With the rapid adoption of Kubernetes, an unforeseen consequence has emerged — there simply aren’t enough trained K8s experts to go around, let alone K8s security experts. Kubernetes environments have increased in size and complexity, expanding its attack surface, and ultimately heightening its susceptibility to exploitation. Given that the configuration of K8s involves many different parameters being tweaked by many different users, the potential for human error is rife. So, what can you do about it?
You need to treat your K8s configuration as the complex system of cloud native infrastructure that it is. Just as Cloud Security Posture Management (CSPM) is used to automate secure cloud infrastructure configuration and eliminate repeated manual intervention, now is the time to apply Aqua KSPM to your K8s infrastructure.
What exactly needs defending
As the use of Kubernetes continues to grow, so does the rate of infrastructure misconfigurations. Chances are you have multiple K8s clusters in various locations to manage. Considering that just one cluster in one location is complicated enough to manage, the challenge of multiple clusters using multiple services with seemingly countless components, and thousands of configuration options is understandably overwhelming. Maintaining this requires keeping track of cluster configurations, RBAC, internal components, host environments, workloads, and more. The only way to do this consistently, efficiently, and without repeated errors, is through continuous auditing of these configurations, which requires repeatable, automated capabilities.
There is also an emotional topic that needs to be addressed — human error. Humans make mistakes, I know this because I am one. Since development responsibilities are distributed, and the “shift left” movement has created a front-loaded process, many more fingers (Dev) are in the proverbial pie. Sure, this provides for better agility by giving more people access to define their environments. But the downside is that most developers aren’t infrastructure security gurus, and small changes upstream can have a big effect downstream.
It’s an unfortunate fact of “cloud native” life that there aren’t enough trained, certified K8s admins. And even if you get certified, it doesn’t automatically qualify you as a security expert. This is because the security model in Kubernetes is multi-faceted and non-linear. This means that a setting chosen in one area of your infrastructure can affect other settings in a way that’s hard to understand, especially if you don’t really know what you’re doing. For example, looking at the interaction between image vulnerabilities, pod security settings, and node host OS hardening — this can create a “perfect storm” of security gaps if they are not properly configured.
Keep using these tools
For the past few years, the CIS Benchmark has been the industry’s single, detailed, actionable “standard” that people were able to align with — but it has its limitations. CIS Benchmark is both insufficient and a difficult concept to implement correctly since it just gives you a series of things to check with no real assessment related to your particular environment.
Aqua had already led the way with automating CIS Kubernetes benchmark checks with our open source Kube-bench tool, and it has been an important part of the Aqua platform since. Additionally, a while back we introduced the industry’s only dedicated pen-testing tool for Kubernetes, Kube-hunter, which was also integrated into our platform. Aqua’s Risk Explorer is another tool that natively provides visibility and prioritization of risk in a K8s cluster. So there’ve been plenty of capabilities within Aqua for understanding and prioritizing security issues in Kubernetes, but our customers have been telling us they need a more comprehensive approach, one that also simplifies and supports their work with best practices.
Enter Aqua KSPM
Our new Aqua Kubernetes Security Posture Management (KSPM) is a key component of our overall Kubernetes security solution. KSPM includes Aqua’s existing capabilities but, more importantly, it introduces and integrates significant new capabilities: K8s assurance policies based on Rego expressions, and K8s roles & subjects risk assessment, providing a complete methodology for the continuous security and compliance posture of your Kubernetes infrastructure.
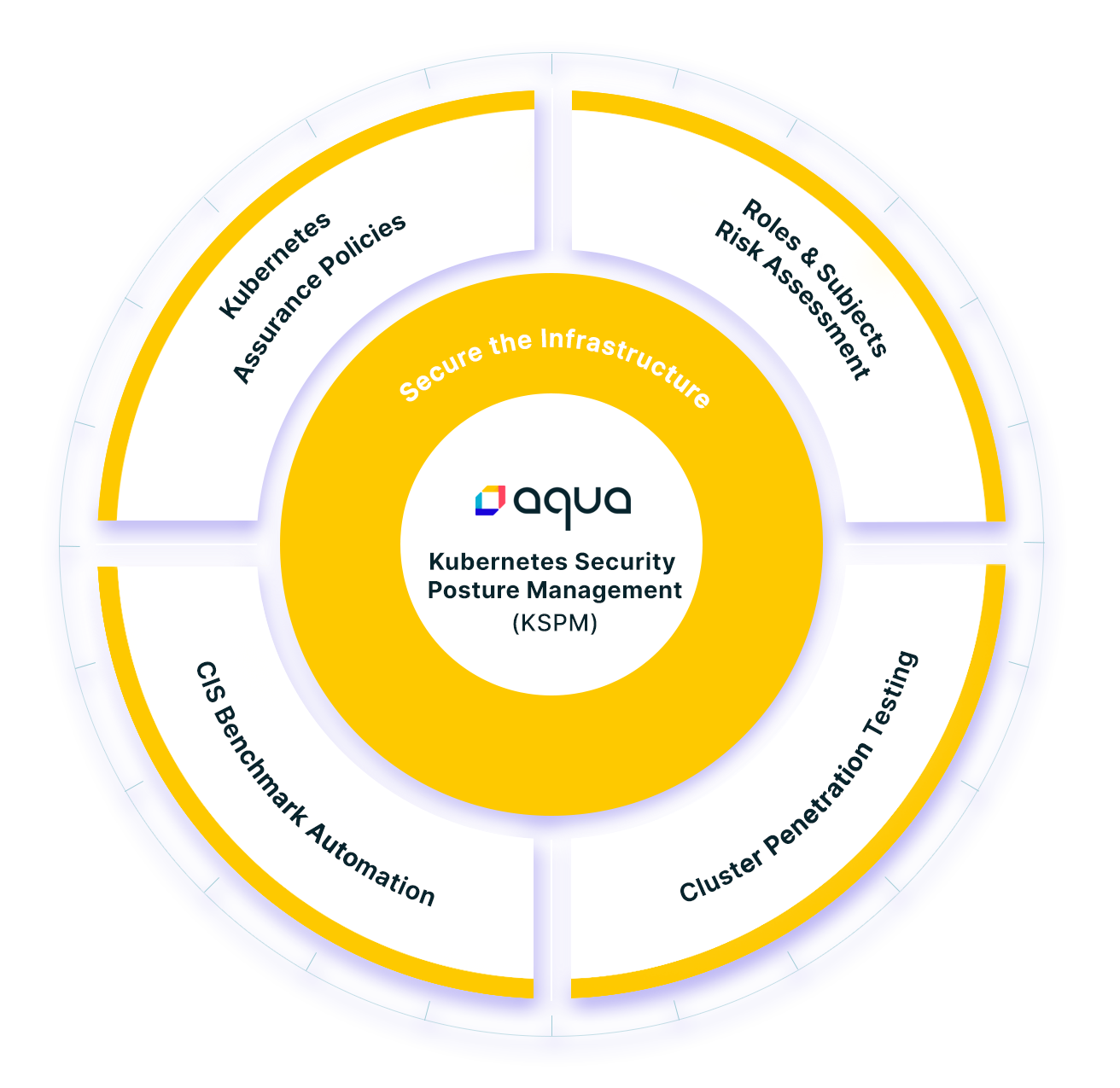
Aqua KSPM
By leveraging and extending Kubernetes-native capabilities, KSPM enables your security and compliance teams to institute and enforce policy-driven configuration and governance, remediate identified risks, and apply continuous security assessment and advice to secure your cloud native applications.
K8s assurance policies – this new capability lets you effectively manage policy and governance resources in support of your Kubernetes implementation. Representing a new type of assurance policy, it helps fulfill the promise of shift-left workload security by evaluating the security posture of your workload configuration from the start. Now you can use Kubernetes-native controls to approve/prevent pod deployment, leverage dozens of out-of-the-box rules based on the capabilities assigned in K8s, and create custom rules using Rego language and import from Open Policy Agent (OPA).
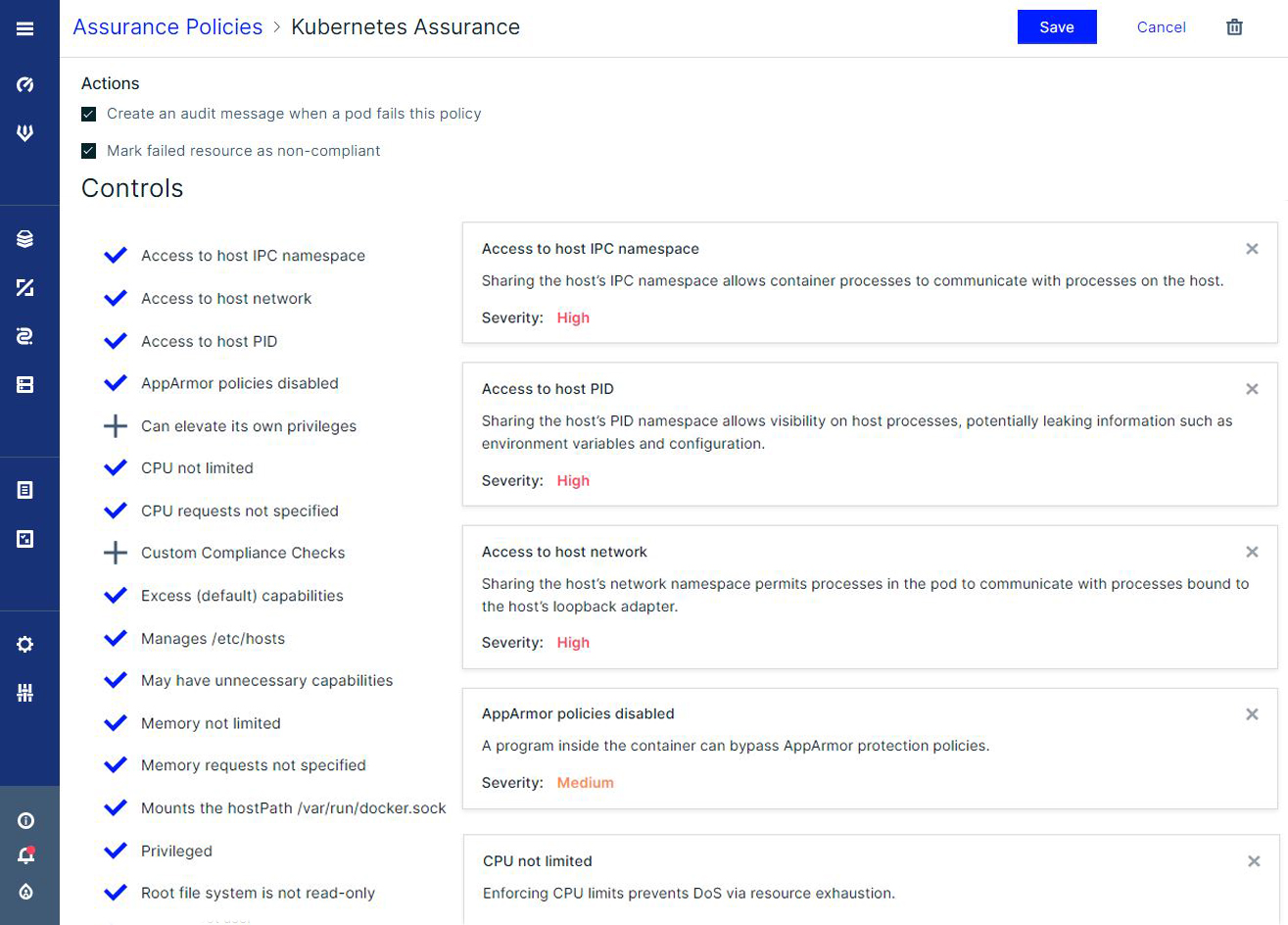
Assurance Policies view
Aqua Kubernetes assurance policy also includes a new pod compliance flow. It combines image assurance policies with Kubernetes assurance policies to build a much more complete and secure compliance posture.

Pod Compliance flow chart
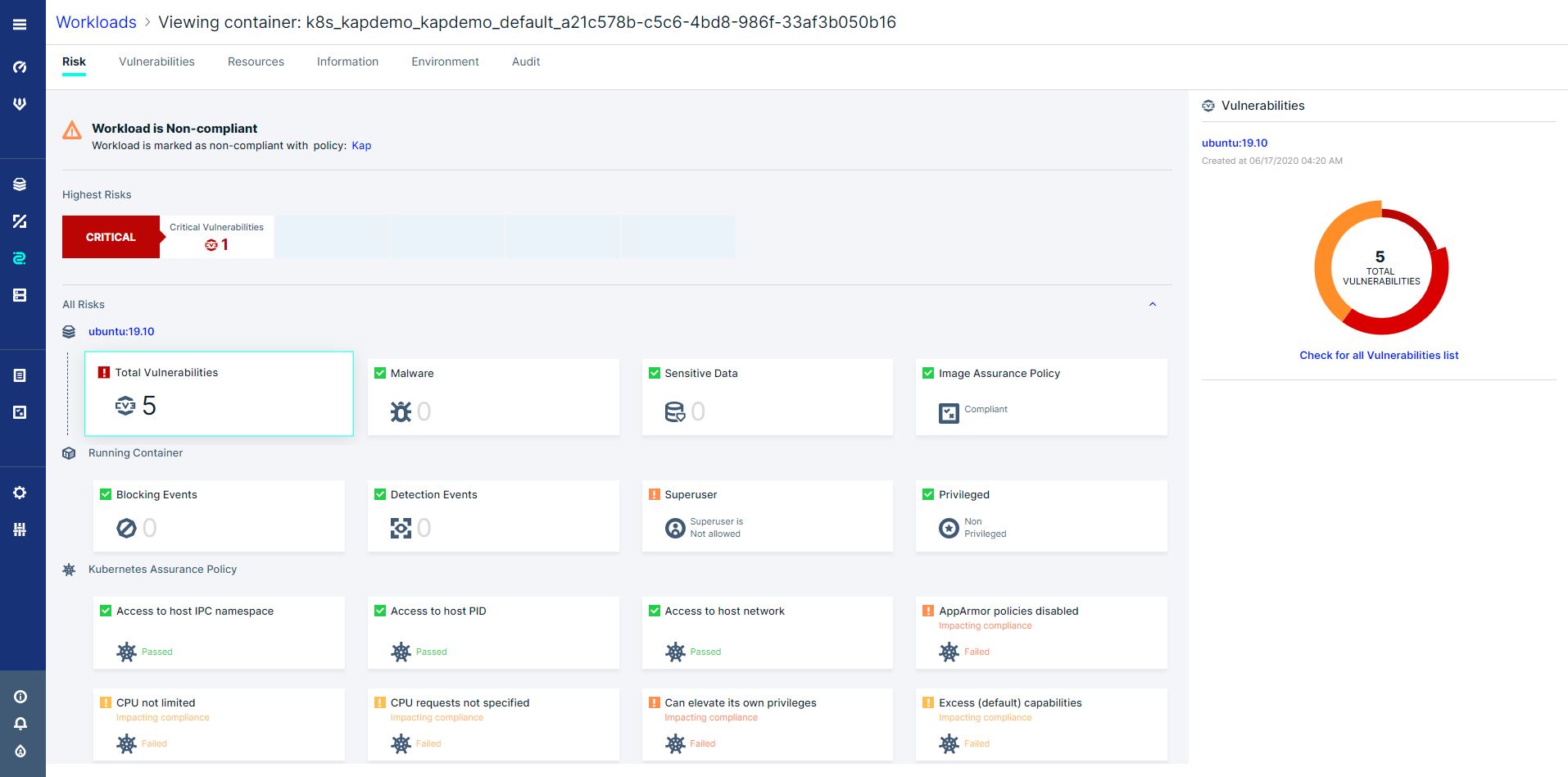
The new Aqua policy flow in KSPM ensures that your workloads clear two evaluations. One determines if the contents of an image (vulnerabilities, secrets, malware, etc.) are out of compliance with any assurance policies. A second check applies Kubernetes assurance policies based on cluster and pod configuration (such as resource limits, capabilities, networking). If any image instantiated in a pod is found to conflict with either policy checks, it will be marked as non-compliant, and, based on your policies, it prevents the deployment of the images in your cluster.
Single pane of glass view for assurance policies
K8s Roles & Subjects Risk Assessment – this enforces least privilege best practices in Kubernetes, to provide unique capabilities that make it easy to identify and address high-risk areas in user and service account access.
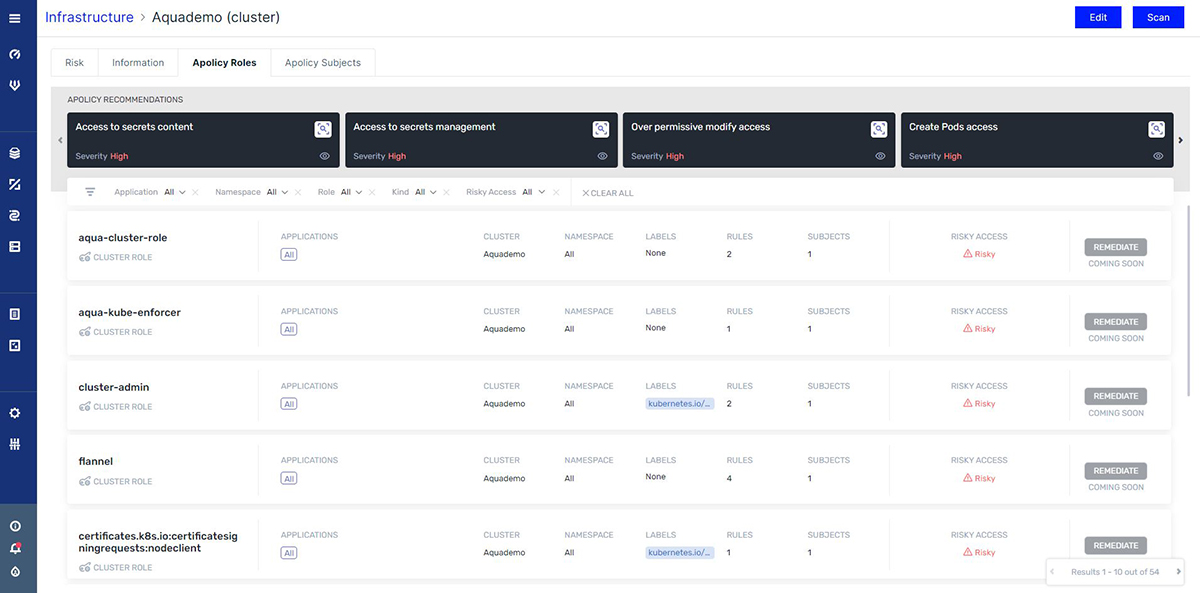
View of Roles and Subjects
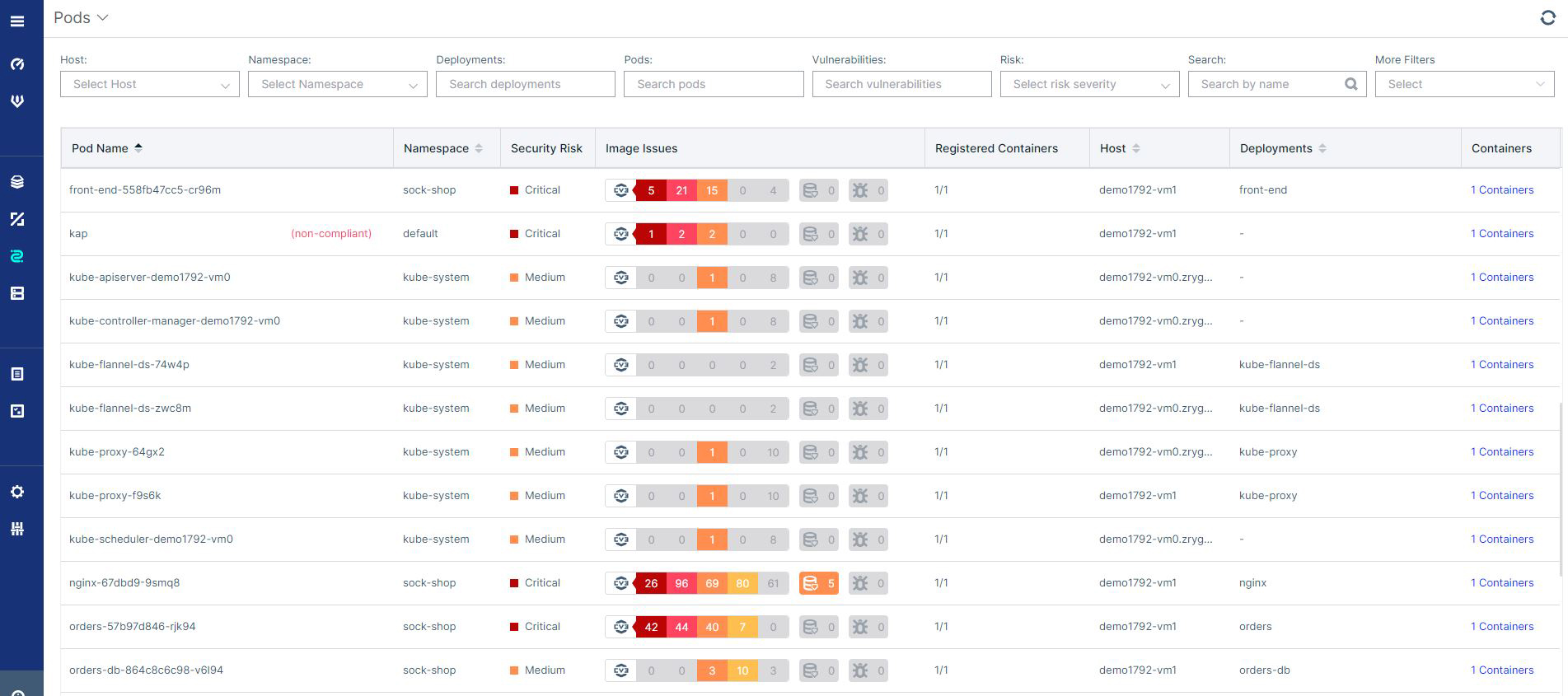
In a single view, Aqua KSPM brings it all together
Aqua KSPM includes a view into all the elements affecting risk in you K8s cluster. By providing rankings based on our expertise built into Aqua KSPM, we’ve made it easier for you to prioritize remediation in your environment. The rankings are combined to show the different types of risks affecting your K8s workloads — all in one place.
So, what have we learned?
Kubernetes is hard to configure. Attack surfaces are expanding. K8s security experts are few and far between. Humans make mistakes. Aqua provides the solution.
With our latest software release, we announced Kubernetes security posture management, which redefines the Kubernetes security solution space with a truly complete approach. Aqua KSPM can help you secure your K8s cluster configuration, understand and reduce your vulnerability to attacks, correctly apply least-privilege access, remediate risks, and stay compliant with your assurance policies. You can also use Rego and OPA capabilities to make it easy for DevOps teams to implement their policies. Best of all, we’re adding these capabilities based upon existing knowledge. K8s assurance policies and the assessments both apply well-researched rules that don’t just automate checks, but also assign weight to the risk they pose to your environment.

