Security for Serverless Functions (FaaS)
Ensure that serverless functions are secured and in compliance. Reduce the attack surface, control deployment, and protect functions in runtime using performance-optimized controls.
Scan functions for vulnerabilities, malware, and secrets
Aqua scans functions based on our constantly updated stream of aggregate sources of vulnerability and malware data (CVEs, vendor advisories, and proprietary research), which ensures up-to-date, broad coverage while minimizing false positives. Scan for cloud provider-specific keys and secrets and prevent their accidental exposure.
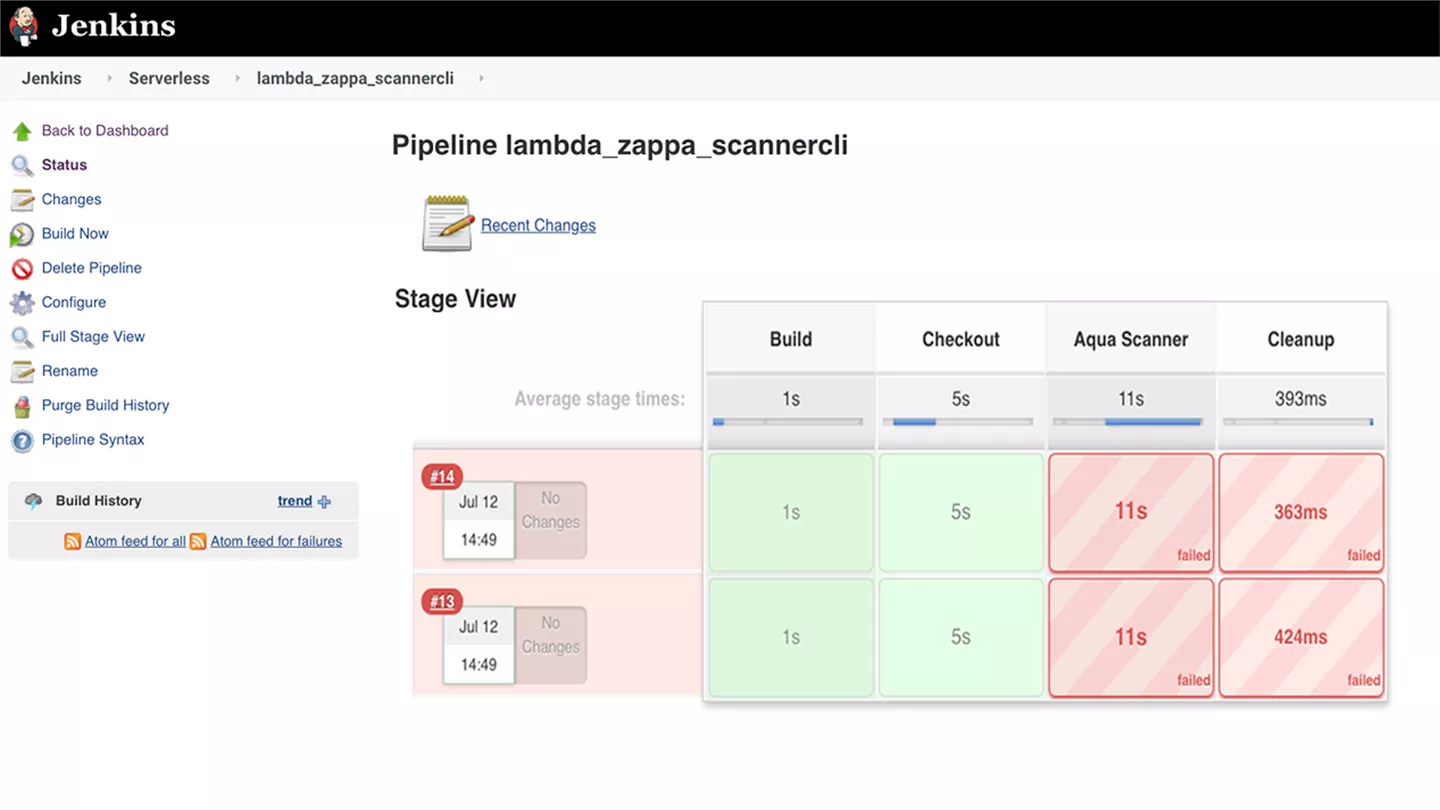
Integrate in your CI/CD pipelines
Aqua enables you to “shift left” security into early stages of development by scanning functions as they are built, shortening the fix cycle for security issues. We provide native plug-ins as well as a CLI tool that automate scanning within CI tools such as Jenkins, Bamboo, and Azure DevOps. As a step in the build, developers can view scanning results and suggested mitigation from within a familiar environment.
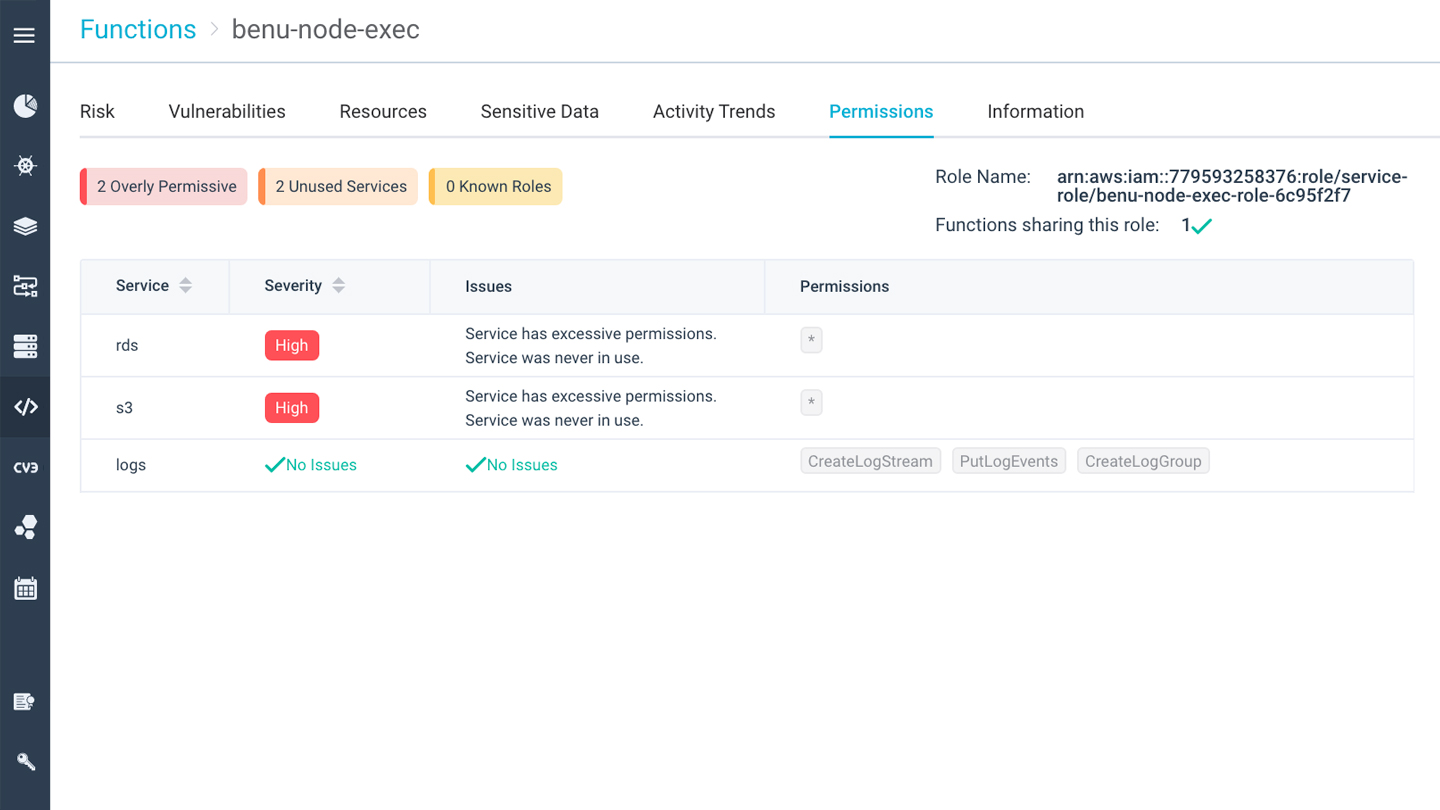
Ensure least-privilege permissions
A key risk in serverless functions is over-provisioned permissions, that allow a potential attacker to gain access to additional resources. Aqua prevents this by flagging over-provisioned permissions, as well as monitoring for unused permissions and roles over time, allowing you to reduce them to what’s needed.
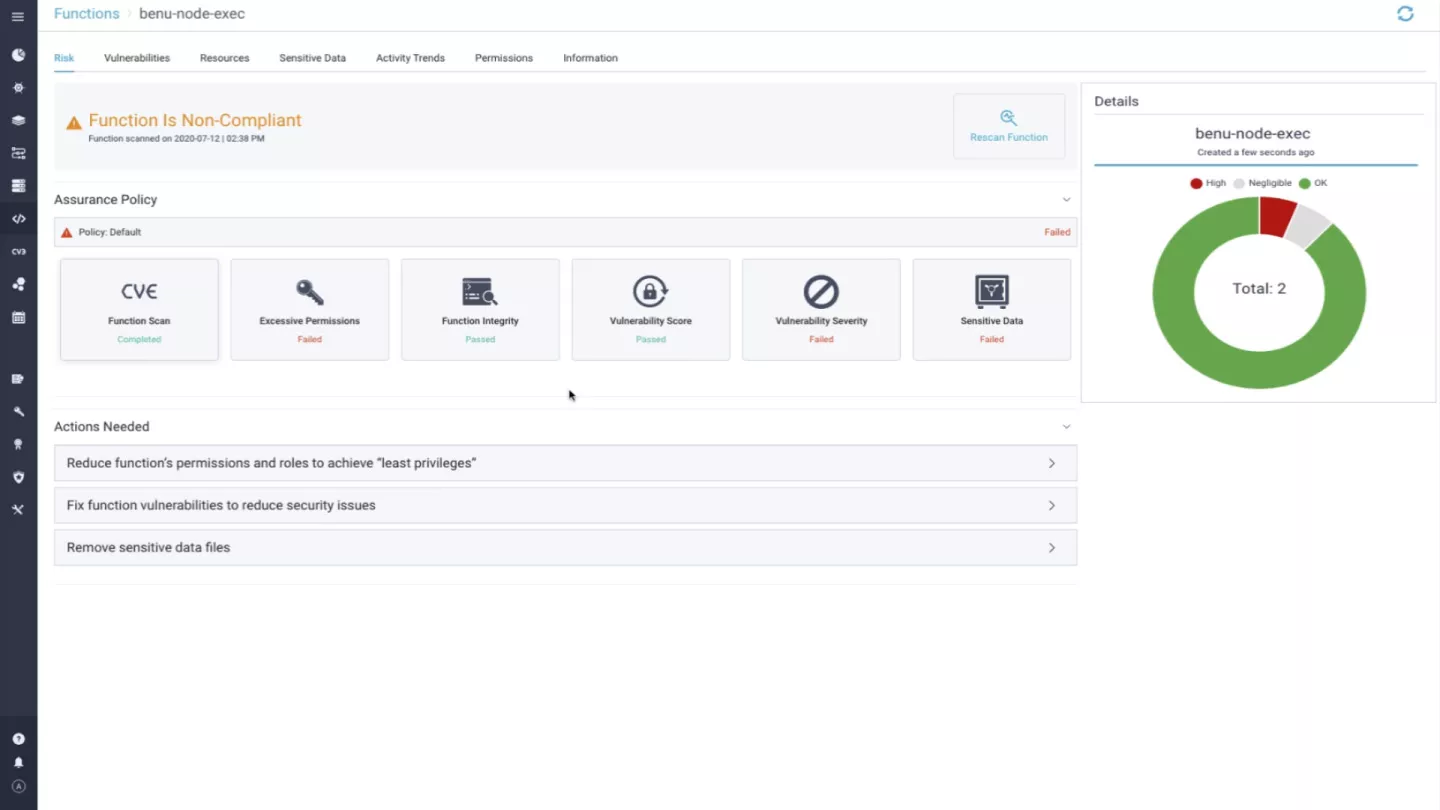
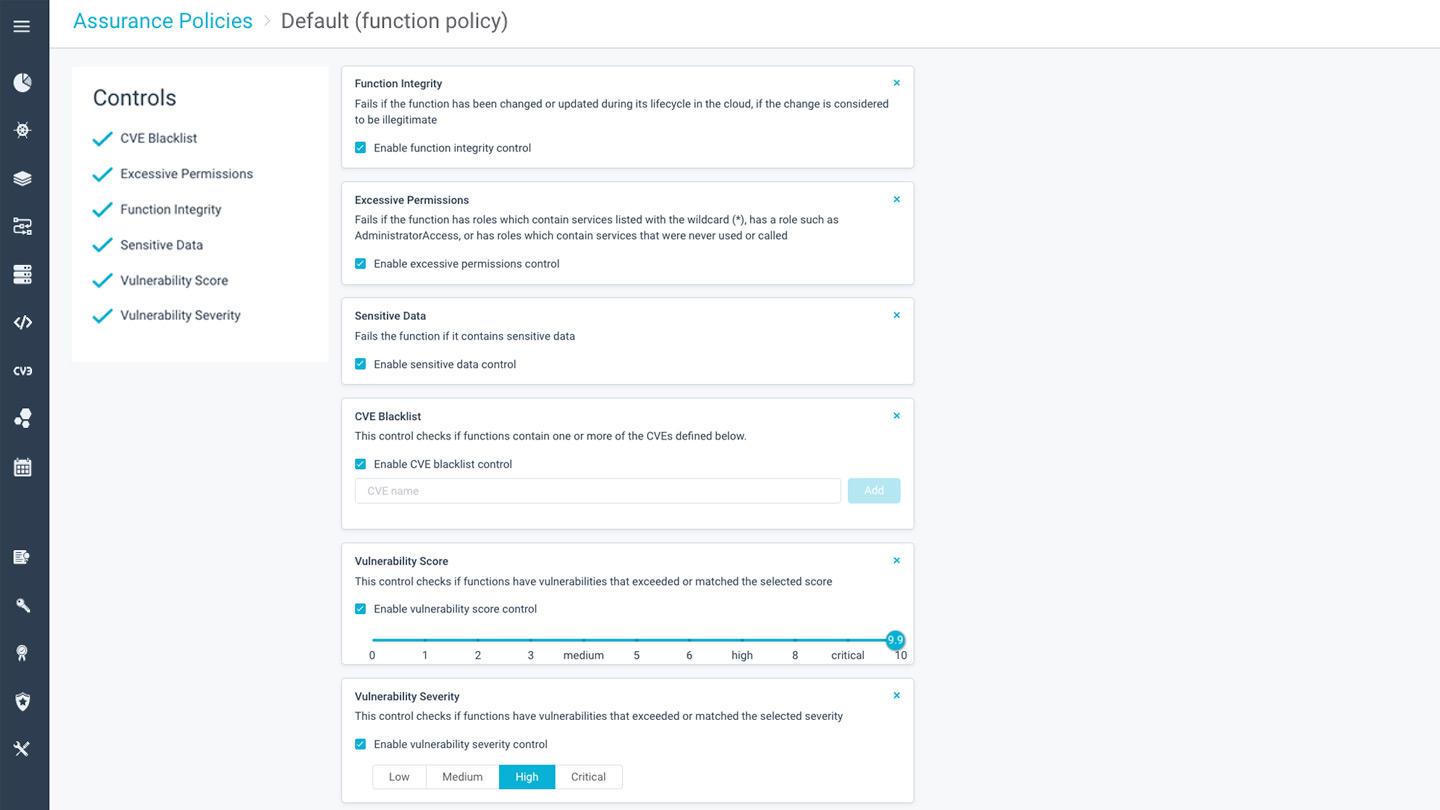
Control deployment of authorized functions
With Aqua’s flexible assurance policies, you can set policies that determine which functions are compliant and authorized for deployment based on their security posture, and conformance to our acceptable risk level. This includes any combination of vulnerability scores, permissions, malware, secrets, and other security-related configuration issues.
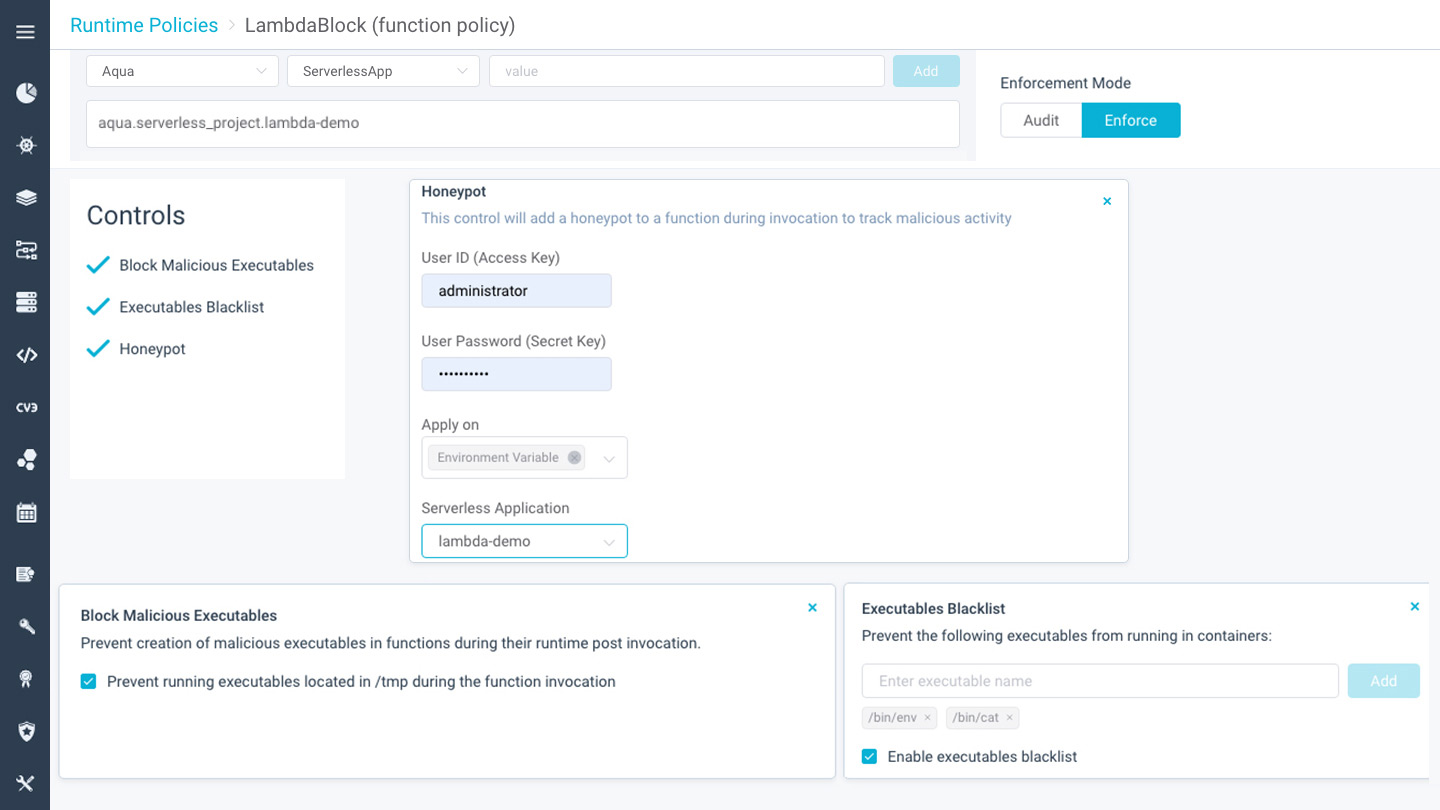
Protect AWS Lambda functions in runtime
Use Aqua’s small-footprint, highly performance-optimized and automatically deployed NanoEnforcers to protect functions in runtime. Aqua can block code injection attempts and unauthorized executables, as well as detect indications of compromise (IoCs) using function-embedded honeypots.