Gartner has estimated that “90% of global organizations will be running containerized applications in production by 2026—up from 40% in 2021.”
The inherent benefits of cloud native application development enable developers to introduce new code into the environment at an accelerated rate. However, the dynamic nature of these environments amplifies the risks associated with runtime attacks.
Preventing risky code from running involves more than just using assurance gateways in the repository and CI/CD pipelines. Adversaries exploit vulnerabilities in runtime components, such as containers, orchestrators, and serverless platforms, to gain unauthorized access, exfiltrate sensitive data, or disrupt critical services.
Container escapes, where an attacker breaks out of a container to access the underlying host or adjacent containers, pose a significant threat in containerized environments. Similarly, serverless function vulnerabilities, such as insecure permissions or input validation flaws, can be leveraged to execute arbitrary code or access sensitive resources.
Security teams struggle to enforce guardrails and distinguish between legitimate but unauthorized application behavior and attackers exploiting these gaps in real-time. Moreover, stopping attacks in cloud native is challenging due to the time-sensitive nature and ease of lateral movement compared to on-premises environments, making it hard to halt an attack once it begins.
Understanding the importance of runtime security in cloud native environments is paramount for organizations looking to fortify their defenses against evolving cyber threats. Let’s delve deeper into why these protection measures are crucial and how they help safeguard the integrity and confidentiality of cloud native applications.
Challenges of traditional security measures
At the heart of cloud native architecture lies its dynamic nature. Their strength brings unparalleled flexibility and efficiency, it also creates a shift in how they are secured. According to the recent research done by our Nautilus team 75% of cloud native attacks happen in production.
One of the primary challenges in securing cloud native applications at runtime is the lack of visibility into the dynamic environment. Traditional security measures, which are static in nature, struggle to keep pace with the transitory nature of cloud native deployments. Static analysis tools and pre-deployment security scans, while valuable, cannot fully mitigate the risks posed by runtime threats. While EDR agents are valuable for traditional endpoint security, they face significant challenges in a world where the perimeter is constantly shifting due to their scalability issues, management complexity, and limited visibility.
Runtime security encompasses a range of techniques and technologies designed to detect, prevent and mitigate threats during application execution. These protections operate in real-time, monitoring the behavior of applications and their underlying infrastructure to identify and respond to malicious activity promptly.
Key capabilities of a cloud native runtime security solution
When evaluating a cloud native runtime security solution, it is crucial to look for key capabilities that ensure robust security and seamless operation across all cloud platforms. Essential capabilities to look for include the ability to secure all workload types, regardless of whether they are on public, private, or hybrid clouds. This ensures a comprehensive security posture during your cloud transformation journey, safeguarding against diverse threats across different cloud infrastructures.
A runtime solution should utilize eBPF (Extended Berkeley Packet Filter) as it offers improved efficiency and visibility crucial for cloud native environments. eBPF’s kernel-level integration ensures high efficiency and low overhead, making it ideal for high-performance environments. It also offers deep visibility into system calls, network packets, and other kernel-level events, enabling comprehensive monitoring and detection of malicious activities. eBPF can help enforce security policies in real time, providing immediate responses to threats and minimizing vulnerabilities.
Additionally, a runtime security solution needs to utilize a multi-layered approach to detect risky behavior of the workloads, whether caused by attackers or by problematic applications that expose the environment to risk. A reverse-shell attack is a prime attack use case for runtime. It’s used often to bypass traditional firewall and network security settings and allows an attacker to remotely execute commands and perform malicious activities on the victim’s system. A runtime security solution can analyze this risky behavior, determine whether it’s within the bounds of ‘normal’ operation and enforce protection to stop the attacker from executing in runtime.
Prevent
One of the primary capabilities of such a solution is its ability to prevent attacks by reducing the attack surface. This is achieved by hardening the runtime environment, which eliminates potential entry points for threats and ensures workload immutability. By preserving container integrity and automatically blocking unauthorized activities, such as rootkits, cryptominers, privilege escalation and more, the solution guarantees that only original image executables and commands run, without disrupting the container. Additionally, it should restrict access and prevent any lateral movement or escalation within or between workloads, thereby fortifying the environment and locking it down against potential threats.
Detect
Detecting cloud threats in real time is essential for maintaining a secure environment. By observing suspicious attack patterns, discovering behavioral anomalies, and leveraging real-world threat intelligence, the solution can detect threats that others might miss, such as in-memory and fileless attacks. By employing both behavior and signature-based detection methods it can uncover known and unknown threats, such as zero-day vulnerabilities and provide real-time kernel visibility to minimize the time to protection. By mapping these techniques to common frameworks such as the MITRE ATT&CK, organizations can ensure they have comprehensive coverage against a wide range of known attack vectors.
Stop
Real-time protection against malware is another critical feature. A robust cloud native runtime solution can automatically block or restrict unapproved activities across running workloads, stopping malware attacks instantaneously. It identifies indicators of compromise (IOCs), file hashing, or malicious signatures to block malware on access or download. This proactive approach extends to preventing zero-day attacks by blocking any lateral movement or escalation within cloud workloads, ensuring comprehensive security coverage.
Respond
Finally, an effective cloud native runtime solution facilitates swift response and investigation. It enables the collection of forensics data, detailed reporting on attack impact, and mitigation of attacks across all stages. With incident response capabilities, it quickly maps out attack patterns and creates detailed timelines of events, providing situational awareness during zero-day attacks. This allows for fast, forensic-level precision in managing, investigating, and responding to incidents, alongside providing clear, actionable remediation steps and comprehensive reports using the MITRE ATT&CK framework.
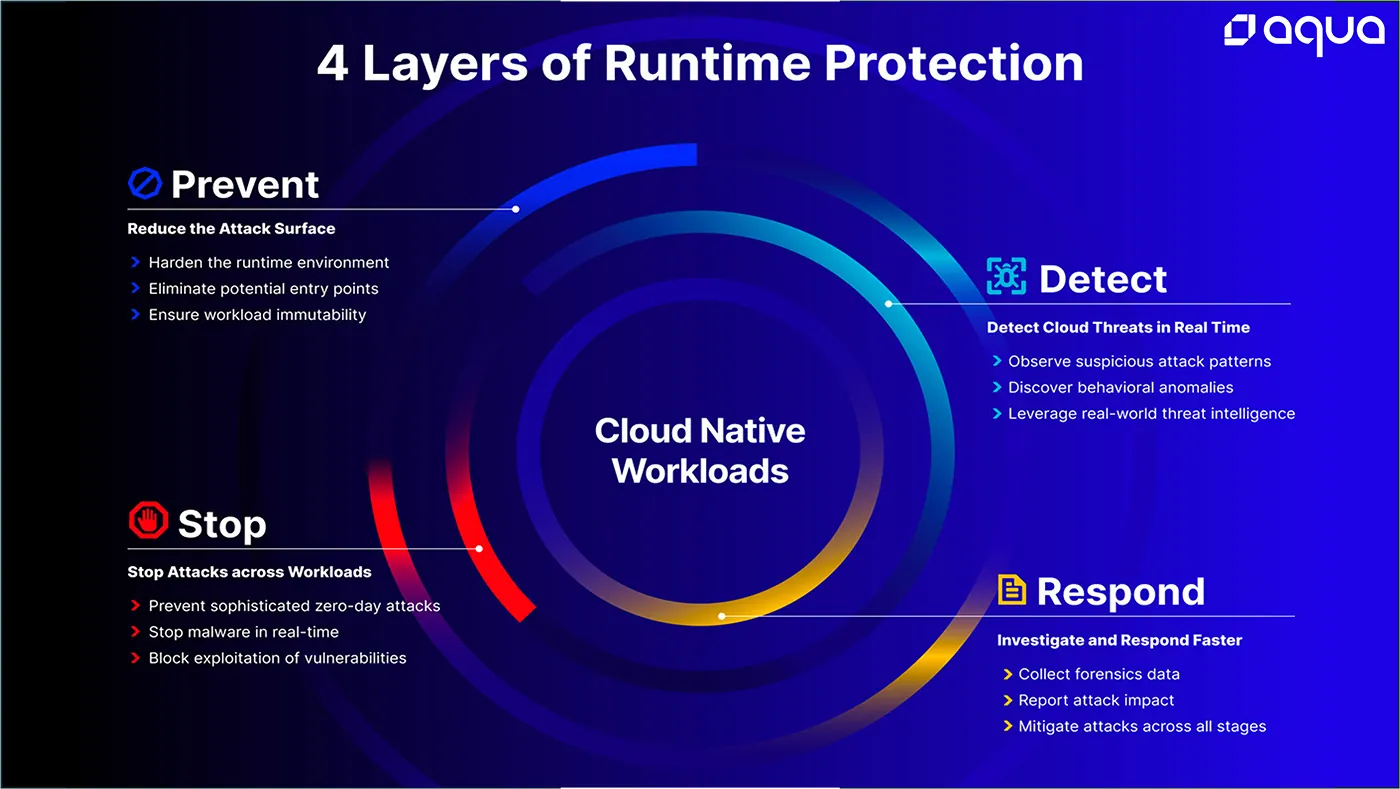
Figure 1: 4 Layers of Runtime Security
Runtime provides organizations with the visibility and control needed to secure their cloud native applications against a wide range of attacks. By continuously monitoring application behavior, these protections enable proactive threat detection and response, minimizing the impact of security incidents on business operations.
The Imperative of Runtime
Understanding the importance of runtime security in cloud native environments is essential for organizations seeking to embrace the benefits of cloud computing without compromising on security. By investing in runtime security measures and adopting a proactive mindset towards threat detection and mitigation, organizations can effectively safeguard their cloud native applications against the ever-evolving threat landscape.
Aqua’s Runtime solution offers true cloud native workload protection for risk reduction and attack prevention that goes beyond simple risk management to provide security professionals with complete visibility into production workloads and the tools necessary to identify, prioritize, and stop zero-day attacks and other sophisticated threats from executing in runtime.
Learn more about securing containers at runtime and how Aqua can help by downloading our eBook Protecting the Cloud Native Enterprise: Building the Foundation for Securing Containers at Runtime