We have enhanced our Cloud Native Security Platform (CSP) by adding Cloud VM protection capabilities for VMs that are not running container workloads. Aqua now provides a full-stack security solution across all workload types: VMs, containers, and serverless functions, for both Linux and Windows VMs.
Cloud VMs are standardized, immutable infrastructures that often use a minimal OS and conform to strict, automated configurations. Much Like containers, cloud VMs are managed using automated templates and processes for provisioning, configuration management, and application deployment. From a vulnerability perspective, VMs are not usually patched in runtime, but rather fresh VMs are spun up from an updated machine image.
Conventional host-based security solutions for physical servers and VMs use complicated agents that perform many functions that are no longer relevant to the cloud era. Aqua has replaced such elements with a lightweight solution suited for cloud workloads, which is easier to manage and less taxing on cloud resources. With the new Cloud VM protection, Aqua has introduced a series of security and compliance controls intended to protect VMs in cloud environments, along with the containerized applications running on them. These new capabilities are now a part of the Aqua platform which can be leveraged to manage full-stack security and compliance.
The new controls for Cloud VMs include File Integrity Monitoring, Network Discovery and Micro-Segmentation, Vulnerability Scanning, and Cloud VM Assurance Policies.
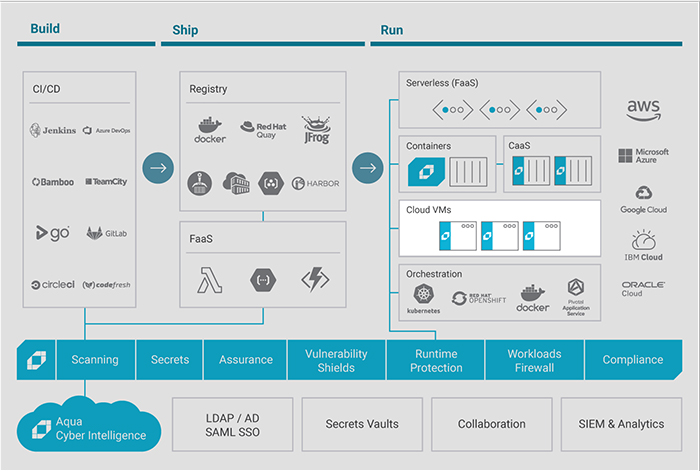
See how securing cloud VMs integrates into the aqua Cloud Native Security Platform
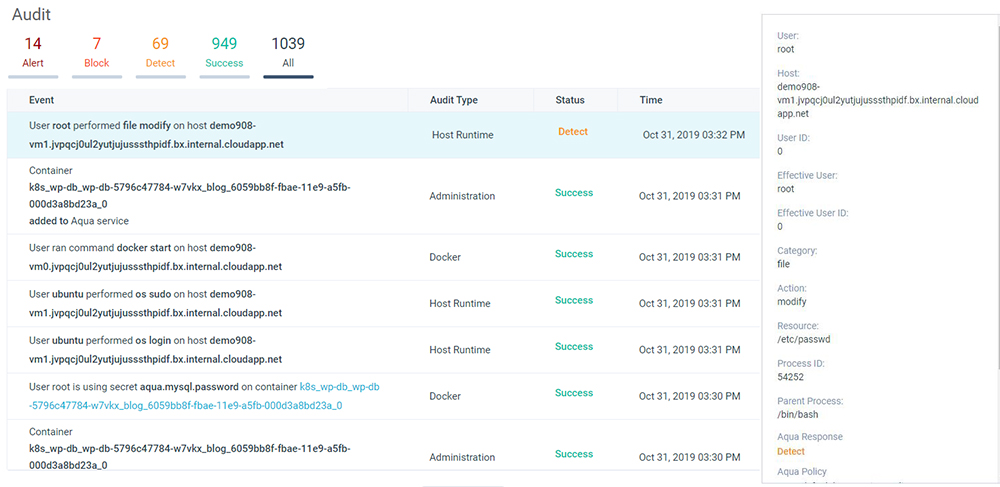
File integrity monitoring
File Integrity Monitoring (FIM) is a process that validates the integrity of the operating system and application files using a verification method between the current file state and a known, good baseline. This is a basic requirement that ensures that applications comply with the PCI-DSS standards. Aqua’s FIM capabilities include:
- Monitoring who changed what and when
- Auditing files and folders for read, write, and attribute changes
- Reporting the OS user and processes used to perform the operation
- Support of both Windows and Linux OS
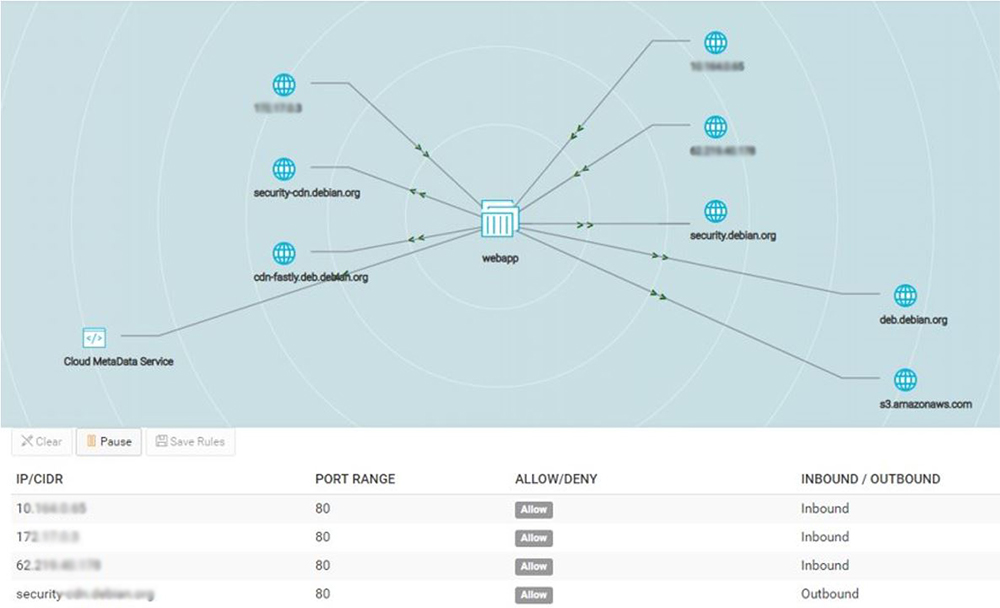
Network discovery and micro-segmentation
When working in a hybrid-cloud or with legacy applications (applications that were not yet migrated to micro-services), managing network traffic can be a challenge. It may require more than one solution to provide the required security posture of applications. Aqua networking capabilities already provide full visibility for cloud-native applications that run on a single/hybrid cloud. With our new coverage for Cloud VMs, we now provide a unified solution for securing network activity for all types of applications, containerized or not. Our Cloud VM’s Firewall capability includes:
- Logical grouping of virtual machines into Aqua services
- Automatically recording of all inbound and outbound network traffic
- Ability to enforce network firewall rules based on VM services, along with IP addresses and domain names (DNS)
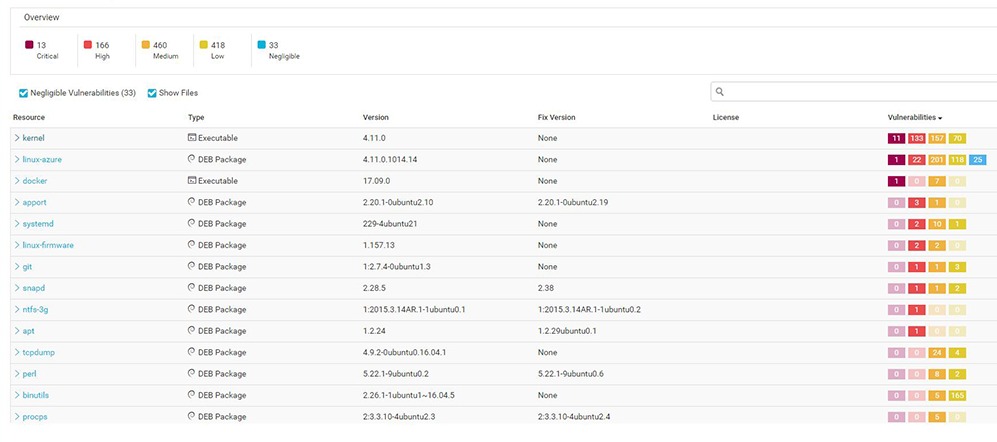
Cloud VM vulnerability scanning
These vulnerabilities are introduced by new and existing software and many of them impact packages that are used by VMs. In addition, companies that are PCI compliant must adhere to requirement 11: “regularly test security systems and processes” and keep out vulnerabilities with CVSS from 4.0 or higher. The Aqua Vulnerability Scanner provides:
- Continuous scanning of cloud VMs for known vulnerabilities and malware
- A detailed report which covers the vulnerable package and remediation steps
- Security alerts on vulnerable VMs
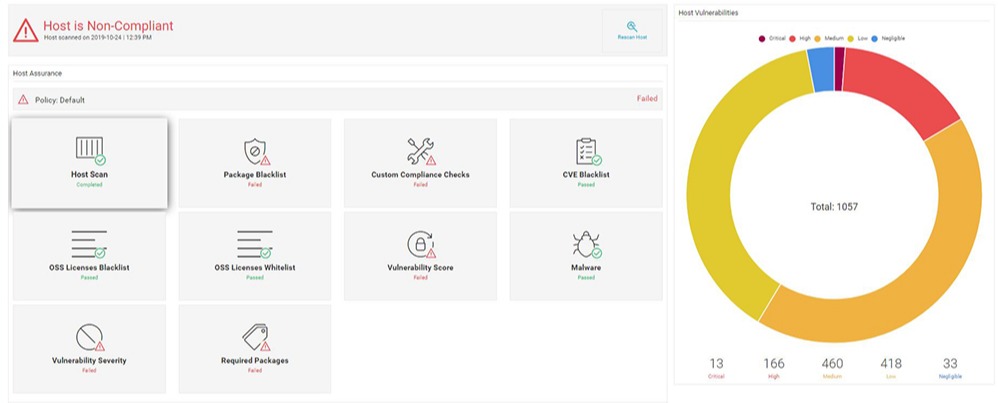
Cloud VM assurance policies
Scanning cloud VMs for vulnerabilities and malware is the first step towards getting the security posture for VMs. It is also critical to evaluate VMs with respect to industry security standards, such as Linux CIS and PCI-DSS, as well as internal organizational guidelines. Aqua VM Assurance Policies allow you to enforce these standards in development and in production. Aqua VM Assurance Policies can be used for:
- Setting alerts on system and application configuration violations
- Defining a compliance baseline for VMs by using built-in and custom configuration checks
- Quickly reviewing remediation steps for aligning non-compliant VMs
Security for all cloud native workloads
As security requirements for public and private clouds continue to evolve, Aqua stands up to those critical requirements in order to protect cloud-native workloads. With the introduction of VM security, Aqua provides its customers with a complete workload protection platform for where they are today and where they are heading in the future.

