Securing Applications on Pivotal Platform - Now VMware Tanzu
Aqua has partnered with Pivotal to provide full lifecycle protection for applications running on Pivotal Application Service (PAS) part of Pivotal platform – now renamed VMware Tanzu Application Service (TAS)
Security for VMware TanzuAqua provides a full lifecycle solution for securing Pivotal Application Service (PAS) from development to production, ensuring that security and compliance policies are enforced, regardless of where your applications are deployed.
Shift Left Security for PAS Droplets
Integrate security into the CI/CD pipeline and the Blobstore to provide image risk analysis, fixing issues early and avoiding security roadblocks.
Runtime protection for PAS workloads and Diego cells
Enforce workload immutability, detect and block suspicious activities and inbound/outbound network connections, and protect Diego cells
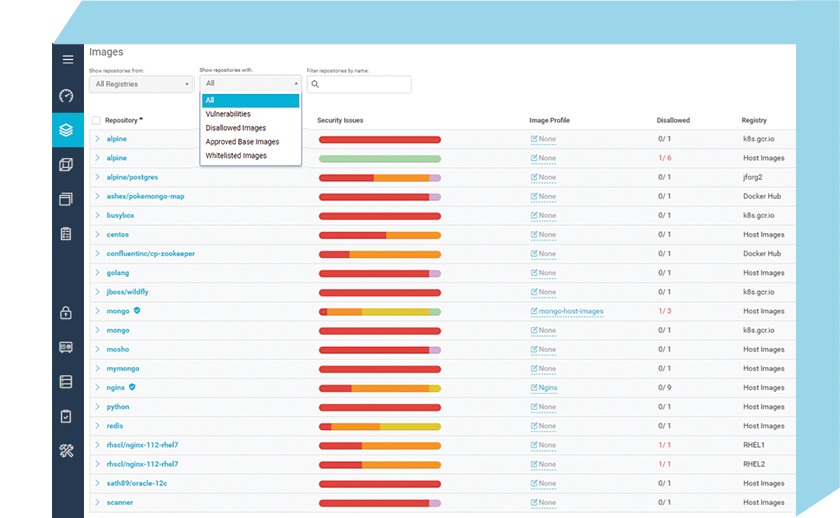
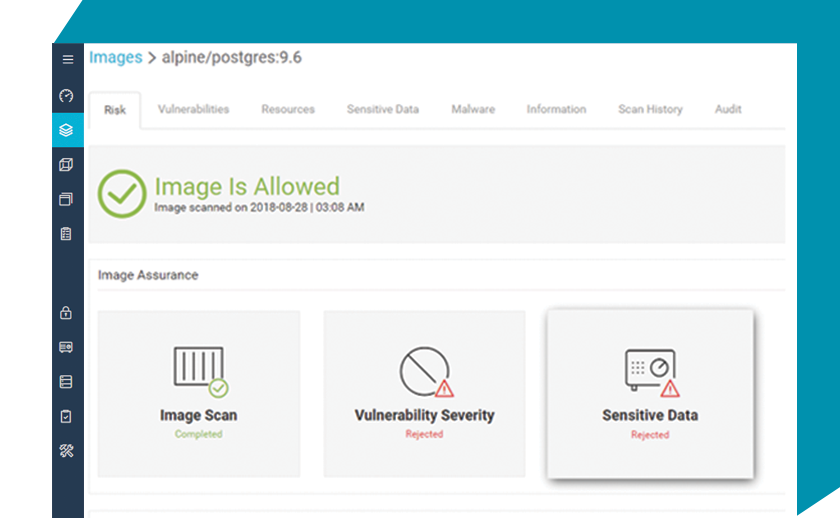
Aqua Security for PCF automatically scans applications and container artifacts for vulnerabilities, secrets, and malware to ensure only droplets that comply with your organization’s security and compliance policies will be deployed.
Automated Security Scans
Scan applications and container artifacts for vulnerabilities, secrets, and malware, directly within CI/CD tools, based on multiple vulnerability and malware feeds that reduce the number of false positives, and include actionable information for quick remediation.
Continuous Droplet Assurance
Identify and block non-compliant applications or container artifacts from being deployed based on customizable assurance policies that include vulnerability severities and scores, embedded secrets, malware found, and custom compliance checks
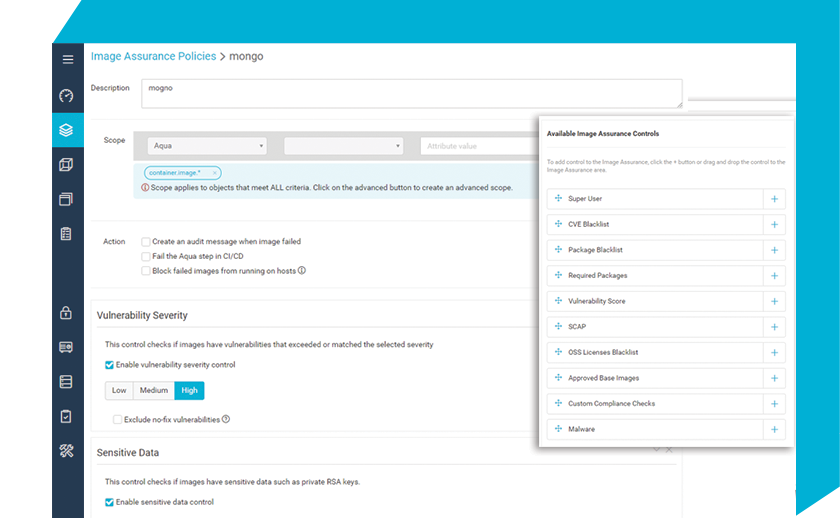
Automated Compliance Checks
Perform custom compliance checks to identify security and compliance violations of regulatory requirements for PCI, HIPAA, GDPR, and more, enforcing compliance policies in your application development and delivery pipeline.
 Nima Badiey
Nima BadieyHead of Technology Ecosystem at Pivotal


