There’s an overwhelming number of vulnerabilities in container images – and the security of your deployments is probably suffering because of it. No matter the size of your organization, it’s a significant challenge to identify the biggest risks to your business and know what to tackle first. Merely classifying and filtering CVEs by the highest severity or score is a nice first step, but it lacks the contextual risk factors needed for specific environments. Additionally, in many environments it will yield too many results to handle effectively. What’s required is a more holistic approach to enable prioritizing by risk and context – this is exactly what you get with Aqua.
Understanding Contextual Risk
In any given customer environment, there are contextual factors that affect how risky a vulnerability might actually be. These factors may well be specific to the environment, or temporal factors that affect a vulnerability’s real risk (e.g., does it really affect this workload) at a given time.
Within the Aqua platform, we have access to a wealth of continuously updated vulnerability data, as well as a full picture of the runtime environment, and we’ve used that to enable the classification, filtering, and prioritization of vulnerabilities according to the following parameters:
- CVE severity and CVSS: What score and rating was a CVE given?
- Exploitability of the CVE: Is there an exploit in the wild? Can it be exploited via the network?
- Running workloads that are vulnerable: Does your specific runtime environment have workloads that are impacted by the CVE?
- Actively running packages: Does your running workload use a vulnerable package?
How this Works: Exploits in the Wild
While a CVSS base score addresses the theoretical level of CVE exploitability and classifies 60% of the vulnerabilities as high or critical severity, only 2.5% of the vulnerabilities have actual exploits in the wild that are available for attackers to use. Prioritization based on this factor is the most common method for a risk-based approach because it is simple to implement, yet effective in how much it narrows down the list.
Aqua shows and filters the vulnerabilities that have available exploits, so you can prioritize them. Additionally, the type of exploit is also presented, and this can help to prioritize it further. For example, in most cases, an exploit that can be executed remotely through the network should be prioritized ahead of an exploit that requires local access.
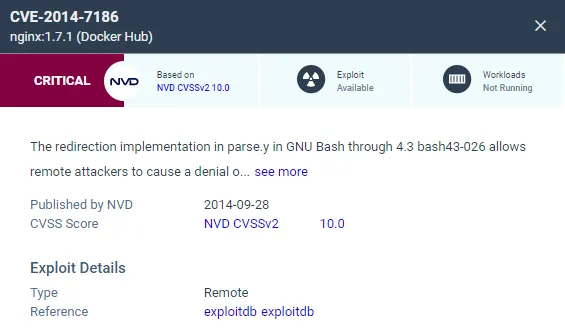
Exploit details are provided per vulnerability (when available)
Affected Running Workloads in Your Environment
Many times, organizations that scan container image registries (a practice I absolutely recommend) might get scanning results for old images or images that aren’t being used in production. This happens due to compliance reasons where the retention policy says not to delete old images. Consequently, many larger organizations store tens of thousands of images in registries, retaining both older versions as well as unused images, while actually deploying only a small fraction of them.
It is important to remember that while “Image at rest” has the potential of being an attack surface in its own right, running containers should be prioritized first as they are exposed in the production environment – which is a lucrative target for attackers.
We provide several options to address this need. You can choose to automatically scan all running containers, or scan all the images from a registry while giving priority to running containers. With either approach, the detection of vulnerabilities in running images is automated and easy to set up.
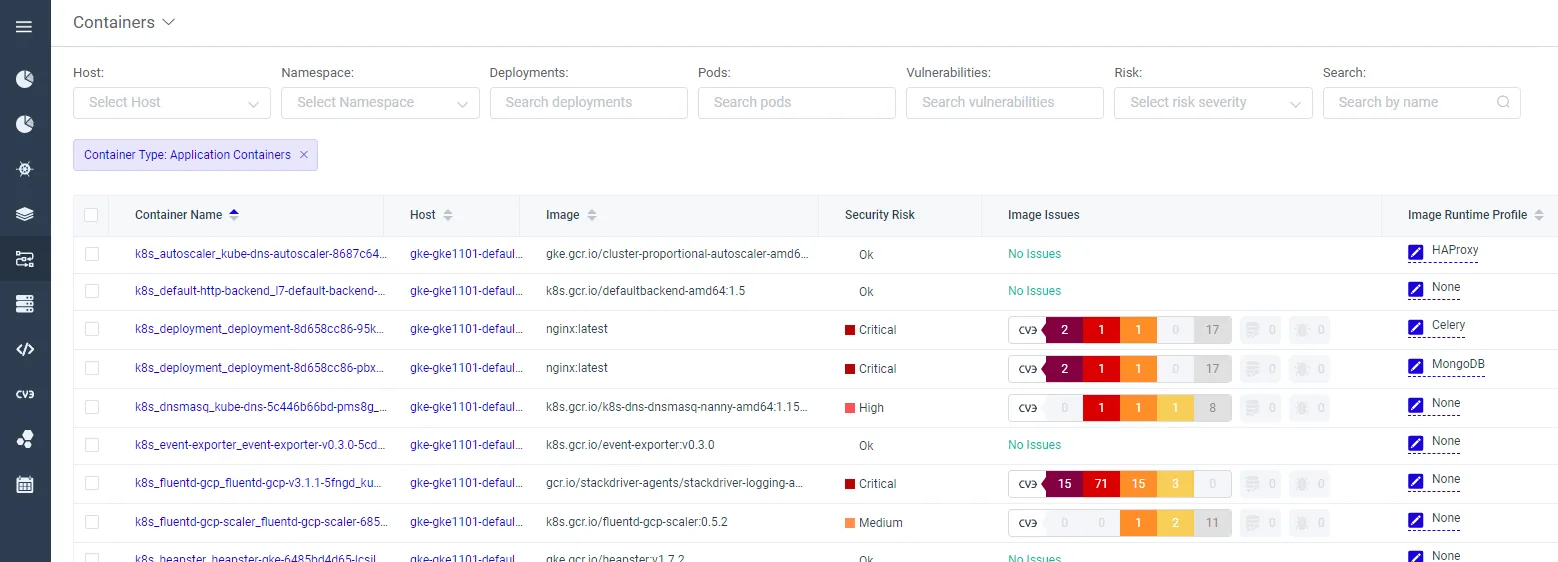
List of running containers and their vulnerabilities and additional risks
Active Packages
For a package to be exploited, it needs to be not only vulnerable, exploitable, and associated with a running container, but also needs to be run as part of an application. If you have a vulnerable package that is actively used by the application, the priority for the remediation or mitigation should be high. Wouldn’t it be great if we could know when vulnerabilities affect packages that are used in a specific application context?
Aqua vShield was created by Aqua to provide mitigation against the exploitation of specific vulnerabilities. Essentially, it is a runtime policy that is created per CVE to mitigate the risk of vulnerabilities. For example, a TCP port can be blocked by vShield to mitigate a certain CVE. But additionally, a unique benefit of vShield is the visibility that it provides for prioritization – you can run vShield policy in audit mode and track whether the vulnerable package is actively being used. If it is active, it means that the risk is very high, and remediation must be prioritized.
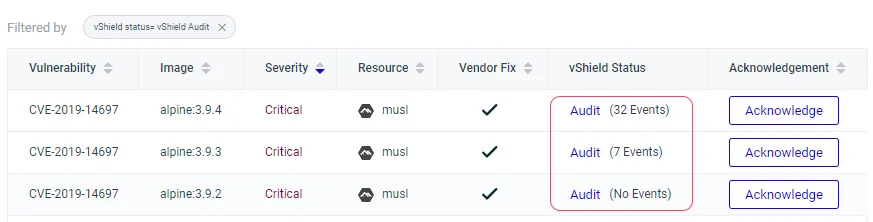
Get visibility into vulnerabilities associated with actively used packages
Business Criticality
The last piece of the puzzle is to consider what’s important to your organization and prioritize accordingly. Maybe specific applications are more sensitive, or more mission-critical, or maybe it’s a specific cluster that holds production applications you want to be prioritized.
We can use Aqua’s advanced application scoping for this purpose. For example, you can create an application scope that filters specific registries, repositories, and clusters with business-critical applications, and filter the vulnerabilities associated with those business-critical apps. Since the scope affects what specific users will see, this can help further narrow the field and focus teams on the vulnerabilities that affect their applications.
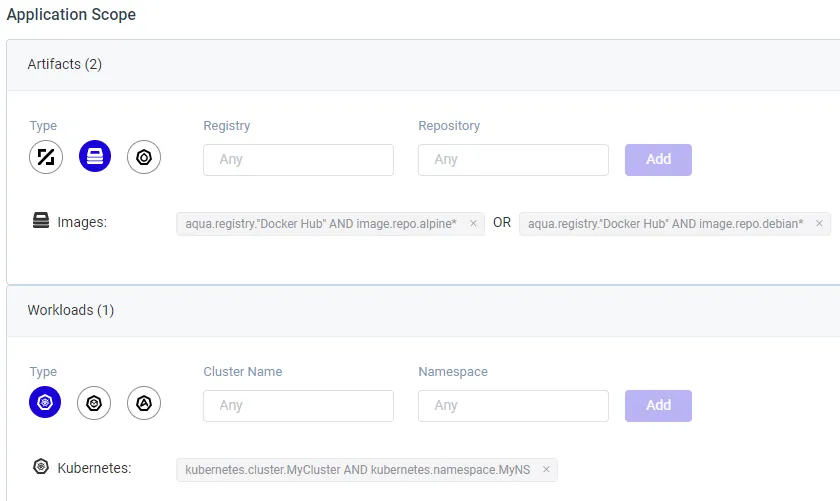
Prioritize business-critical applications by repository name, registry, cluster or namespace
Aqua Risk-Based Insights
Out of the box, the Aqua solution provides a risk-based insights interface that automatically considers risk-related contextual factors and then specifies the list of vulnerabilities from “important” to “urgent.” This allows security teams to start by assessing the list of most urgent risks before moving to the next level of risks. By doing this, it allows teams to prioritize vulnerabilities through a risk-based approach.
Now is the Time to Upgrade Your Vulnerability Management Tool
With the number of vulnerabilities increasing, quickly identifying where you should invest your team’s time and efforts is more important than ever. Vulnerability management with Aqua provides many useful capabilities:
- Natively enrich vulnerability management with risk-related contextual factors such as running containers and exploitability.
- Easy-to-use interface for narrowing down the list to prioritize contextual risks.
- The only solution in the market that gives insights on actively used packages.
- Easily filter business-critical applications using our advanced application scoping.
Addressing risks through better prioritization of vulnerabilities using multiple factors that are contextual to your environment is an efficient way of dealing with the ever-growing stream of known vulnerabilities, especially if you use a lot of open source operating systems, applications and packages. The old way of classifying CVEs is dead, long live risk-based vulnerability management.