Securing Cloud Native Workloads on AWS
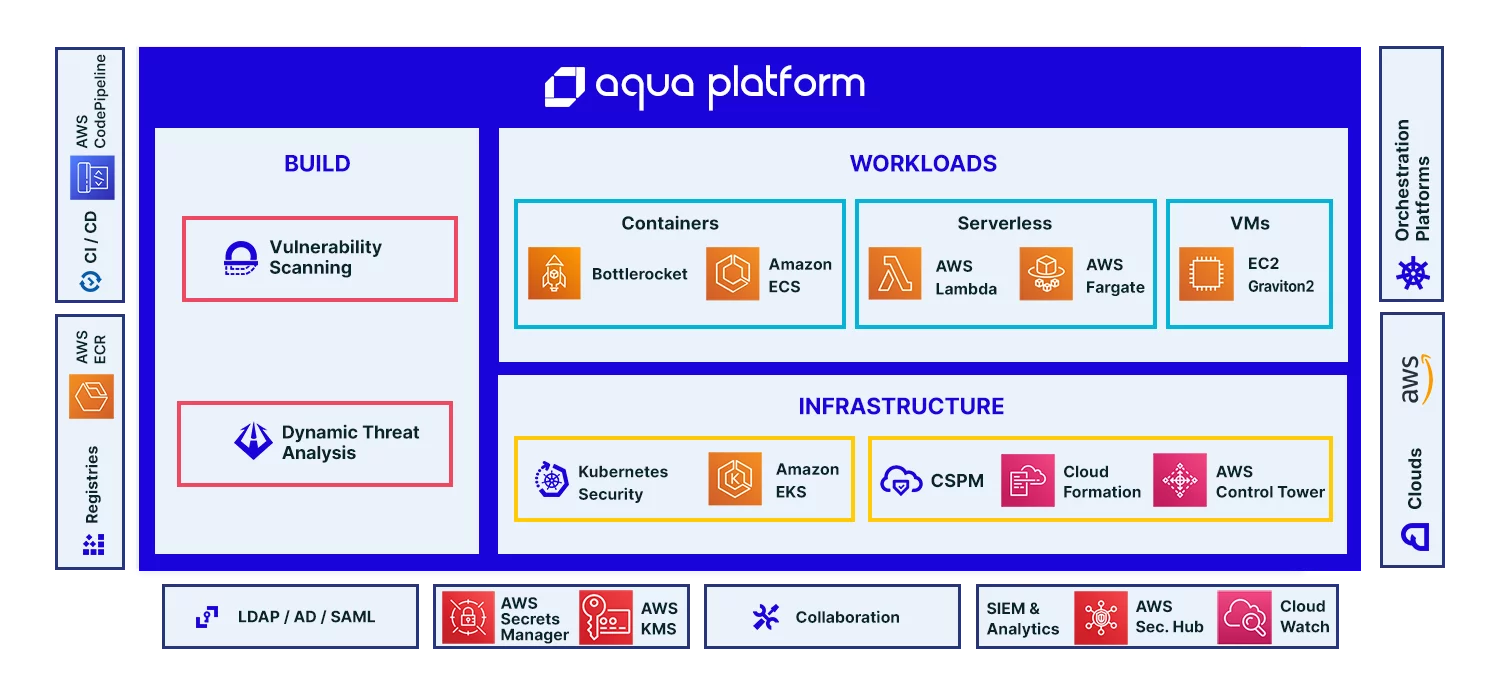
Aqua provides the most complete security solutions to protect workloads running on Amazon ECS, EKS, AWS Fargate and AWS Lambda - including Graviton2-powered workloads.
As an Advanced APN member and Container Competency technology partner, Aqua provides highly-integrated security controls for cloud native applications on AWS, supporting managed container services, such as Amazon ECS for container orchestration, Amazon EKS for Kubernetes-based deployments, AWS Fargate for on-demand container scaling, AWS Lambda for serverless functions, and Amazon ECR for storing and managing container images.
Protect workloads running on
Amazon EKS
Prevent unauthorized images from running in your EKS cluster, enforce container immutability, network segmentation and segregation of duties.
Secure Applications running on AWS Fargate containers
Ensure that workloads running on AWS Fargate - including ECS, EKS and Graviton2-powered workloads - are only performing their intended function, detect vulnerable or compromised containers.
Extend security from Amazon ECR to Amazon ECS
Manage image vulnerabilities, ensure only trusted images can be deployed, automatically whitelist legitimate container behavior, and detect and block suspicious activities.
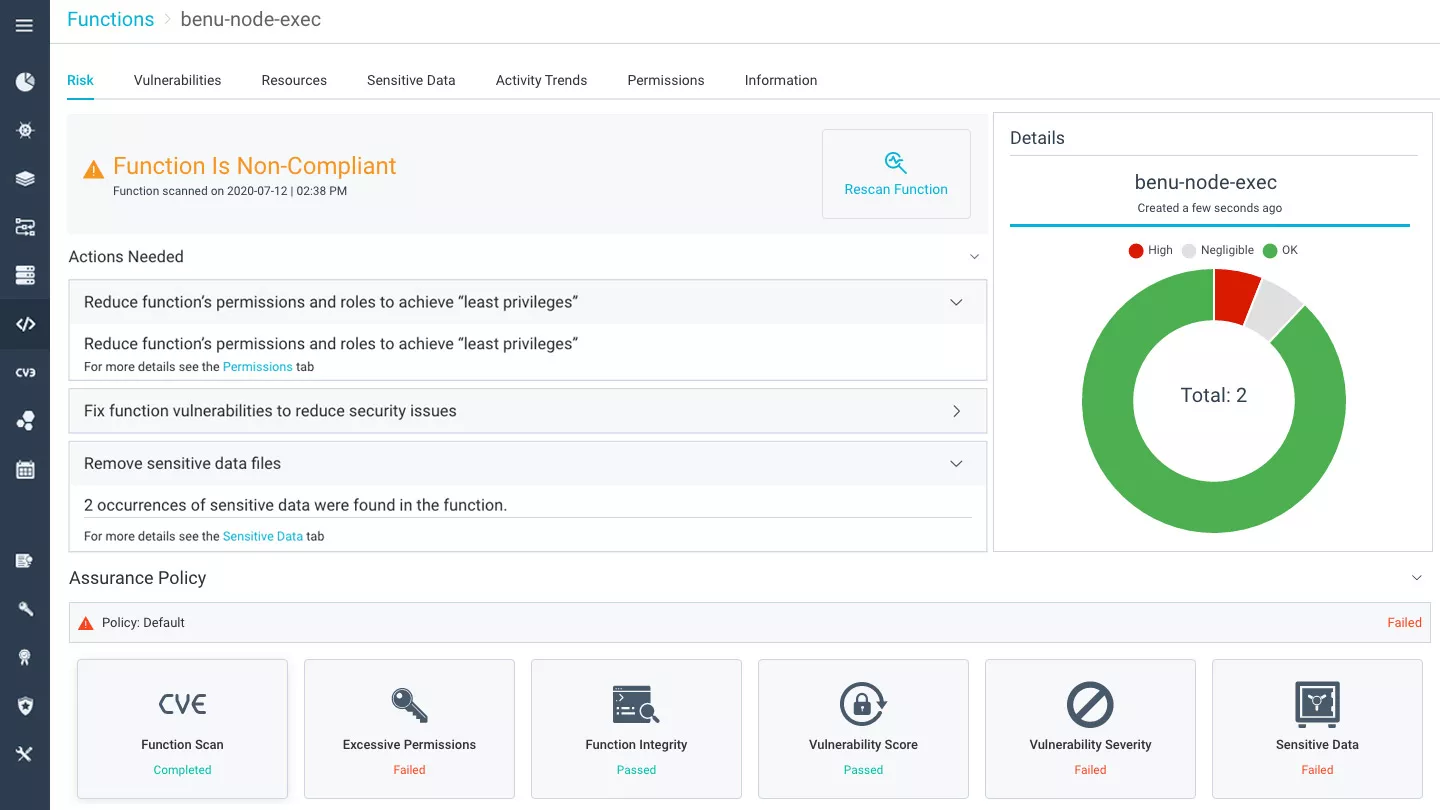
Protect AWS Lambda Functions
Control the risk of AWS Lambda functions by discovering over-provisioned permissions and roles, embedded credentials and keys, and vulnerabilities. Monitor functions at runtime, preventing code injection and malicious activity.
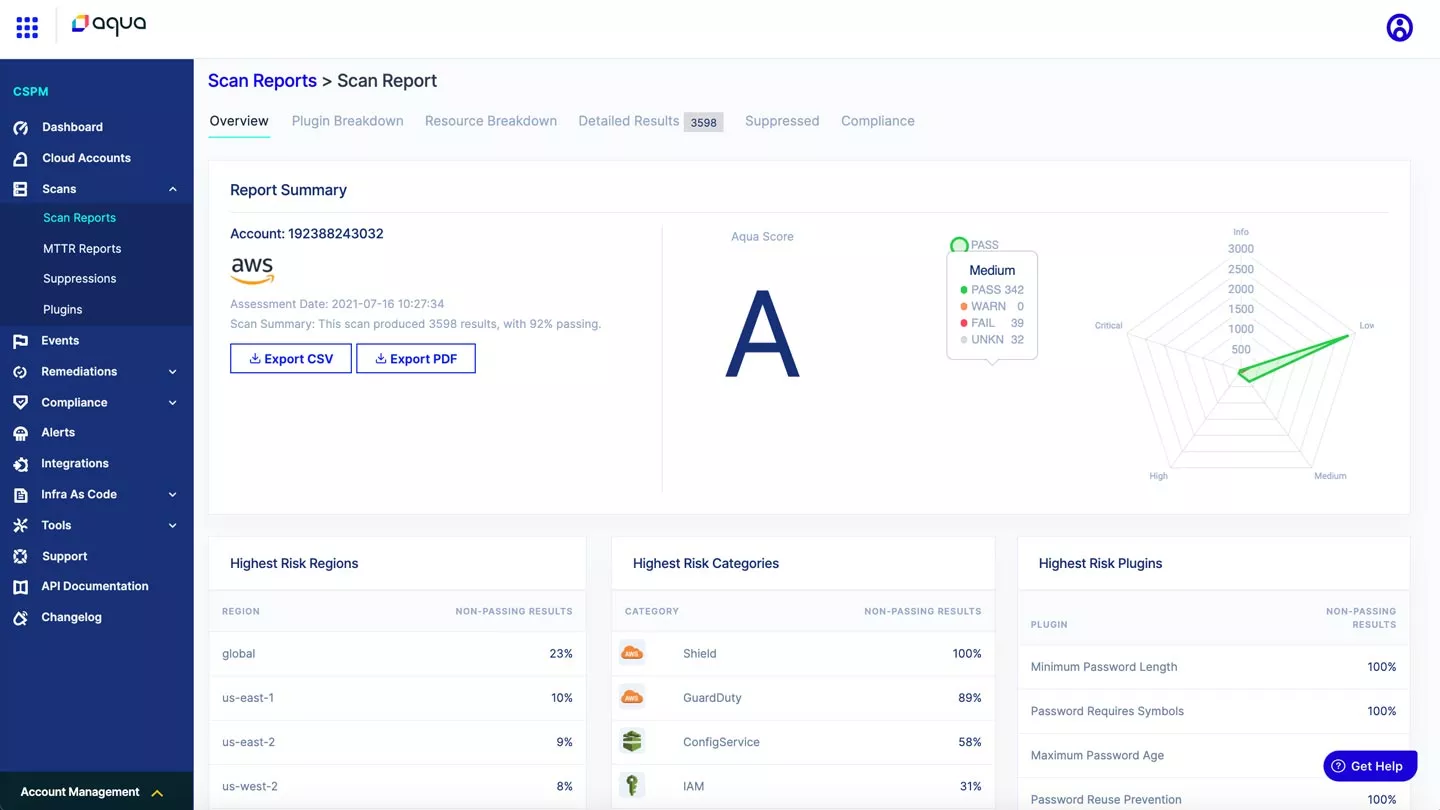
Cloud Security Posture Management (CSPM)
Ensure that your AWS accounts and services are configured according to best practices, including the CIS Foundation Benchmarks for AWS and the AWS Well-Architected Framework. The Well-Architected Framework AWS Management & Governance Lens provides prescriptive guidance on key concepts and best practices for optimizing management and governance across AWS environments, working in tandem with Aqua as an integrated partner solution.
The Integrated Partner Solution
Cloud VM Security and Compliance
Protect workloads running on Amazon EC2 instances and ensure they are properly hardened. Scan for vulnerabilities and malware, apply File Integrity Monitoring (FIM), check configuration against the CIS Benchmark for Linux, and monitor user access and activity. Create command-level audit trail for compliance and forensics.
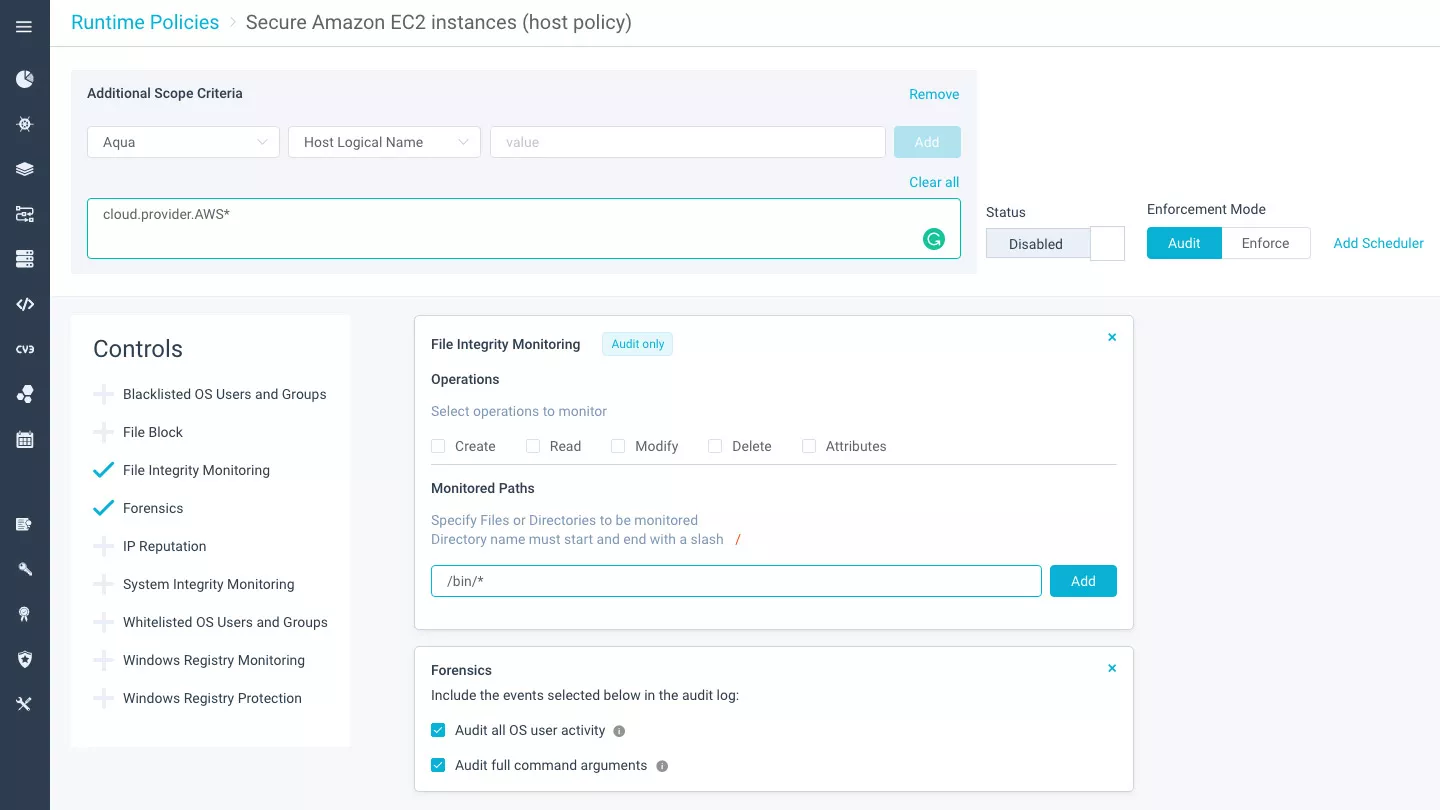
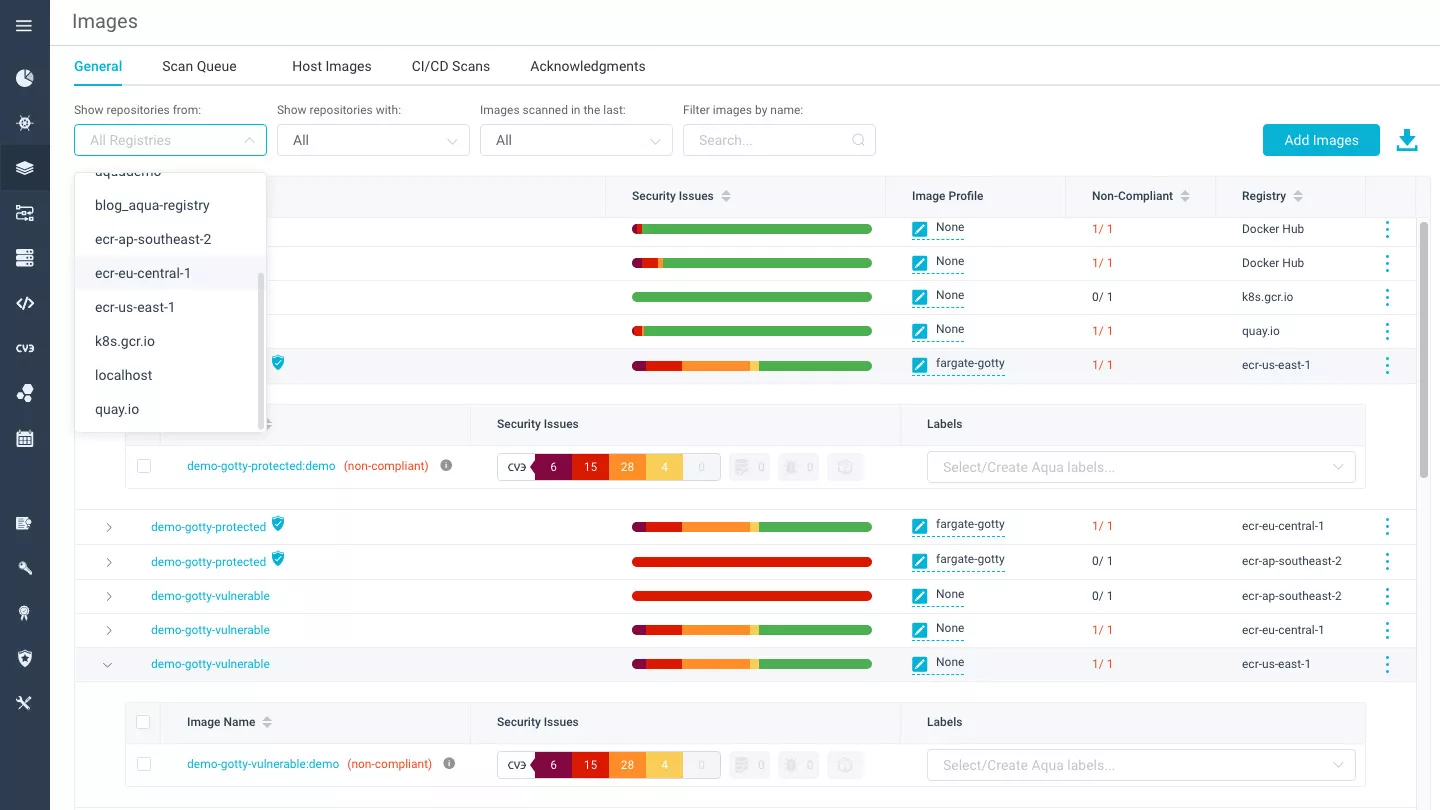
Image Vulnerability
Scanning & Assurance
Prevent unauthorized images from running in your AWS environment. Continuously scan images stored in Amazon ECR to ensure that DevOps teams do not introduce vulnerabilities, bad configurations, or secrets into container images. Get actionable recommendations for remediation of security issues.
Serverless Function Risk assessmentand Mitigation
Continuously scan Lambda functions in AWS accounts to ensure that developers don’t introduce vulnerabilities into function code, leave access keys in environment variables, or create overly permissive roles. Define security policies for AWS Lambda functions and alert or prevent the execution of functions that violate the policies.
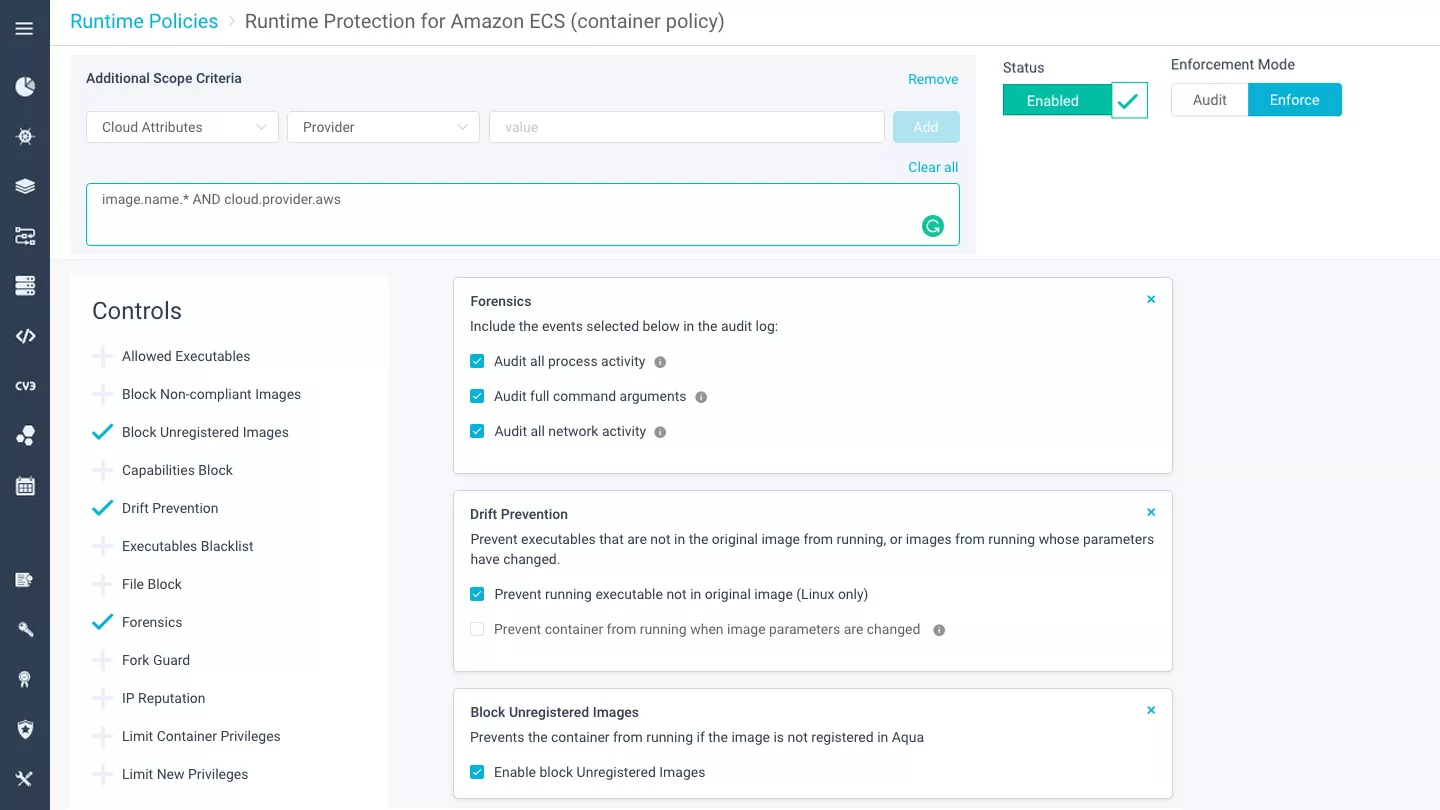
Protect Applications in Runtime
Prevent unvetted containers from running in your Amazon ECS, EKS and Fargate environments. Automatically create security policies based on container behavior and ensure that containers only do what they are supposed to do in the application context. Detect and prevent activities that violate policy, and defend against container-specific attack vectors.
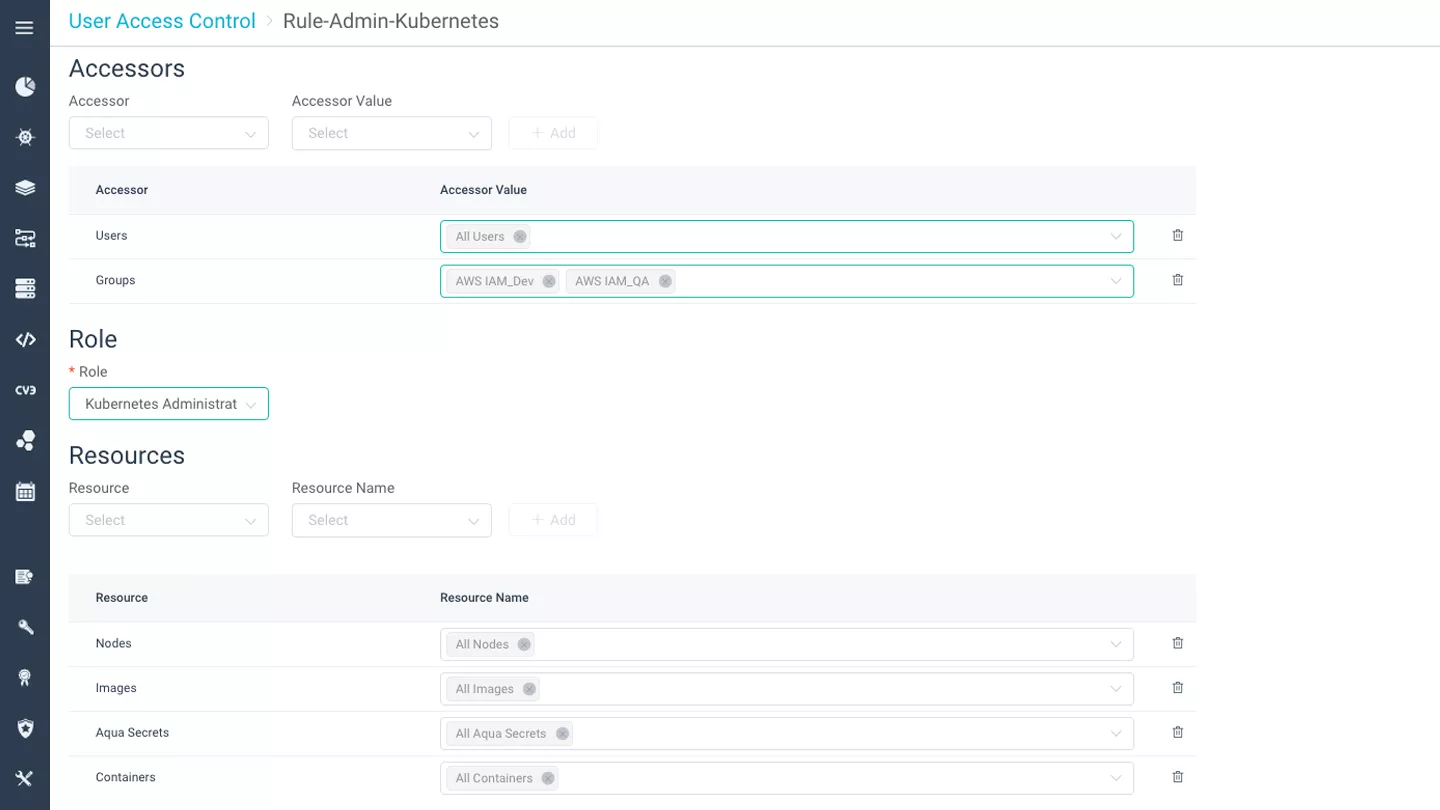
Container-Level RBAC
Apply highly granular access control policies into containers at runtime via integration with AWS IAM roles. Define user access privileges according to role, allowing or preventing specific Docker actions, such as view, run, stop, view logs, and more.
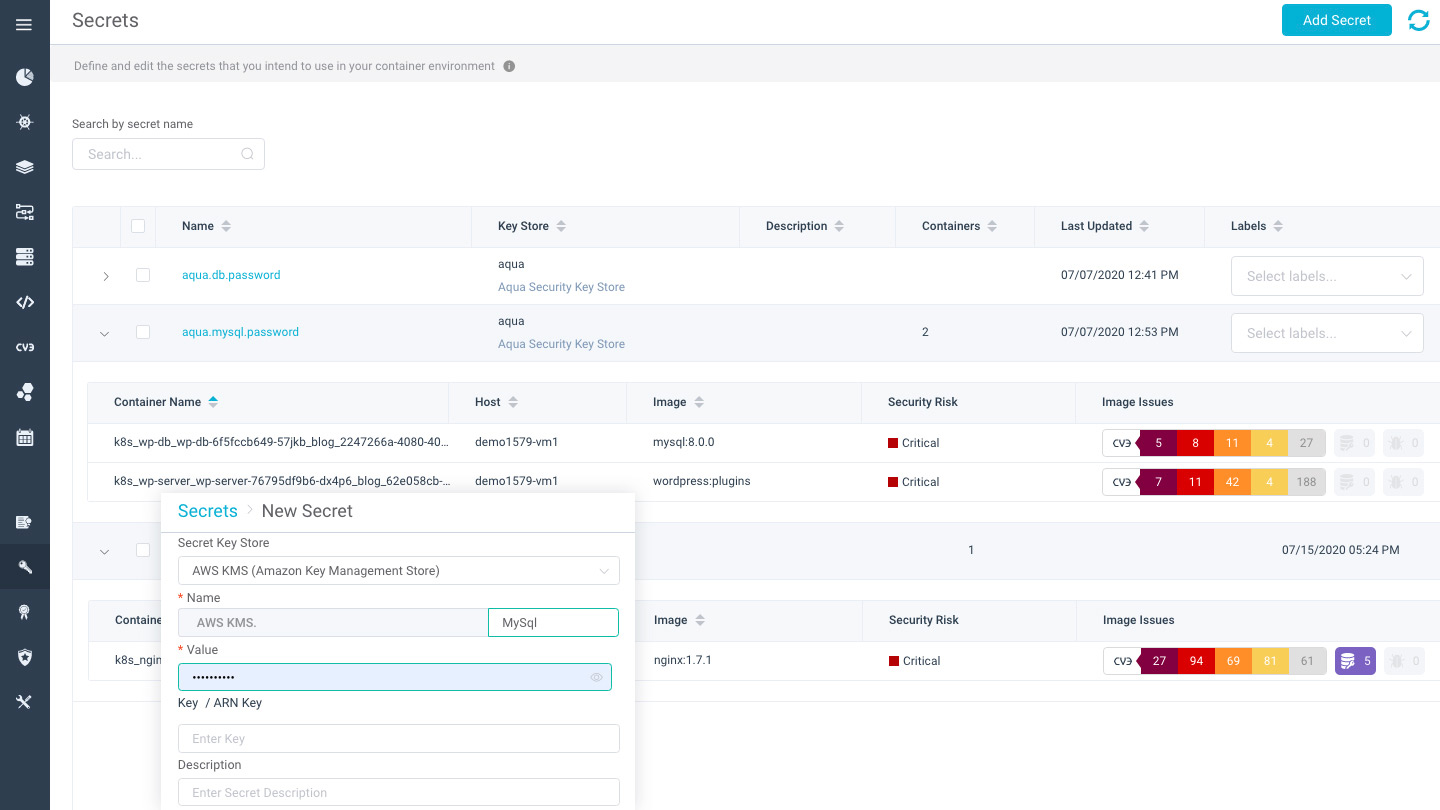
Secrets Management
Leverage AWS KMS (key management store) to securely deploy secrets – such as passwords, keys and tokens – into containers at runtime. Aqua makes it easy to manage, rotate, and revoke secrets in containers with no downtime, running only in memory without persistence on disk.
With Aqua supporting our new AWS Privatelink for AWS Marketplace feature, they have leveraged our newest capability to reduce risk and increase security of data moving between Enterprises and SaaS vendors. We are thrilled to have Aqua enabling security for customers using containers on Amazon Virtual Private Cloud.
The 15 Riskiest AWS Misconfigurations
This white paper delves into the most riskiest configurations and guides teams to help them pinpoint the potential risks in their own environments. The importance of auto-remediation and select examples on best practices for implementing is also covered.
Get the Whitepaper