Trivy is an easy-to-use, comprehensive open source scanner that helps developers gain visibility into the software components used in their applications. With the growing awareness about supply chain security, software bills of materials (SBOMs) have become the standard for creating software inventory lists. To simplify this process, Trivy recently added support for generating SBOMs as a top-level command in the CycloneDX format, an industry-wide SBOM standard.
In this post, we share an overview of SBOMs, their use cases, and their role in the industry. We’ll also cover how to use Trivy to generate SBOMs in the CycloneDX format.
An introduction to SBOMs
SBOMs originally come from manufacturing, where they are used to provide a clear roadmap of the components that make up a product. In the software world, the US Department of Commerce defines an SBOM as “a software bill of materials (SBOM) is a complete, formally structured list of components, libraries, and modules that are required to build a given piece of software and the supply chain relationships between them. These components can be open source or proprietary, free or paid, and widely available or have restricted access.”
Whether you’re choosing, producing, or operating software, your product will rely on a variety of third-party libraries and components. An SBOM will provide a machine-readable list of their versions that run in your software and their related vulnerabilities.
The benefit of an SBOM is that it can be shared easily. Thus, you can gain insights into the components, dependencies, and vulnerabilities of a product before committing to using or integrating with it. This improves the overall transparency and visibility into security issues across the industry and helps detect vulnerabilities early and efficiently.
There are two main industry standards for SBOMs:
- Software Package Data Exchange (SPDX and SPDX Lite), an ISO standard hosted by the Linux Foundation, which outlines the components, licenses, and copyrights associated with a software package.
- CycloneDX, an open source, lightweight SBOM standard, which is used in application security and supply chain analysis and originated from the Open Web Application Security Project (OWASP).
In general, there are several use cases where SBOMs can be helpful, both internal and external:
- Compliance review
- Security assessment
- License compliance
- Quality assurance
- Compliance audit
- Customer audit
In the next section, we’ll show how you can use the Trivy CLI to generate SBOMs. Currently, Trivy provides SBOMs in the CycloneDX standard.
Generating an SBOM with Trivy
It’s been possible for some time to generate package lists using Trivy. This can be useful if you’re looking to get an idea of what’s been built into your container image.
To follow the examples below, ensure that you have Trivy installed on your terminal. For an installation guide or upgrade options, check out Trivy’s documentation.
trivy --version
Version: 0.25.0
Vulnerability DB:
Version: 2
The following command will provide a list of the package versions and SHA hashes, as shown below piped through jless:
trivy -q image --ignore-unfixed --format json --list-all-pkgs ubuntu:20.04
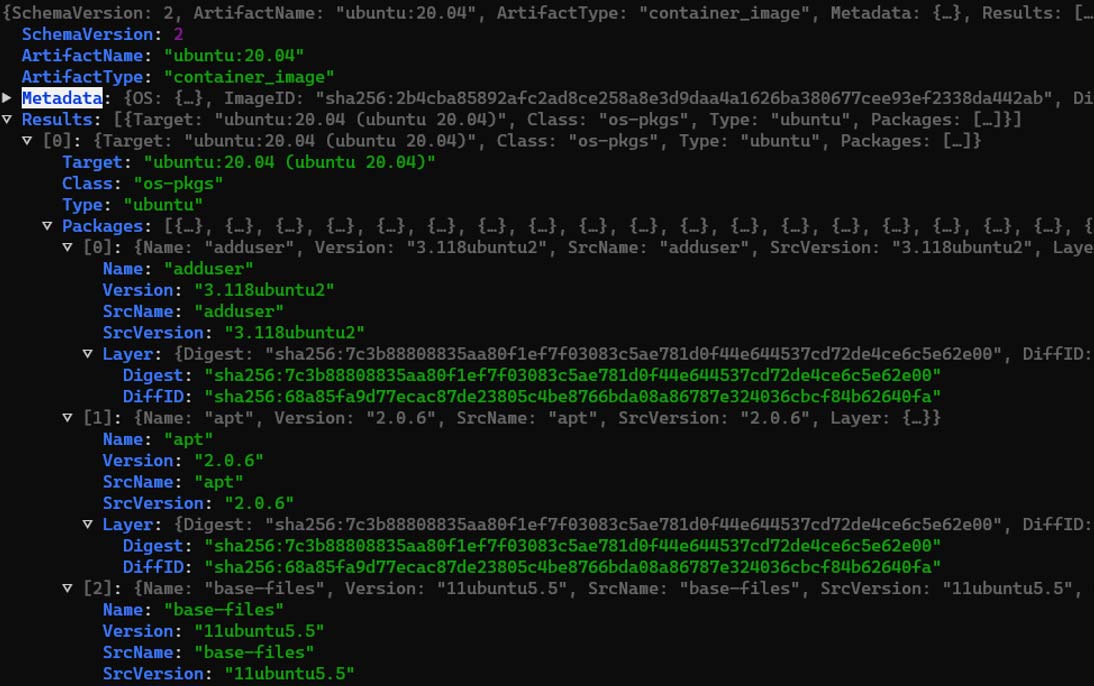
Figure 1: Trivy image scan to list all packages
Based on this, we can use Trivy’s CycloneDX feature, contributed by Masahiro331, to generate our SBOM:
trivy -q image –format cyclonedx ubuntu:20.04 | jless
And we get our SBOM!
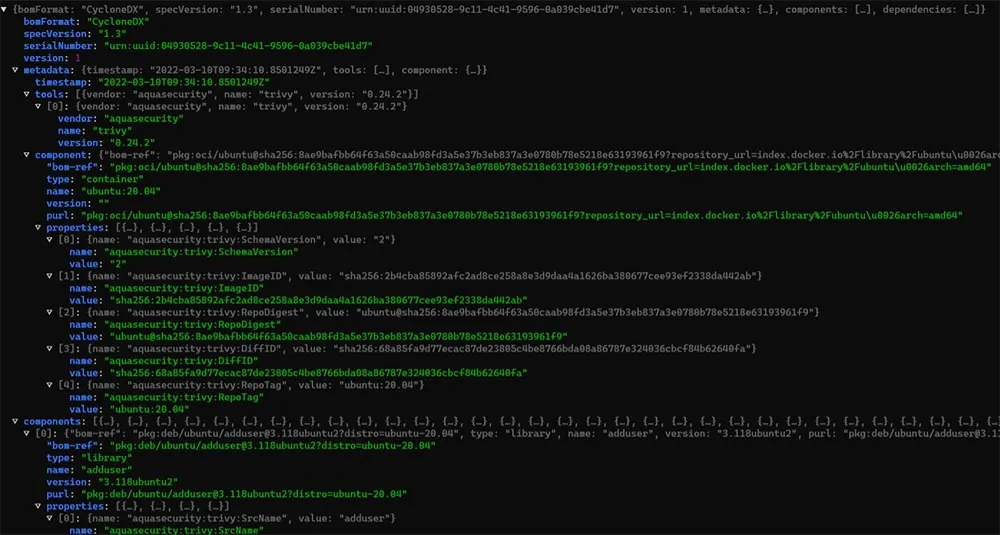
Figure 2: An SBOM generated by Trivy
However, we’ve made the process much easier, and it’s also possible to generate an SBOM through one of Trivy’s top-level commands. If you’re already using Trivy, ensure that you have the latest release installed and upgrade the Trivy CLI.
Like other Trivy CLI commands that you might be already familiar with, you can use the SBOM command:
trivy sbom --help
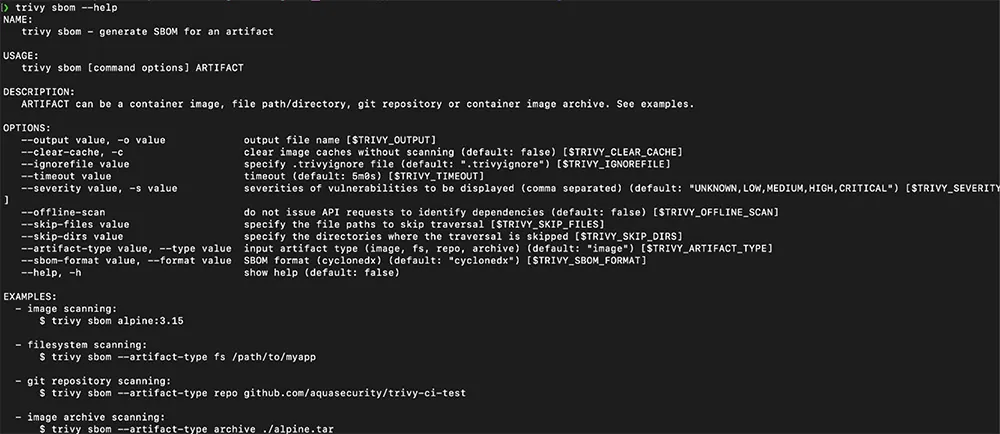
Figure 3: Trivy’s CLI SBOM command and options
We can then generate an SBOM for our container image:
trivy sbom alpine:3.15
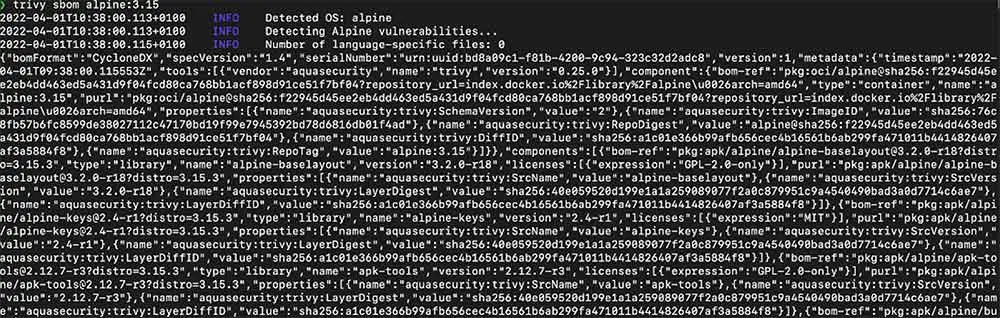
Figure 4: Trivy SBOM scan on a container image
Generally, the output is returned in machine-readable format. If you’d like to access a human-readable version of the SBOM, use the “-p” flag before sbom and piped through jq:
trivy -q sbom alpine:3.15 | jq
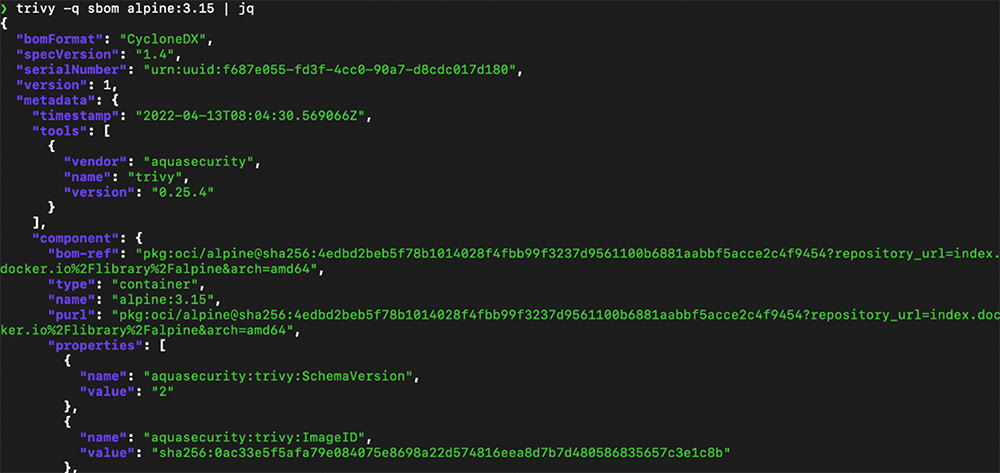
Figure 5: Trivy SBOM scan on container image in human-readable form
To create an SBOM for other resources, use the flag “–artifact-type” before specifying the resource.
This allows us to create an SBOM for our filesystem:
trivy sbom --artifact-type fs ./
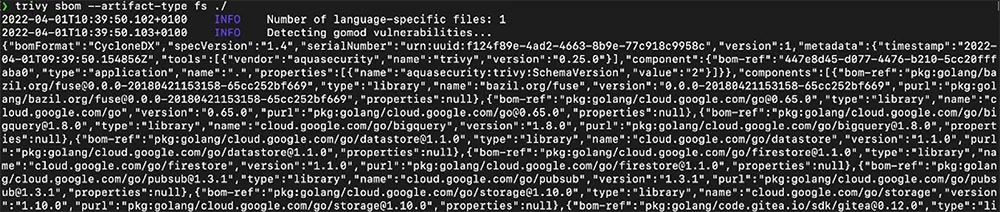
Figure 6: Using Trivy SBOM on a filesystem
Or for the entire repository:
trivy sbom --artifact-type repo github.com/aquasecurity/trivy-ci-test
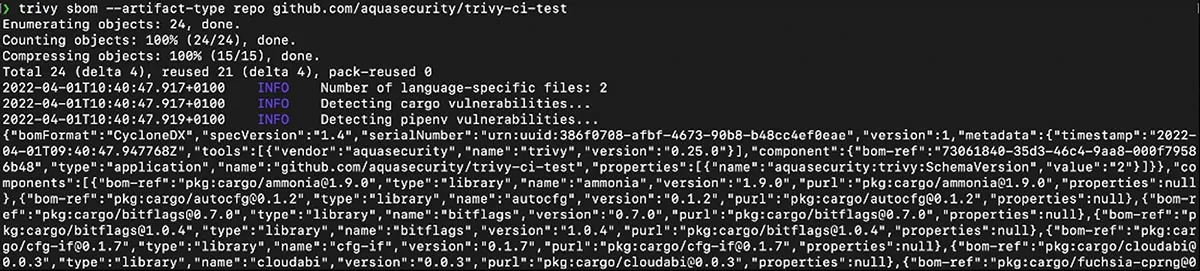
Figure 7: Using Trivy SBOM on Git repository
Summary
Generating reliable source package information in the form of SBOMs is an important part of software supply chain security. With Trivy, you can now easily add this step to your development process and improve the security of your applications without the need to use additional tools.
Stay tuned for more features in Trivy, including support for SPDX and other SBOM formats as well as SBOM-related capabilities. If there’s anything specific you would like to see, let us know on GitHub or Slack.
Try Trivy today and make sure to give it a star on GitHub ⭐ and join our community on Slack to share how you’re using SBOM in Trivy!