Automate DevSecOps: security and speed without compromise
“Shift left” security early into the DevOps pipeline, accelerating application delivery and removing obstacles to digital transformation
Aqua enables organizations to automate secure development and deployment of applications in their DevOps pipelines, by embedding comprehensive security testing and powerful policy-driven controls early on -- all fully automated.
Scanning and Dynamic Analysis
Comprehensively scans container images and serverless functions for known vulnerabilities, embedded secrets, OSS licensing issues, hidden malware, and configuration issues.
Continuous Image Assurance
Prevents unapproved images and functions from being deployed in your environment, preempting operational errors, image sprawl, and rogue deployments - based on your policies.
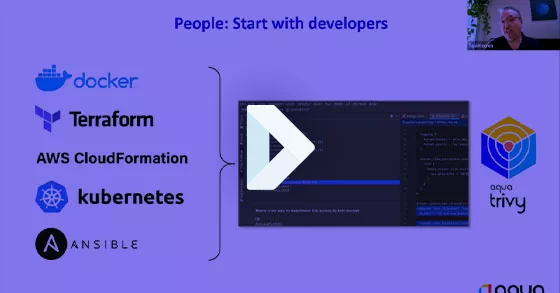
CI/CD Integration
Natively integrates with Jenkins, Azure DevOps, Bamboo, GitLab, TeamCity, and more, to scan images as they are built, providing actionable feedback to developers within their CI tools.
Collaborative Remediation
Provides real-time actionable information on vulnerability and configuration remediation, fed back to developers within their CI/CD tools, sent via Slack, or as a ticket in Jira.
Centralized Secrets Management
Leverages your existing secrets vaults to securely deliver, update, and rotate secrets in containers with no container restart, and no exposure outside the container, both in transit and at rest.