Agentless vs. Agent Based Security & Monitoring: How to Choose?
Agentless refers to a technology or approach that operates without requiring the installation of additional software agents or components on the target systems or devices.
What Is Agentless?
Agentless refers to a technology or approach that operates without requiring the installation of additional software agents or components on the target systems or devices. Agentless architectures are commonly used to deploy security or monitoring systems across distributed systems. This is typically achieved through utilizing remote management protocols or APIs, allowing the management system to access and control the target system remotely.
The advantage of agentless technology is that it can be simpler to implement and maintain, as there is no need to install and manage agents on each device. Additionally, it can also be more secure, as there are fewer components that could potentially introduce vulnerabilities into the system. However, agentless systems have many limitations, including limited real-time monitoring, reduced level of detail, dependency on APIs, and limited automation.
This is part of a series of articles about cloud security.
In this article:
What Is Agentless Security and Monitoring?
Agentless security and monitoring refer to a method of collecting and analyzing security-related information about an environment and its workloads without deploying additional software agents or components. Instead, information is gathered using non-invasive methods, such as through cloud APIs or by processing log files.
Agentless scans take snapshots of resources, assessing the environment through API calls to gather metadata and runtime storage information from the workloads. This information is then processed with machine learning algorithms to build an inventory and analyze the security risks across the environment.
This approach to security and monitoring offers the advantage of low friction, allowing security teams to assess risk and maturity without having to deploy software into the environment. Additionally, because no code is deployed on the workloads, it can also be seen as a more secure and less intrusive method of security monitoring.
Limitations of the Agentless Approach
However, agentless security has some limitations that organizations should be aware of when considering this approach:
- Limited real-time monitoring: Since agentless security relies on non-invasive methods such as cloud APIs or log files, it may not provide real-time monitoring capabilities in the same way that agent-based security does.
- Reduced level of detail: Agentless security may also provide a reduced level of detail compared to agent-based security, as it cannot collect information at the same level of granularity.
- Dependence on APIs and log files: Agentless security relies on the availability and accuracy of APIs and log files, which may not be accessible or up-to-date in all environments.
- Limited Automation: Because agentless security does not have direct access to the devices, it may be more difficult to automate security policies and controls in the same way that agent-based security can.
- Compatibility issues: In some cases, the APIs or log files used by agentless security may not be compatible with all devices or systems, which could limit the scope of the security information that can be collected.
It’s important to carefully consider the limitations of agentless security and weigh them against the specific requirements and priorities of the organization before deciding on this approach.
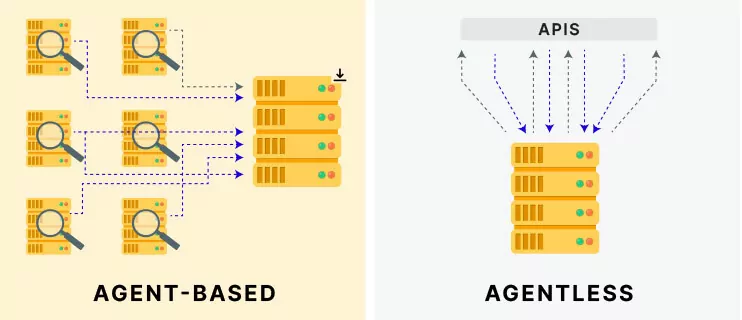
Agentless vs. Agent-Based Security
Agent-based security refers to a method of collecting and analyzing security-related information about an environment and its workloads by deploying software agents on each device or system. The agents continuously monitor and report back security-related data to a central management system.
Pros of agent-based security:
- Provides real-time monitoring and reporting of security-related data.
- Offers more granular and detailed information about the state of the environment and its workloads.
- Can automate and enforce security policies and controls directly on the devices.
- Can be more efficient and effective in detecting and responding to security incidents.
Cons of agent-based security:
- Adds additional software components to the environment, which could introduce vulnerabilities or performance issues.
- Requires additional resources and effort to deploy and maintain the agents on each device.
- Might negatively impact the performance of the devices.
Key differences between agentless and agent-based security:
| Agentless Security | Agent-Based Security | |
| Deployment | No agents or components installed on devices | Software agents deployed on each device or system |
| Data Collection | Non-invasive methods (e.g. APIs, log files) | Agents continuously monitor and report back data |
| Real-time Monitoring | Limited | More detailed and real-time |
| Security | Considered more secure and less intrusive | Potentially less secure due to additional components installed |
| Maintenance | Generally easier to maintain | Requires additional effort to deploy and maintain agents |
| Performance Impact | Generally less intrusive | Potential performance impact on the devices |
| Detail | Limited information and detail | More granular information and detail |
Agent Security vs. Agentless Security: How to Choose?
When choosing between agent security and agentless security, there are several factors to consider:
- Visibility and control: Agent based systems provide a higher level of visibility over endpoint devices and systems.
- Control: An agent-based solution provides more control, can be used to proactively enforce security policies, and keep systems up-to-date with the latest security patches.
- Scalability: Agentless security solutions may be more scalable than agent-based solutions, as they do not require additional software to be installed on each device or system. This can be beneficial in large, distributed environments where managing and maintaining agents on a large number of devices would be challenging.
- Integration: Agent-based solutions may be more easily integrated with other security solutions and systems, as they can provide detailed information about the state of a device or system.
- Resource usage: Agent-based solutions can consume more resources on the endpoint, such as memory and CPU, than agentless solutions. In environments where devices have limited resources, agentless solutions may be more suitable.
- Use case: The specific use case or environment will also play a role in determining which type of solution is more suitable. For example, in environments where devices are not easily accessible, such as in industrial control systems, agentless solutions may be more suitable.
It’s important to evaluate the specific needs and requirements of your organization and to consider the trade-offs between the two types of solutions. It’s also important to note that it’s not an either-or decision, and a combination of both agent and agentless security solutions can also be used to provide a more comprehensive security posture.
Learn more About Vulnerability Management
Open Source Vulnerability Scanning: Methods and Top 5 Tools
Open source vulnerability scanners, often used as part of Software Composition Analysis (SCA) tools, are used to detect open source components used in software projects, and check if they contain unpatched security vulnerabilities, and help organizations remediate them. These tools scan complex dependency trees, because vulnerabilities can be found in a dependent library used by the main component or brought into an application during the build phase. Learn how open source vulnerability scanning works and discover tools that can help you identify and remediate vulnerabilities in OSS components and containers.
Read more: Open Source Vulnerability Scanning: Methods and Top 5 Tools
Trivy Vulnerability Scanner Adopted by Leading Cloud Native Platforms
Trivy is a comprehensive and easy-to-use open source vulnerability scanner for container images. Unlike other open source scanners, Trivy covers both OS packages and language-specific dependencies and is extremely easy to integrate into organizations’ software development pipelines. Trivy vulnerability scanner is being added as an integrated option in the CNCF’s Harbor registry, in GitLab, and in Mirantis Docker Enterprise.
Read more: Trivy Vulnerability Scanner Adopted by Leading Cloud Native Platforms
