effectively across all their cloud environments.
3. Misconfiguration Monitoring and Mitigation
Misconfigurations are a common cause of data breaches in cloud environments. They can occur when cloud resources are not configured correctly, leading to gaps that can be exploited by attackers.
CSPM tools can continuously monitor your cloud environment to detect any misconfigurations. They can check your configurations against established best practices and alert you to any deviations. This allows you to quickly identify and remediate any issues before they can be exploited.
Furthermore, some CSPM tools also provide automated remediation capabilities. This means they can not only detect misconfigurations but also fix them automatically. This can significantly reduce the time and effort required to manage your cloud security.
4. Agentless Risk Assessment
CSPM tools perform agentless vulnerability scanning. This involves taking snapshots of running workloads and scanning them via cloud provider APIs. This method provides quick visibility into cloud workloads, risk posture management, while detecting some, but not all, risks, such as misconfigurations, vulnerabilities, and more.
Based on these methods, CSPM tools can identify, assess, and manage risks in your cloud environment. They can prioritize risks based on various factors, including the severity of potential impact and the likelihood of exploitation. CSPM tools provide a risk score for each identified issue, helping you understand risk exposure and prioritize your remediation efforts.
5. Context-Based Insights
CSPM tools go beyond simply identifying vulnerabilities and misconfigurations; they offer context-based insights to help organizations understand the scope and impact of each identified issue. Context-based insights incorporate additional data, such as user activity, data sensitivity, and threat intelligence, to provide a comprehensive view of the risk environment.
For example, if a CSPM tool identifies an open database, it will also evaluate what kind of data the database holds, who has access to it, and whether there have been any recent attempts to exploit similar vulnerabilities. The tool might integrate with other security systems to gather threat intelligence, such as known IP addresses associated with malicious activity, to provide additional context.
6. Risk Visualization and Risk Prioritization
CSPM tools can visualize your risk landscape, helping you to understand your risk exposure at a glance. They can also prioritize risks based on their severity and likelihood of exploitation, helping you to focus your remediation efforts where they are most needed.
CSPM tools can provide various types of visualizations, including dashboards, charts, and graphs. These visualizations can help you to understand your risk landscape, and also to communicate your risk exposure to other stakeholders, including senior management and auditors.
Below is an example of a security graph in the Aqua CSPM solution.
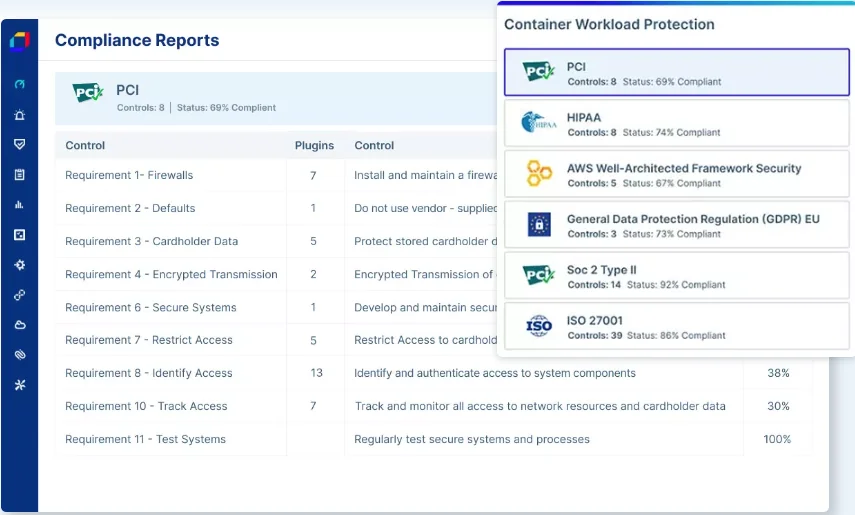
7. Compliance Monitoring
Compliance in the cloud is a challenging task, given the dynamic nature of cloud environments. CSPM tools simplify this process by automating compliance monitoring and ensuring that your cloud environment adheres to the necessary industry standards and regulations.
Compliance monitoring with CSPM tools involves continuous scanning and monitoring of your cloud configurations to ensure they meet the required compliance standards. These tools not only detect non-compliant configurations and potential vulnerabilities but also provide detailed reports that can be used for audit purposes. They can also send alerts in real time whenever there’s a compliance violation, thereby allowing you to take immediate action.
8. Cloud Threat Detection
CSPM tools are equipped with a variety of technologies that help detect potential threats in your cloud environment. They continuously monitor your cloud configurations and identify any anomalies that could indicate a potential security threat. This includes detecting unauthorized access, identifying fileless malware and other advanced threats, and spotting potential vulnerabilities that could be exploited by cybercriminals. The combination of agentless and agent-based scanning helps CSPM identify a wide variety of threats.
The threat detection capabilities of CSPM tools are powered by technologies like artificial intelligence and machine learning. These technologies enable CSPM tools to analyze large volumes of data and identify potential threats quickly and accurately. They also enable these tools to learn from past incidents and improve their threat detection capabilities over time.
9. Code to Cloud Visibility and Traceability
CSPM tools can monitor and manage every aspect of your cloud environment, from the code produced by development teams to the workloads that are running in the cloud. This level of visibility enables you to identify and address potential security issues at every stage of the development and deployment process.
Code to cloud visibility also aids in traceability. With CSPM tools, you can trace the lifecycle of every resource in your cloud environment. This includes tracking the changes made to these resources, identifying who made these changes, and determining when and why these changes were made. This level of traceability is crucial in maintaining a strong security posture as it enables you to quickly identify the source of the issue, find the developer responsible for it and enable fast remediation.
10. Guided Remediation
While CSPM tools are excellent at detecting potential security issues, they also excel in providing guided remediation. When a potential issue is detected, these tools don’t just alert you about the problem, they also provide detailed guidance on how to fix it. This includes providing step-by-step instructions, best practices, and even automated remediation capabilities.
Guided remediation is crucial in ensuring that the detected issues are addressed effectively and efficiently. It helps you understand the issue, determine the best course of action, and implement the necessary remediation actions. Moreover, guided remediation also helps in educating your team about the best practices for cloud security.
CSPM vs. Other Cloud Security Solutions
CSPM vs. CNAPP
Cloud Native Application Protection Platforms (CNAPP) are designed to secure applications built on the cloud native stack. They protect cloud native applications across the entire lifecycle—from development to production.
CNAPPs consolidate multiple previously disparate capabilities, such as container scanning, infrastructure-as-code (IaC) scanning, cloud infrastructure entitlement management (CIEM), cloud security posture management (CSPM), runtime workload protection (CWPP), runtime configuration scanning, and vulnerability scanning.
CSPM tools, on the other hand, focus on managing security risks associated with misconfigurations in the cloud. Unlike CNAPP, CSPM tools are not typically built for application-level protection. They concentrate more on infrastructure-level security risks.
While CNAPP is geared towards protecting applications, CSPM is more concerned with the overall security posture of the cloud environment.
CSPM vs. CWPP
Cloud Workload Protection Platforms (CWPP) are designed to protect workloads across any cloud environment. CWPP provides runtime protection for VMs, containers, Kubernetes, and serverless workloads.
In comparison, CSPM tools focus on managing and preventing security risks stemming from misconfigurations in the cloud. CSPM tools do not provide protection for workloads; instead, they focus on reducing the attack surface and ensure that the cloud environment is configured correctly to prevent breaches.
While CWPP is focused on workload protection, CSPM is more about managing the overall security posture of the cloud environment. Both tools are essential and are often used together.
CSPM vs. CASB
Cloud Access Security Brokers (CASB) are on-premise or cloud-based software that sit between cloud service consumers and cloud service providers. They enforce security policies such as authentication, encryption, and device profiling.
On the other hand, CSPM tools identify and manage risks related to misconfigurations in the cloud. They do not sit between the cloud service consumer and provider; instead, they work on the cloud environment to ensure it is configured securely.
While CASB controls access to cloud services, CSPM ensures that the cloud environment is secure. For complete security, it is a good idea to use both CSPM and CASB.
Learn more in our detailed guide to cloud security solutions
Gartner’s Vision: CSPM and CWPP Will Be Part of CNAPP
In a move towards a more integrated approach to cloud security, Gartner predicts that Cloud Security Posture Management (CSPM) and Cloud Workload Protection Platforms (CWPP) will eventually become part of Cloud Native Application Protection Platforms (CNAPP).
As organizations continue to shift towards cloud native applications, there is a growing need for comprehensive security solutions that cover all stages of the application lifecycle. By integrating CSPM, CWPP, and CNAPP, organizations can manage their cloud security posture, protect their cloud workloads, and secure their applications with a single platform.
This integration will provide several key benefits:
- Unified security management: By integrating CSPM, CWPP, and CNAPP, organizations can manage their cloud security from a single platform. This can reduce complexity and make it easier to identify and address potential security risks.
- Comprehensive protection: The integration of these three platforms will provide protection at every level of the cloud environment—from the infrastructure and workloads to the applications.
- Improved efficiency: A unified platform can streamline security management and reduce the time and effort required to manage cloud security. This can lead to cost savings and free up resources to focus on other critical areas.
- Better visibility: Integrating these platforms can provide better visibility into the cloud environment. This can improve detection and response capabilities, enabling organizations to quickly identify and respond to potential threats.
CSPM as Part of Aqua Cloud Native Security Platform
Aqua Real-Time CSPM provides a complete view of your real-time cloud security risk, surfacing the most critical issues so you can focus on fixing what matters most. Real-Time CSPM accurately identifies cloud risks and pinpoints threats that evade agentless detection. It delivers rich, context-based insights and actionable remediation recommendations for faster, more effective cloud risk management.
Real-time CSPM is an integrated part of the Aqua CNAPP solution, Aqua Cloud Native Security Platform, which enables organizations to unify cloud native application protection to detect, prioritize, and reduce risks across every phase of their software development life cycle.
