New release of Aqua’s cloud native security platform addresses the needs of large enterprise deployments with runtime visibility and multi-application, multi-team policy management
BOSTON – November 13, 2018 – Aqua Security, the leading platform provider for securing container-based and cloud native applications, today announced version 3.5 of its cloud native security platform, which now protects a wide range of cloud native technologies, including applications using serverless functions. Customers can deploy end-to-end security to establish a consistent policy enforcement layer spanning containers, serverless containers (such as AWS Fargate) and serverless functions (such as AWS Lambda).
In addition, driven by continued enterprise adoption of the Aqua platform in some of the largest global enterprises, Aqua CSP v3.5 raises the bar in terms of ease of management of complex, multi-application and multi-team enterprise environments by enabling flexible policy scopes and highly granular user role definitions, and adds container encryption for protection of intellectual property.
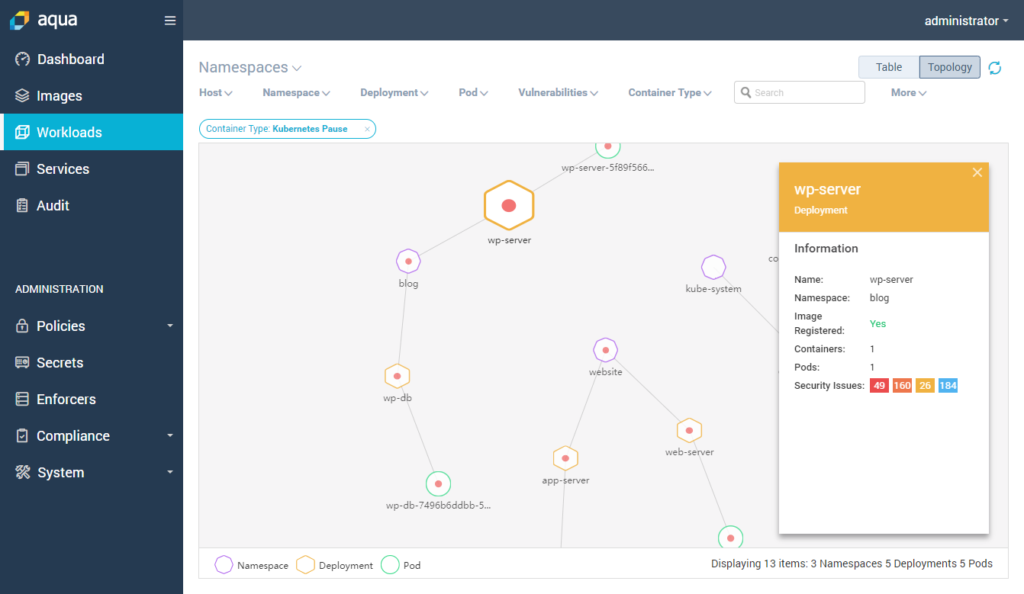
The new Aqua Workloads Explorer topology view, showing the security posture of a Kubernetes cluster
Moving to a serverless model allows developers to prioritize simplicity and agility by abstracting infrastructure concerns to provide a straightforward execution environment for applications and microservices. However, serverless architectures also introduce new security risks. Attackers may leverage a weakness or vulnerability in the serverless function code itself or outsourced libraries; or attempt to take advantage of the complexity of cloud infrastructure permissions to reach services or networks that contain sensitive information. Building on Aqua’s experience in securing containers, Aqua CSP v3.5 addresses these serverless threat vectors and minimizes their potential impact.
“As the adoption of containers and serverless continues to expand within a greater number of enterprises, and to greater numbers of applications within those enterprises, there is a growing need for scalable security that is easy-to-manage across multi-cloud and hybrid cloud deployments, covering both containers and serverless functions,” said Amir Jerbi, CTO and co-founder of Aqua Security. “Our customers now run multiple cloud native applications, and require a unified platform to manage security across teams, while providing security and DevOps teams segregation of duties coupled with the control they require.”
The new features and capabilities Aqua CSP v3.5 introduces include:
- Risk Assessment for Serverless functions: Checks functions for known vulnerabilities, embedded secrets (keys and tokens), and cloud permissions, to ensure that function privileges are secure and minimized. Serverless support is fully integrated with Aqua’s extensive controls for container runtime deployments and is managed via the same console.
- Container Encryption: Aqua now makes it possible to encrypt the entire contents of a container image, decrypting it with a key when it is instantiated as a container. This feature enables companies with sensitive intellectual property embedded in their container images to protect them against unauthorized use, and prevents unauthorized access to code in case of a registry breach, or when code is given under license to partners and customers.
- Greater Visibility through Workload Explorer: With a tabular and visual view of running workloads on Kubernetes and Docker environments, Workload Explorer provides visibility into large, distributed runtime environments, highlighting vulnerable or risky components (i.e., namespaces, deployments, pods, containers). Operations and security staff can easily filter the data and drill down to view detailed information quickly to ensure compliance.
- Contextual Runtime Policies: Based on feedback from some of Aqua’s largest customer implementations, Aqua runtime security policy models now allow the definition of a highly specific scope for each policy, to be applied to an application context. The scope can be defined according to dozens of parameters, including Kubernetes deployment and namespace, image registry prefix, environment variables, and many more. This flexibility allows customers to easily differentiate between multiple applications, for example by applying stricter policy to applications with higher trust requirements, such as mission critical applications, even if they use the same images as other applications.
- Fine-Grained Administrative Access Control: An enhanced RBAC engine enables fine-grained permissions for DevOps, security and compliance teams on the Aqua platform, enabling true segregation of duties between teams and roles. For example, different teams may be granted access to different sets of images or registries, while their ability to view or change Aqua policies for images, serverless functions, runtime, secrets, and compliance will vary according to their specific role.
Availability: Aqua CSP v3.5 will be generally available at the end of November, and will be demonstrated at DockerCon Europe in Barcelona, booth S20, and at KubeCon/CloudNativeCon North America in Seattle, booth G14.
About Aqua Security
Aqua Security enables enterprises to secure their container and cloud-native applications from development to production, accelerating application deployment and bridging the gap between DevOps and IT security. Aqua’s Container Security Platform provides full visibility into container activity, allowing organizations to detect and prevent suspicious activity and attacks in real time. Integrated with container lifecycle and orchestration tools, the Aqua platform provides transparent, automated security while helping to enforce policy and simplify regulatory compliance. Aqua was founded in 2015 and is backed by Lightspeed Venture Partners, Microsoft Ventures, TLV Partners, and is based in Israel and Boston, MA. For more information, visit www.aquasec.com or follow us on twitter.com/AquaSecTeam.
