Kubernetes Security Posture Management (KSPM)
Kubernetes, the open source container orchestration platform, is a complex system that is subject to specialized security risks – such as misconfigured Kubernetes Role-Based Access Control (RBAC) policies, insecure container images, and Kubernetes runtime vulnerabilities, to name just a few. Conventional application security and cloud security tools don’t address all of these risks.
This is why investing in a capability such as Kubernetes Security Posture Management (KSPM) is crucial for organizations that deploy applications using Kubernetes. Keep reading for details on what KSPM means, why it’s important, how Kubernetes security relates to cloud and container security, and best practices for getting the most out of KSPM.
Kubernetes Security Posture Management (KSPM): An overview
Kubernetes Security Posture Management (KSPM) refers to the set of business tools used to secure Kubernetes workloads and clusters in a comprehensive way. These solutions are specifically tailored to address the unique security challenges of Kubernetes environments, which differ significantly from traditional or general-purpose IT systems.
The main purpose of KSPM is to help ensure that Kubernetes-based resources are as secure as possible, by continuously monitoring, identifying, and remediating risks.
Why is KSPM important for cybersecurity?
When deploying workloads using Kubernetes, you face certain unique security risks that other solutions aren’t always effective in detecting, such as:
- Misconfigured RBAC: Kubernetes has a built-in Role-Based Access Control (RBAC) system to manage access rights within clusters. Misconfigurations in RBAC policies could cause security risks like allowing a user to access data or applications owned by other users.
- Insecure management of Kubernetes secrets: If passwords, access keys, and other secrets aren’t stored and managed securely, they could become available to threat actors, leading to security breaches.
- Malware in container images: Applications deployed in Kubernetes are based on container images, which could contain malware.
- Container runtime vulnerabilities: Kubernetes relies on a runtime to execute containers. Attackers could exploit vulnerabilities within the runtime to take control of applications or, in extreme cases, an entire Kubernetes cluster.
- Node security flaws: Kubernetes clusters consist of nodes, which are individual servers that host workloads (or, in the case of control plane nodes, host the core Kubernetes software). Vulnerabilities in the operating systems on the nodes could become vectors of attack against clusters.
- Pod Security Misconfigurations: Pods, the smallest deployable units in Kubernetes, can be misconfigured to allow unnecessary privileges or network access. For instance, allowing a pod to run as a privileged user can expose the host system to compromise.
- Network Policy Gaps: Kubernetes clusters often lack well-defined network segmentation policies, leaving workloads vulnerable to lateral movement attacks where attackers compromise one component and move to others within the cluster.
- Unmonitored Kubernetes API Activity: The Kubernetes API server is a critical control point for cluster operations. Without proper monitoring, unauthorized access or suspicious activity targeting the API may go unnoticed.
- Supply Chain Attacks: Kubernetes clusters rely heavily on third-party components, such as Helm charts, custom operators, or open-source libraries. These dependencies can introduce vulnerabilities or malicious code if not properly vetted.
Again, traditional security tools don’t always catch all of these risks. Not all application vulnerability scanners can scan containers, for example, and tools designed to detect misconfigurations in generic cloud Identity and Access Management (IAM) policies typically don’t analyze Kubernetes RBAC policies for potential risks.
How KSPM works
Kubernetes Security Posture Management (KSPM) operates by continuously monitoring, analyzing, and auditing the state of Kubernetes clusters and their workloads to detect potential risks, misconfigurations, and compliance issues. It ensures the security of Kubernetes environments by implementing automated checks and providing actionable insights for remediation.
Here’s a more detailed breakdown of how KSPM tools function:
- Cluster Configuration Scanning: KSPM tools examine Kubernetes cluster configurations, including control plane components, worker nodes, and networking policies, for example they compare these configurations against industry best practices, such as the CIS Kubernetes Benchmarks.
- Role-Based Access Control (RBAC) Analysis: Kubernetes RBAC settings are a frequent source of vulnerabilities.
- Container Image Scanning: KSPM tools inspect container images used in workloads for vulnerabilities, misconfigurations, or malicious code by comparing them against vulnerability databases like CVE or NVD.
- Kubernetes Object Validation: KSPM tools assess Kubernetes objects (e.g., pods, deployments, services) to ensure they meet security requirements.
- Compliance Auditing: Organizations must adhere to regulatory and internal compliance standards.
- Runtime Monitoring and Threat Detection: Some KSPM tools extend their functionality to monitor Kubernetes clusters at runtime.
- Automated Policy Enforcement: KSPM tools help enforce security policies by integrating with Kubernetes admission controllers to block non-compliant workloads at deployment.
- Visualizations, Alerts, and Reporting: KSPM tools generate alerts, detailed reports, and visual dashboards to provide real-time visibility into the security posture of Kubernetes environments.
KSPM tools operate via agent-based/agentless scanning, integration into CI/CD pipelines for pre-deployment security checks, and enforcement of custom policies using frameworks like Open Policy Agent (OPA) and Gatekeeper. Many tools provide preconfigured policies or allow administrators to create custom policies using policy definition languages like Rego, ensuring robust and adaptable Kubernetes security.
KSPM vs. CSPM
If we consider that any Security Posture Management (SPM) solution in general has three core capabilities—Discovery, Policy Enforcement, and Compliance—the differences between Kubernetes Security Posture Management (KSPM) and Cloud Security Posture Management (CSPM) lie in their scope and focus. While CSPM targets the broader security needs of cloud infrastructure, KSPM is specifically tailored to address the unique challenges of securing Kubernetes clusters and workloads. Both solutions complement each other to provide comprehensive security for modern cloud-native environments.
| Capability | KSPM (Kubernetes Security Posture Management) | CSPM (Cloud Security Posture Management) |
| Discovery | Identifies Kubernetes-specific risks, such as misconfigured RBAC, pod security settings, and container image vulnerabilities. | Detects misconfigurations in cloud environments, such as open storage buckets, insecure IAM roles, and exposed VMs. |
| Policy Enforcement | Enforces Kubernetes-specific policies, including admission controls, pod security policies, and workload runtime restrictions. | Implements cloud-focused policies, such as restricting public IP exposure and enforcing encryption. |
| Compliance | Aligns Kubernetes configurations with frameworks like CIS Kubernetes Benchmarks and custom policies. | Ensures cloud environments meet compliance standards such as PCI DSS, GDPR, or ISO/IEC 27001. |
This comparison highlights how KSPM and CSPM address different layers of security while sharing common foundational principles. Together, they provide a holistic approach to securing cloud-native and containerized infrastructure.
What to look for in a KSPM solution
KSPM is a broad category, and KSPM tools vary in functionality, without the 3 core capabilities previously mentioned, the best solutions should deliver the following:
- Integration with CI/CD Pipelines: Seamlessly integrates with CI/CD tools to identify security issues early, enforcing compliance before deployment.
- Runtime Monitoring and Threat Detection: Continuously monitors Kubernetes clusters for anomalies and suspicious activities, ensuring real-time threat detection and response.
- Scalability and Multi-Cluster Support: Manages security across multiple Kubernetes clusters, supporting both on-premises and cloud-based environments at scale.
- User-Friendly Dashboards and Reporting: Provides intuitive dashboards and detailed reports to visualize security posture, compliance, and trends over time.
- Integration with Broader Security Ecosystems: Connects with CSPM, SIEM, and SOAR tools to deliver a unified, organization-wide security posture.
- Threat Intelligence Integration: Leverages threat intelligence feeds to proactively identify known exploits and vulnerabilities across Kubernetes environments.
- Automation and Orchestration: Automates remediation of misconfigurations and orchestrates workflows to minimize manual intervention and improve efficiency.
- Open-Source Tooling Support: Supports tools like kube-bench and kube-hunter, offering flexibility for integrating open-source solutions into security workflows.
Emerging trends in Kubernetes security and integration with AI/ML for threat detection
Going a step further, modern KSPM tools may also integrate advanced features, such as the ability to detect threats using AI/ML. This is valuable not just because it adds efficiency and scalability to threat detection, but also because it can help to identify complex threats that humans might struggle to catch manually – but that AI can detect by quickly parsing large volumes of data and discovering nuanced anomalies.
KSPM best practices
To get the most out of KSPM, consider the following most important best practices:
- Enforce Role-Based Access Control (RBAC): Properly configured RBAC policies are foundational for securing Kubernetes clusters by restricting access and implementing least privilege principles.
- Regularly Audit Kubernetes Configurations: Continuously scanning configurations with tools like kube-bench ensures alignment with best practices (e.g., CIS Benchmarks) and helps identify misconfigurations early.
- Scan Container Images: Scanning container images for vulnerabilities prevents insecure workloads from being deployed, reducing the risk of exploitation during runtime.
- Monitor Runtime Activity: Runtime monitoring detects anomalies and suspicious behavior, enabling real-time threat detection and response to minimize potential damage.
- Adopt a Shift-Left Security Approach: Integrating KSPM into CI/CD pipelines helps identify and address security issues early, making remediation faster and less costly.
- Secure Secrets Management: Proper secrets management, such as encrypting sensitive data and using solutions like HashiCorp Vault, prevents unauthorized access to critical information.
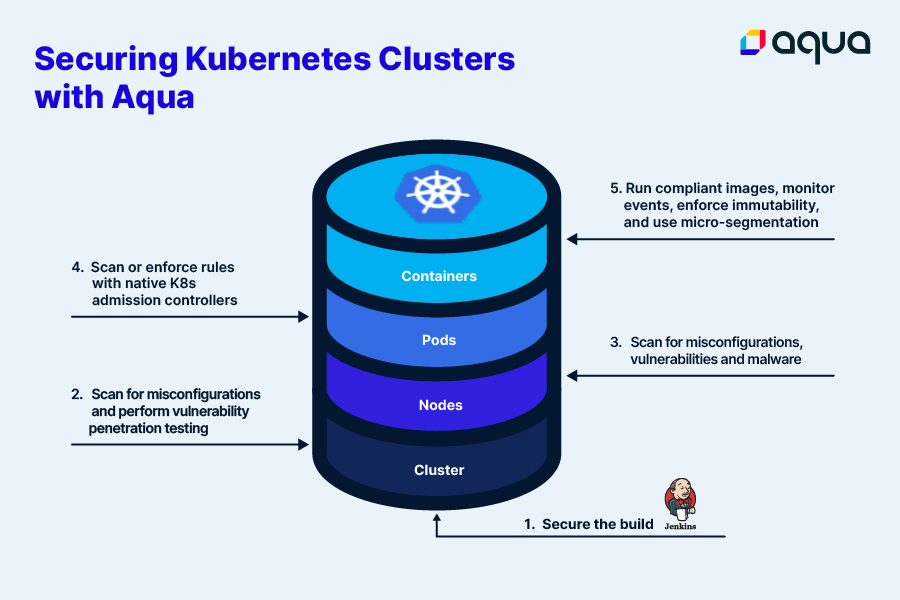
Aqua as a KSPM solution
Aqua was built from the start to help businesses secure cloud-native platforms like Kubernetes. As a holistic Kubernetes security solution, Aqua automatically detects risky configurations, scans workloads, and monitors Kubernetes runtime environments to keep all aspects of your cluster safe. And, because Aqua also offers CSPM and application security capabilities, it provides an end-to-end solution that keeps your entire environment secure – including but not limited to Kubernetes clusters.
