What Is SSDF (Secure Software Development Framework)?
The National Institute of Standards and Technology (NIST) Secure Software Development Framework (SSDF) is a set of guidelines and best practices for secure software.
What Is SSDF (Secure Software Development Framework)?
The National Institute of Standards and Technology (NIST) Secure Software Development Framework (SSDF) is a set of guidelines and best practices for designing, developing, and maintaining secure software. These typically include guidelines for secure coding, threat modeling, vulnerability management, and incident response, among other areas. They may also include specific requirements for compliance with regulatory standards or industry best practices.
The SSDF standard was created as a result of the President’s Executive Order (EO) on “Improving the Nation’s Cybersecurity (14028).” NIST created the standard to improve the cybersecurity posture of federal agency cybersecurity in line with the EO.
The goal of the SSDF is to help organizations create software that is less susceptible to security breaches and vulnerabilities. The NIST SSDF version 1.1 was produced in response to the 2021 executive order to strengthen cybersecurity across the United States. It establishes standardized terminology for software security.
This is part of a series of articles about software supply chain security.
In this article:
How Can the NIST SSDF Benefit Software Security?
The framework can benefit software security in a number of ways:
- Structure: The NIST SSDF provides a structured approach to software development that can help organizations identify and mitigate security risks throughout the development process.
- Industry standards: The NIST SSDF aligns with industry standards and best practices, so organizations can be confident that they are following established guidelines for secure software development.
- Compliance: The NIST SSDF can help organizations comply with regulatory requirements for software security, such as those imposed by the Federal Risk and Authorization Management Program (FedRAMP) and the Health Insurance Portability and Accountability Act (HIPAA).
- Risk management: The NIST SSDF provides a comprehensive framework for managing risk throughout the software development lifecycle.
- Improving the security of software: By following the NIST SSDF, organizations can improve the security of their software by identifying and addressing potential vulnerabilities and threats early in the development process.
SSDF Sections
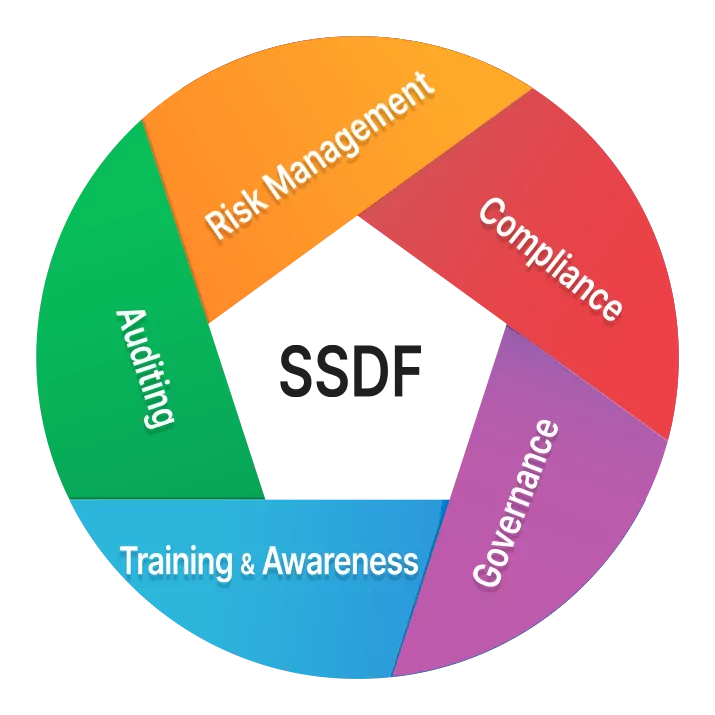
The framework includes sections on the following objectives.
Preparation
The NIST Secure Software Development Framework (SSDF) includes a section on “Preparing the Organization” which focuses on establishing the necessary policies, procedures, and practices for secure software development. This section covers several key areas, including:
- Governance: The overall governance of software development within the organization, including roles and responsibilities, decision-making processes, and oversight of software development activities.
- Risk management: The processes and procedures for identifying, assessing, and mitigating risks throughout the software development lifecycle.
- Compliance: The requirements for compliance with relevant regulatory standards and best practices, such as those imposed by the Federal Risk and Authorization Management Program (FedRAMP) and the Health Insurance Portability and Accountability Act (HIPAA).
- Training and awareness: The training and awareness programs that need to be in place to ensure that all software development personnel are aware of the organization’s secure software development policies and procedures, and are equipped to develop software in accordance with those policies and procedures.
- Auditing: The processes and procedures for auditing software development activities to ensure that they are in compliance with the organization’s secure software development policies and procedures.
Protection
The SSDF includes a section on “Protecting the Software” which focuses on the technical measures and controls that organizations can use to protect their software. This section covers several key areas, including:
- Secure coding: The principles and practices of secure coding, including best practices for writing secure code, identifying and addressing common vulnerabilities, and testing for security.
- Threat modeling: The process of identifying, assessing, and mitigating potential threats to the software.
- Vulnerability management: The process of identifying, assessing, and mitigating known vulnerabilities in the software.
- Incident response: The planning and preparation for responding to security incidents, including incident response procedures and incident response teams.
- Security testing: The different types of security testing that should be performed on software, such as penetration testing, vulnerability scanning, and security code reviews.
Secure Software Production
The SSDF includes a section on “Producing Well-Secured Software” which focuses on the processes and procedures for developing software in a secure manner. This section covers several key areas, including:
- Secure software development life cycle (SDLC): The secure software development life cycle, which includes the phases of software development and the security-related activities that should be performed during each phase.
- Secure requirements: The process of gathering and defining secure software requirements and how to ensure that the requirements align with the organization’s security policies and standards.
- Secure design: The process of designing secure software and the design principles that should be followed to ensure that the software is secure. The software settings must be secure by default.
- Secure implementation: The process of implementing secure software and the best practices for writing secure code.
- Secure verification: The process of verifying that the software is secure and the different types of security testing that should be performed on software.
- Secure deployment: The process of deploying secure software and the security-related activities that should be performed before, during, and after deployment.
Vulnerability Response
The NIST SSDF includes guidance on responding to vulnerabilities in software systems. The framework advises organizations to establish a vulnerability management process that includes the following steps:
- Identification: Detecting and identifying vulnerabilities in software systems, including through the use of tools such as vulnerability scanners and penetration testing.
- Prioritization: Assessing the risk posed by each vulnerability, taking into account factors such as the likelihood of exploitation and the potential impact.
- Remediation: Developing and implementing a plan to address the vulnerabilities, including patching or upgrading software, implementing workarounds, or taking other steps to mitigate the risk.
- Verification: Testing and validating that the vulnerabilities have been successfully addressed.
- Communication: Communicating vulnerabilities and remediation actions to stakeholders, including customers, partners, and other interested parties.
The framework also recommends that organizations establish an incident response plan to handle security incidents and vulnerabilities that cannot be addressed through the vulnerability management process.
