Unified Cloud Security
Accelerate secure innovation and protect your entire development lifecycle from code to cloud and back.
Dev Security
Cloud Security
One Platform
Secure your weakest software supply chain links
Prevent security risks from becoming security incidents by discovering and remediating vulnerabilities, malware, exposed secrets and other risks in your code, build tools, and delivery pipelines.
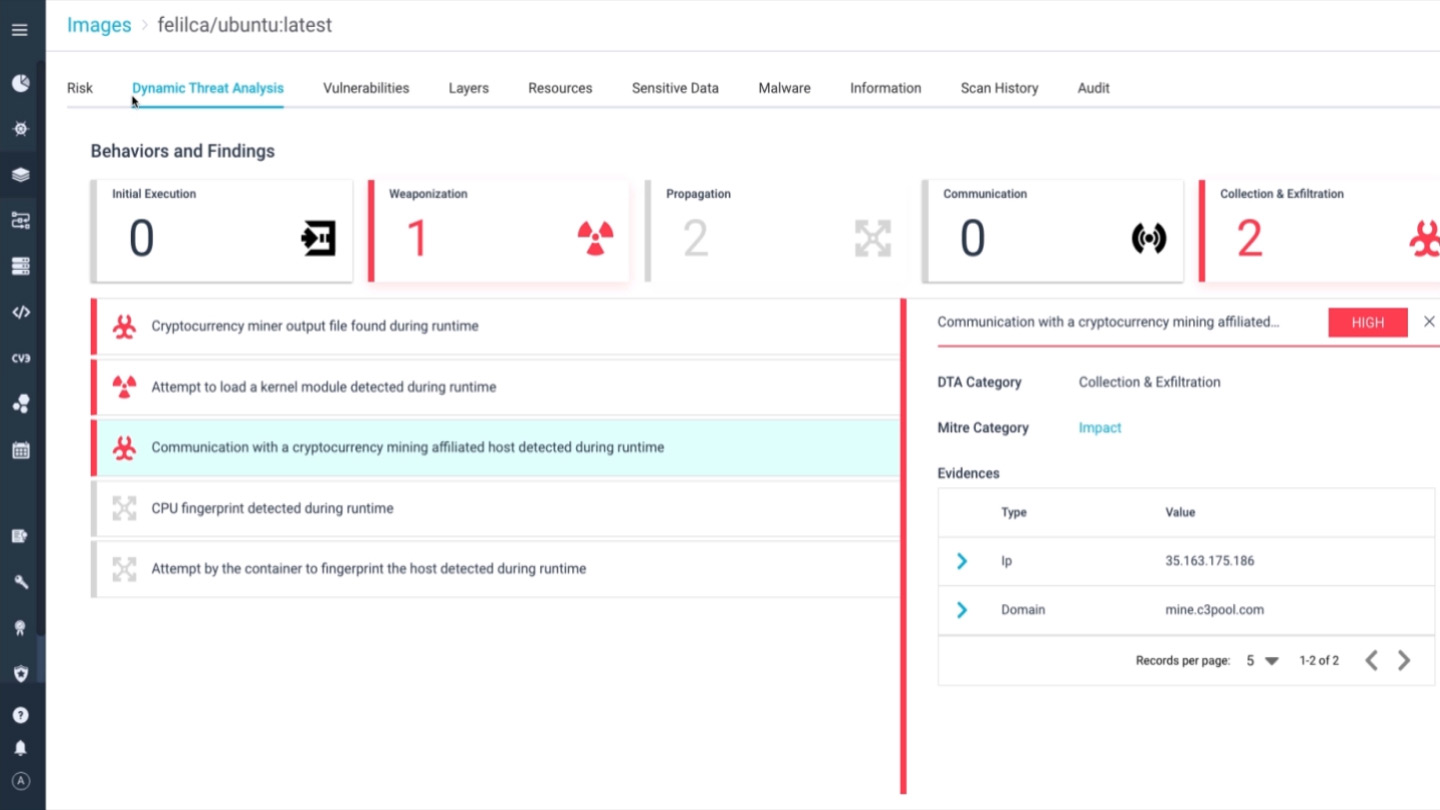
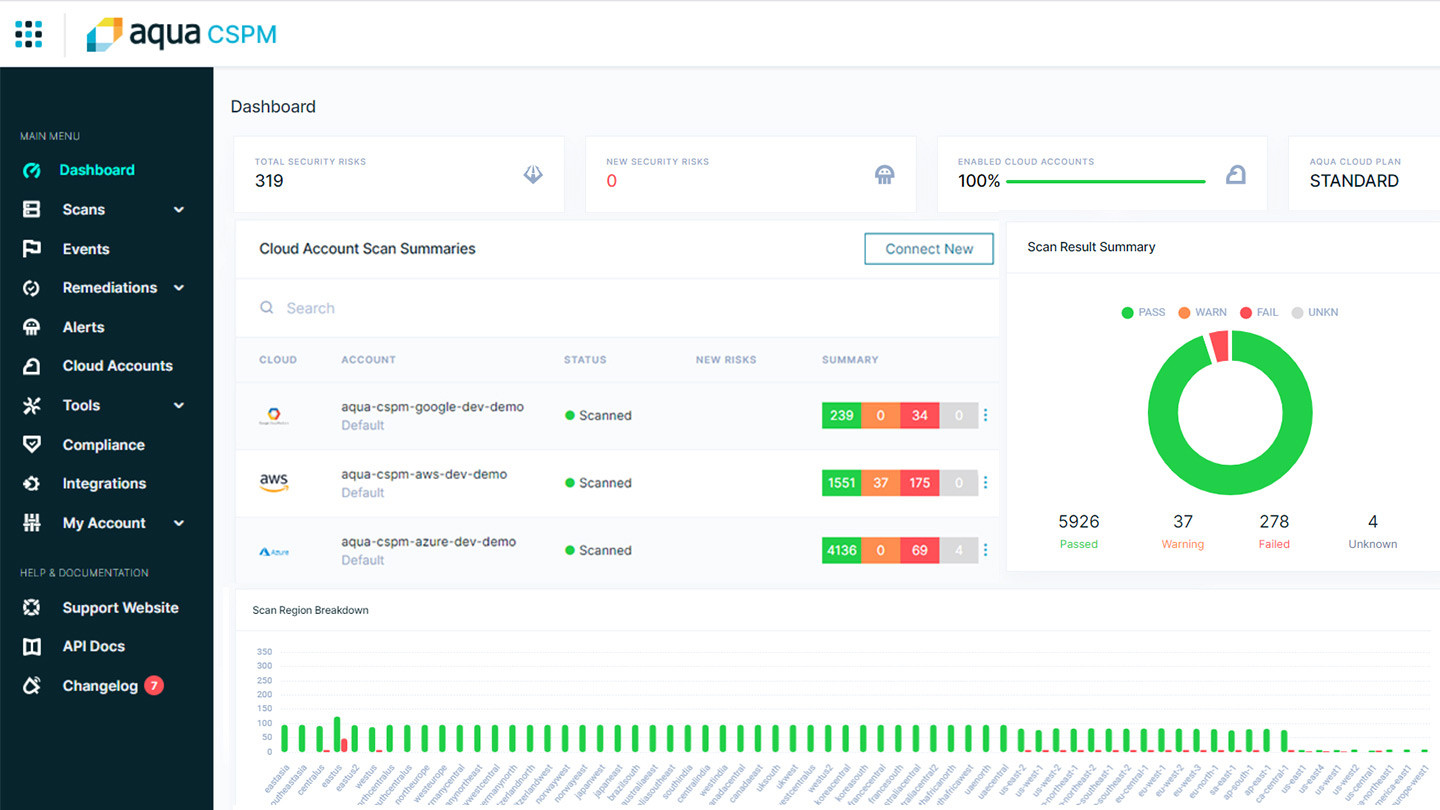
Quickly detect, prioritize and mitigate your biggest cloud security risks
Gain complete visibility into your multi-cloud environment to find and fix misconfigurations and other risks that leave you exposed. Stop known and zero-day attacks in real time.
Bring teams together, regain visibility and reduce your risk
Enable seamless collaboration across teams, eliminate cloud native blind spots, and prevent successful attacks using one source of truth across the entire software development lifecycle (SDLC).
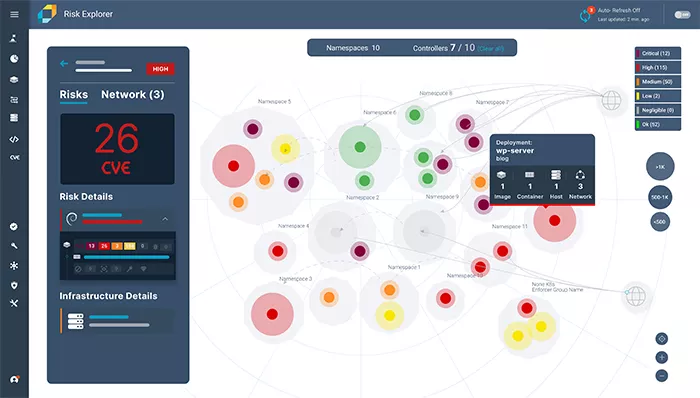
See everything
You can’t secure what you can’t see. With Aqua, discover every resource and risk across your entire development lifecycle. The platform empowers you to truly understand your security posture, make better security decisions, and confidently report compliance to auditors and management.
Aqua Cloud Security Platform
Accelerate secure innovation and protect your entire development lifecycle from dev to cloud and back
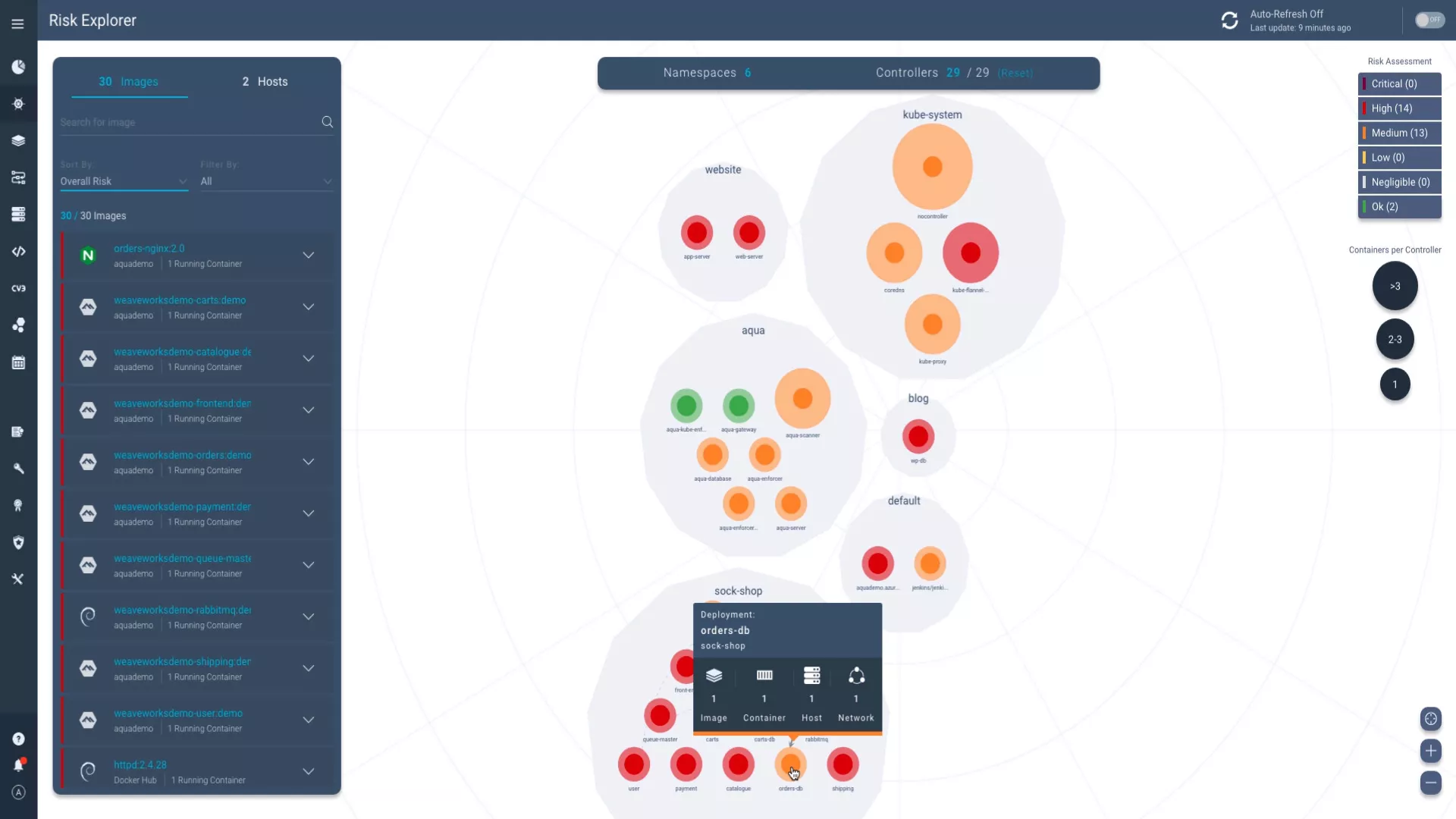
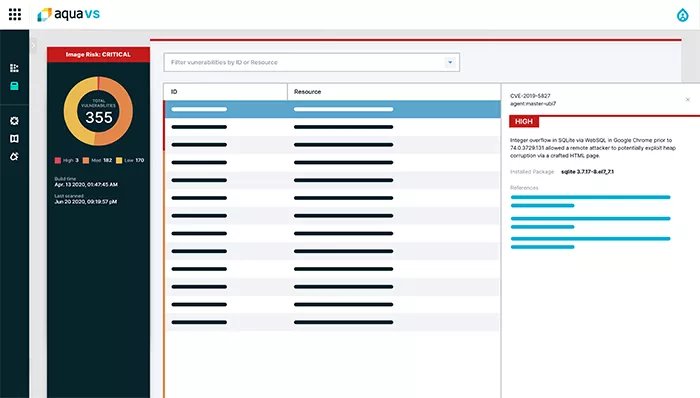
Prioritize what’s most important
Staring at a never-ending list of vulnerabilities, misconfigurations, and other risks is daunting. Understand where you’re truly vulnerable to attack and focus on what matters by combining data sources across the Aqua platform to gain risk-based insights.
The freedom to run anywhere
Aqua secures your applications wherever you develop and run them
Across clouds, container and serverless platforms, CI/CD pipelines, registries, DevOps tools and modes of deployment, orchestrators, all the way to Security, SIEM, and Analytics.
CI/CD
Registries
Container & Serverless
Cloud Providers
Security Tools
Prove you are compliant
Compliance doesn’t have to be difficult to achieve or maintain. You can continually audit your security posture and map findings onto compliance frameworks like PCI, SOC2, and dozens more that are built into the Aqua platform.
Aqua Platform
”Aqua articulated a vision and path forward for the cloud native security market that set them apart from competitors.”
Kellen Dunham, CTO
AIB, Inc.
AIB, Inc.
Trivy Vulnerability Scanner
”Trivy takes container image scanning to higher levels of usability and performance. It is the perfect complement to Harbor”
Michael Michael, Harbor maintainer and Director of Product Management
VMware
VMware