Enterprise-Grade Security for Docker Environments
Aqua provides end-to-end security for applications running on Docker Enterprise Edition or Community Edition, protecting the DevOps pipeline and production workloads in runtime with full visibility and control.
With Aqua, you can protect your Docker applications running on either Linux (docker or containerd runtimes) or Windows, with powerful image assurance, container immutability and least-privilege enforcement, and container firewall.
Integrate security controls
into your DevOps pipeline
Scan images within your CI tools, registries, and on Docker hosts to find and fix issues early, going beyond vulnerabilities to hard-coded secrets, bad image configuration, and malware.
Protect Docker applications
at runtime, in real time
Control the deployment of trusted images, enforce container immutability, and automatically learn and enforce least-privilege behavior to detect and prevent suspicious activity and attacks.
Apply enterprise-grade security to your Docker environment
Use Aqua's highly automated and customizable security policies to govern multi-tenant, multi-cloud and multi-orchestrator deployments, from development to production.
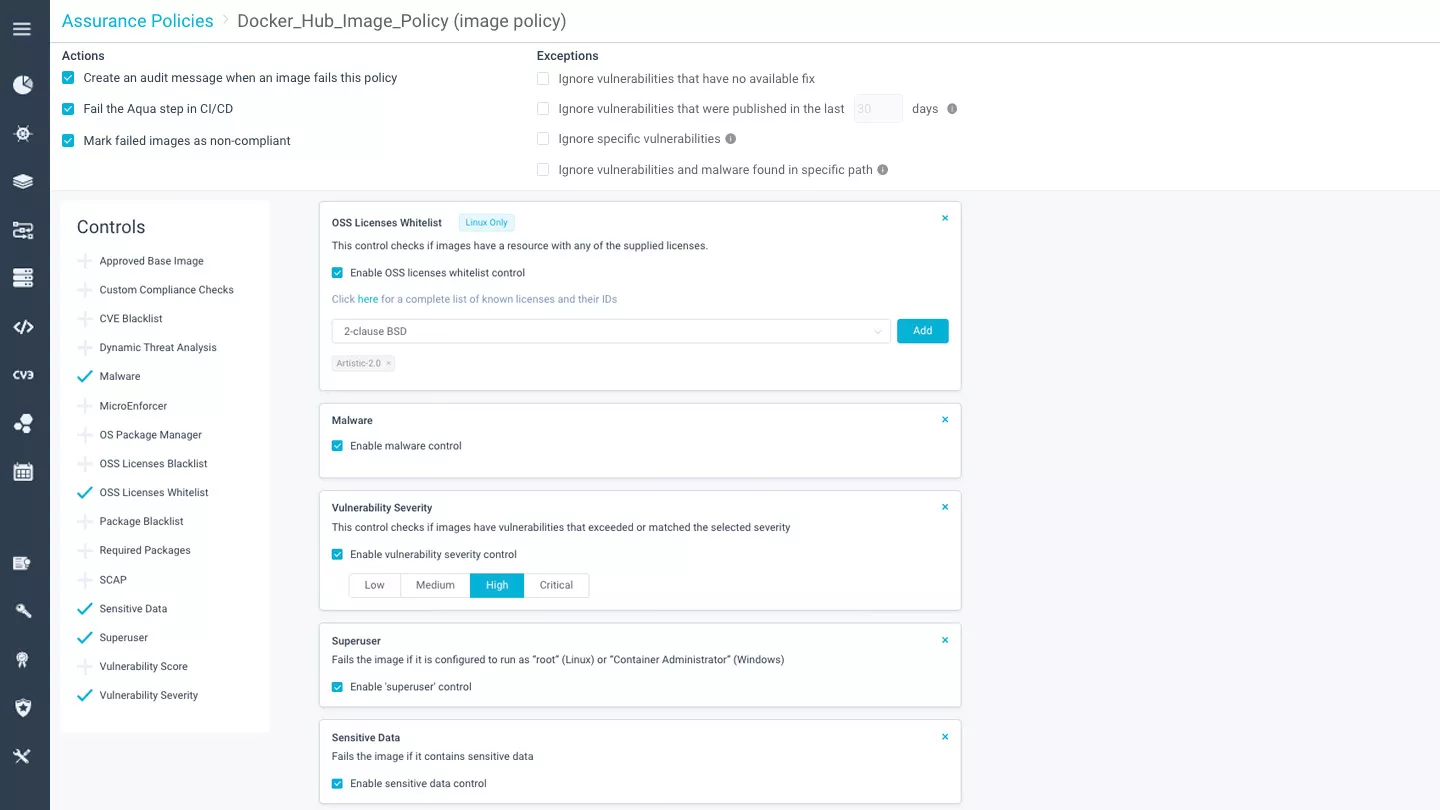
Continuous Image Assurance
Aqua scans images for vulnerabilities, malware, embedded secrets, configuration issues and OSS licensing, allowing you to create custom policies that determine which images will be allowed to run on your Docker hosts. Based on a constantly updated data stream, Aqua's vulnerabilities database is aggregated from multiple sources, and consolidated to ensure that only the most up-to-date data is included, increasing accuracy and reducing false positives and negligible CVEs.
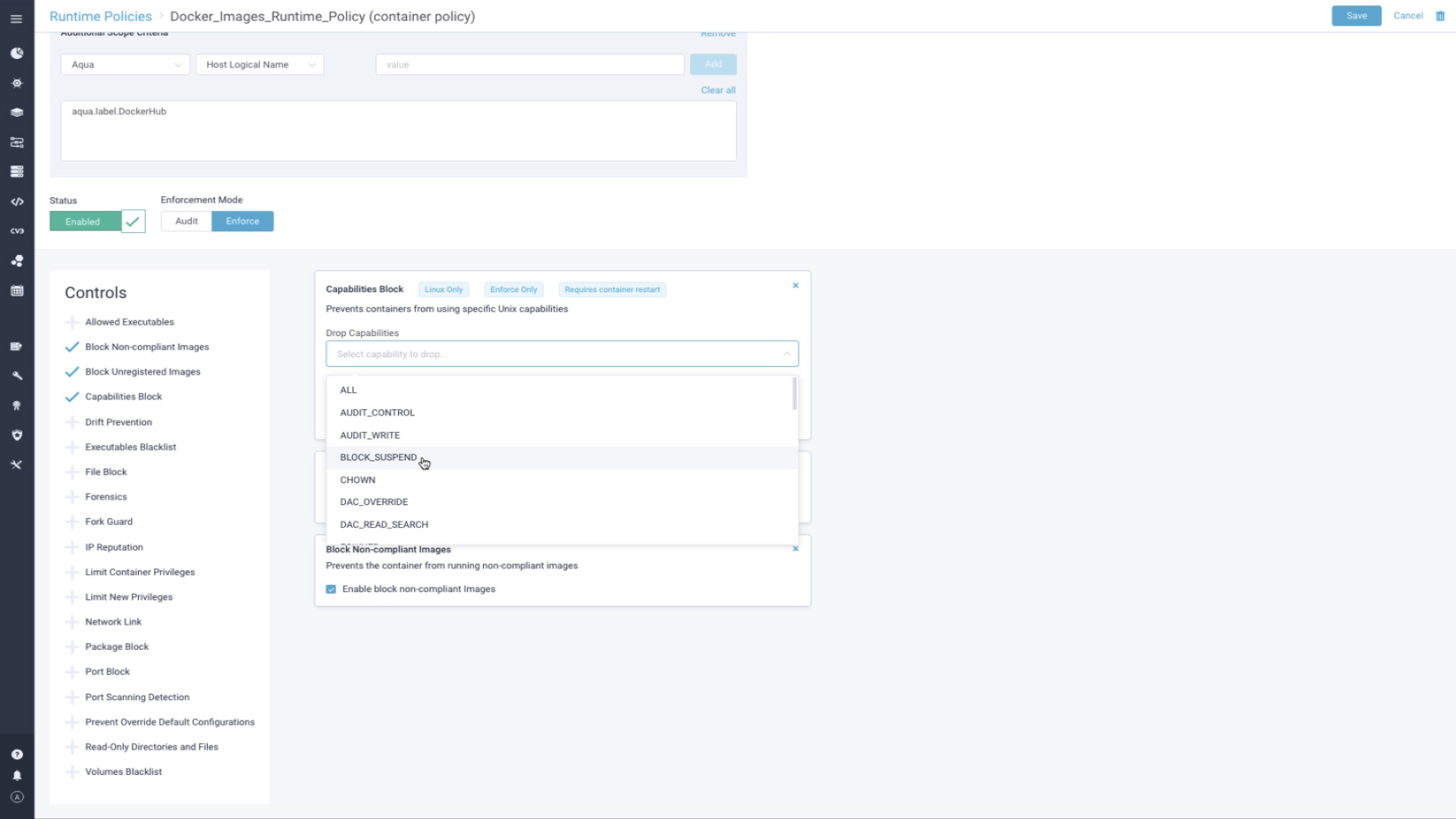
Runtime Security for Docker
Aqua provides multiple layers of security to protect Docker applications at runtime: enforcing container immutability and preventing changes to running containers, enforcing least-privileges using a machine-learned behavioral profile, isolating the container from the host by creating custom seccomp profiles, and controlling network connections with a container firewall.
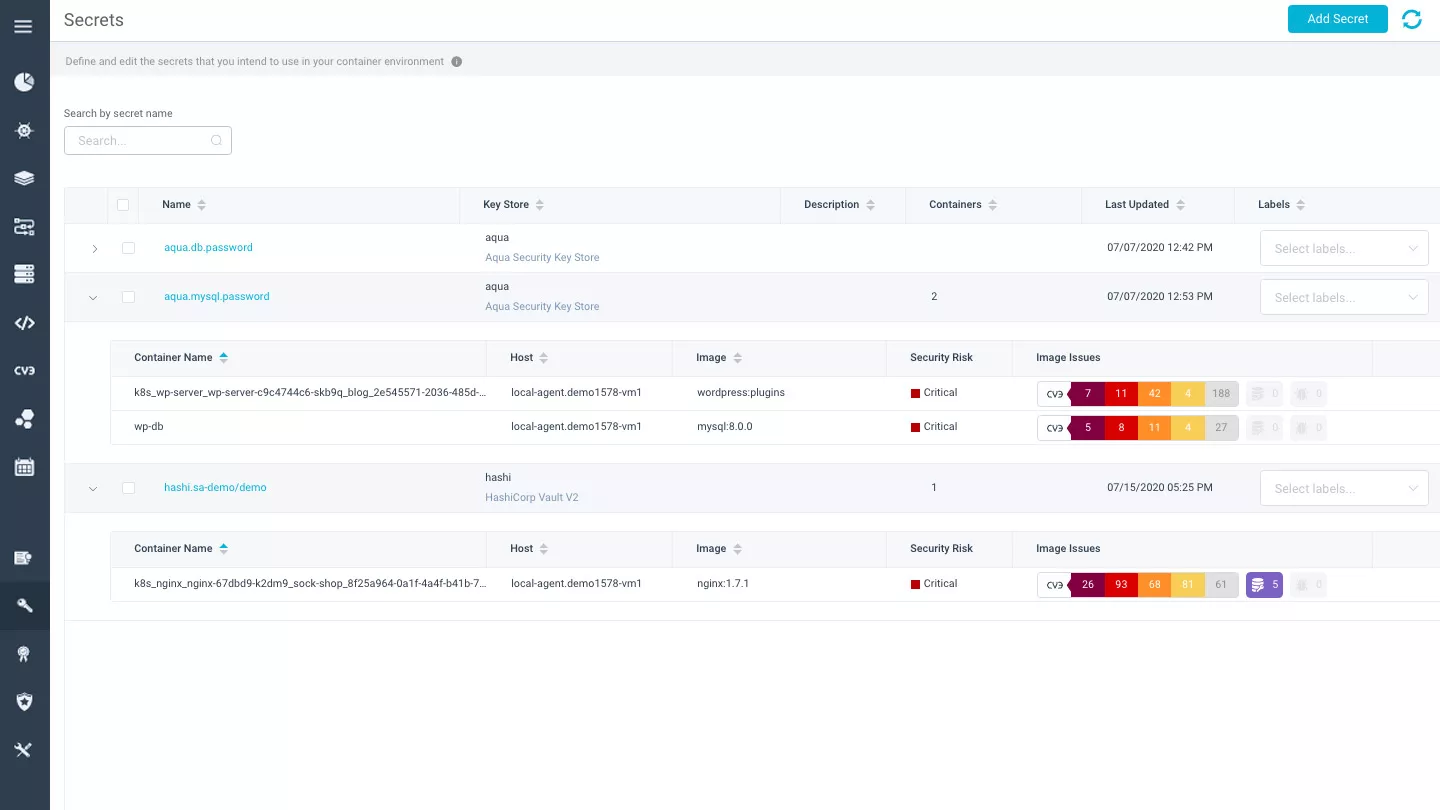
Secrets Management
Aqua securely delivers secrets to containers at runtime, encrypted in transit and at rest, loading them in memory with no persistence on disk, where they are only visible to the container that needs them. Integrate with your existing enterprise vault, such as Hashicorp, CyberArk, AWS KMS or Azure Vault. Unlike other secrets solutions, you can transparently update, revoke, and rotate secrets without restarting containers.
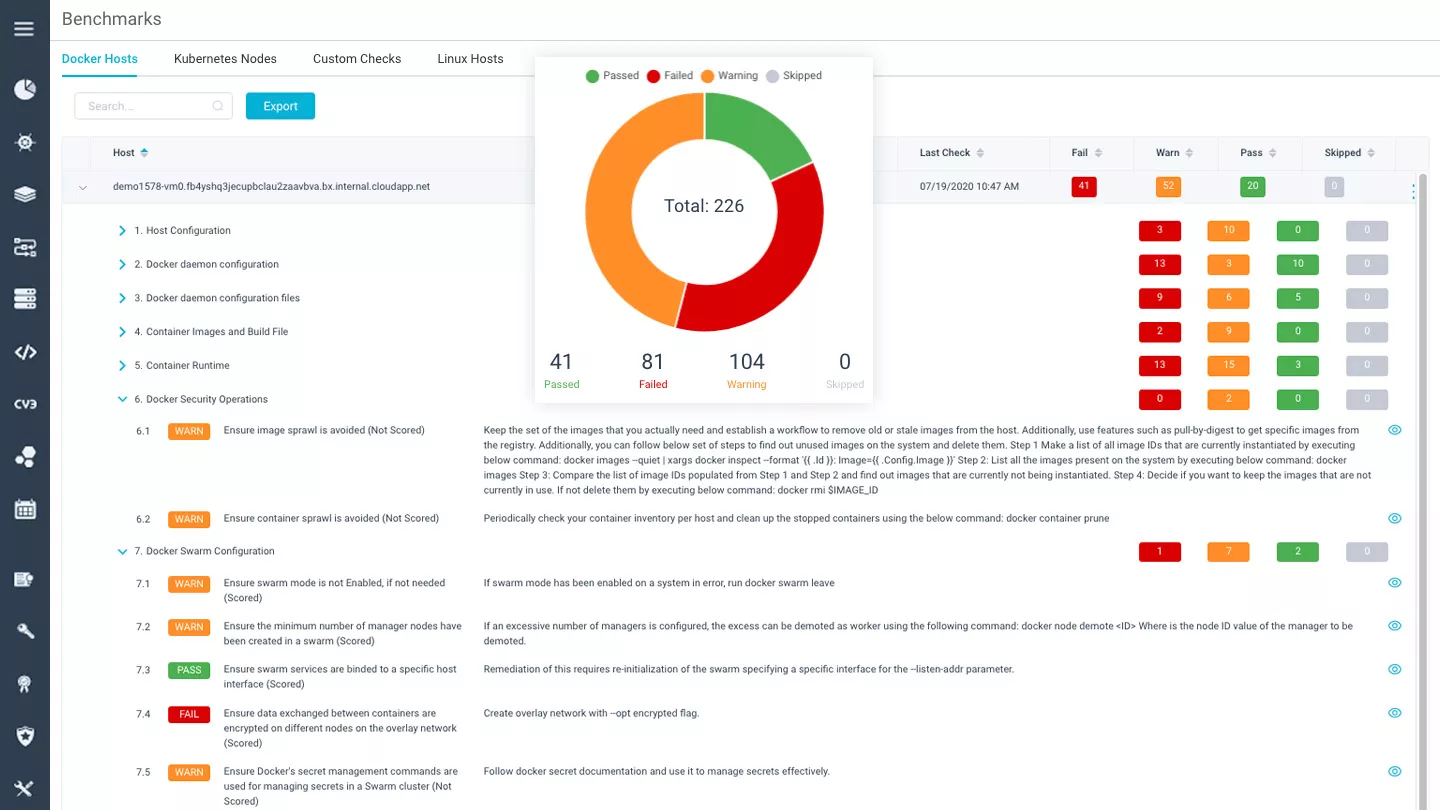
Docker CIS Benchmark Validation
Run compliance checks of your Kubernetes environment according to the CIS Docker Benchmark (in addition to Docker K8s Benchmark), that includes more than 100 individual checks to ascertain the environment's security posture. Aqua provides daily scans and a detailed report with the findings.
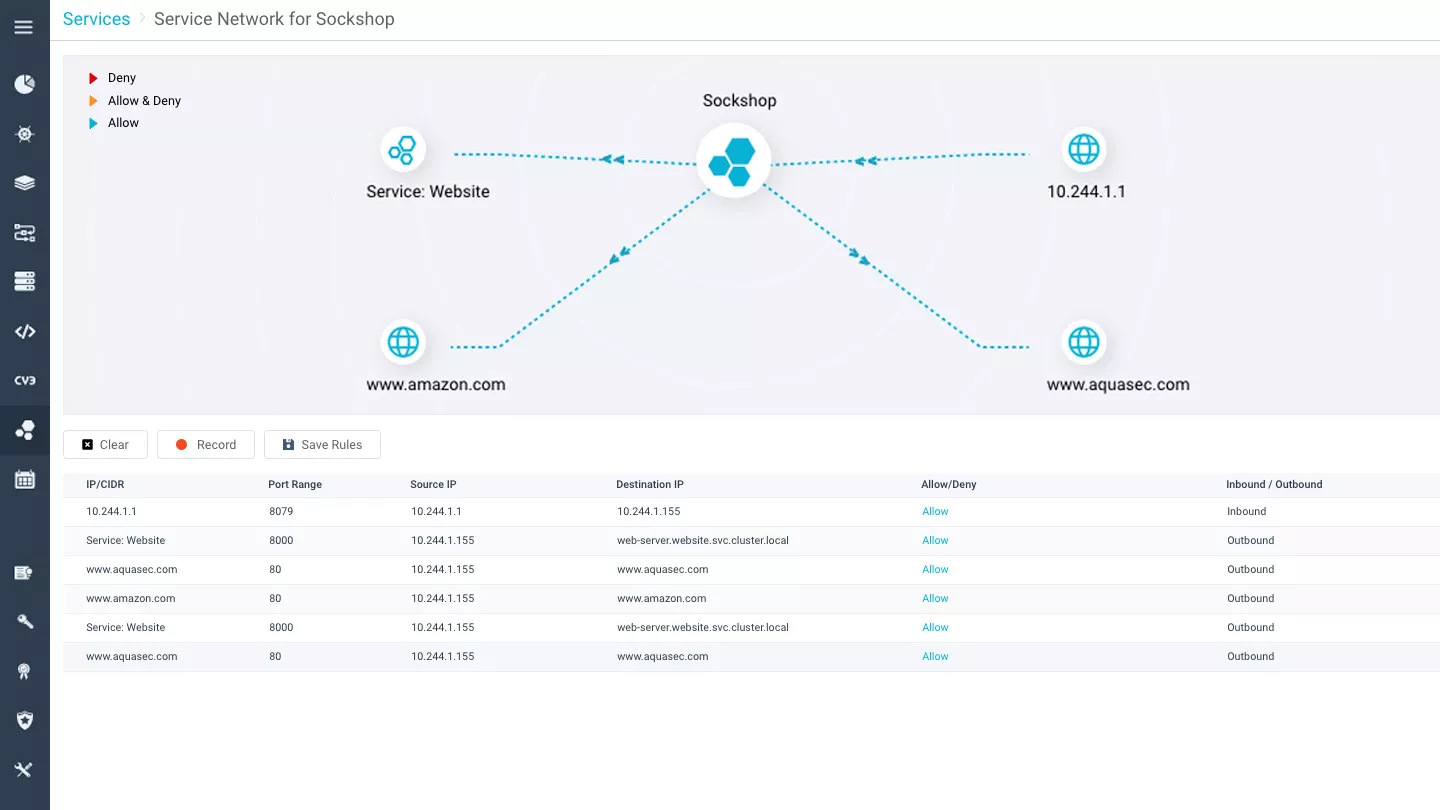
Container Firewall for Docker
Enforce container-level network rules with Aqua's container firewall - visualize network connection, automatically map legitimate connections, and create rules based on application services. Only whitelisted connections will be permitted, both within a Swarm or Kubernetes cluster, as well as between clusters.
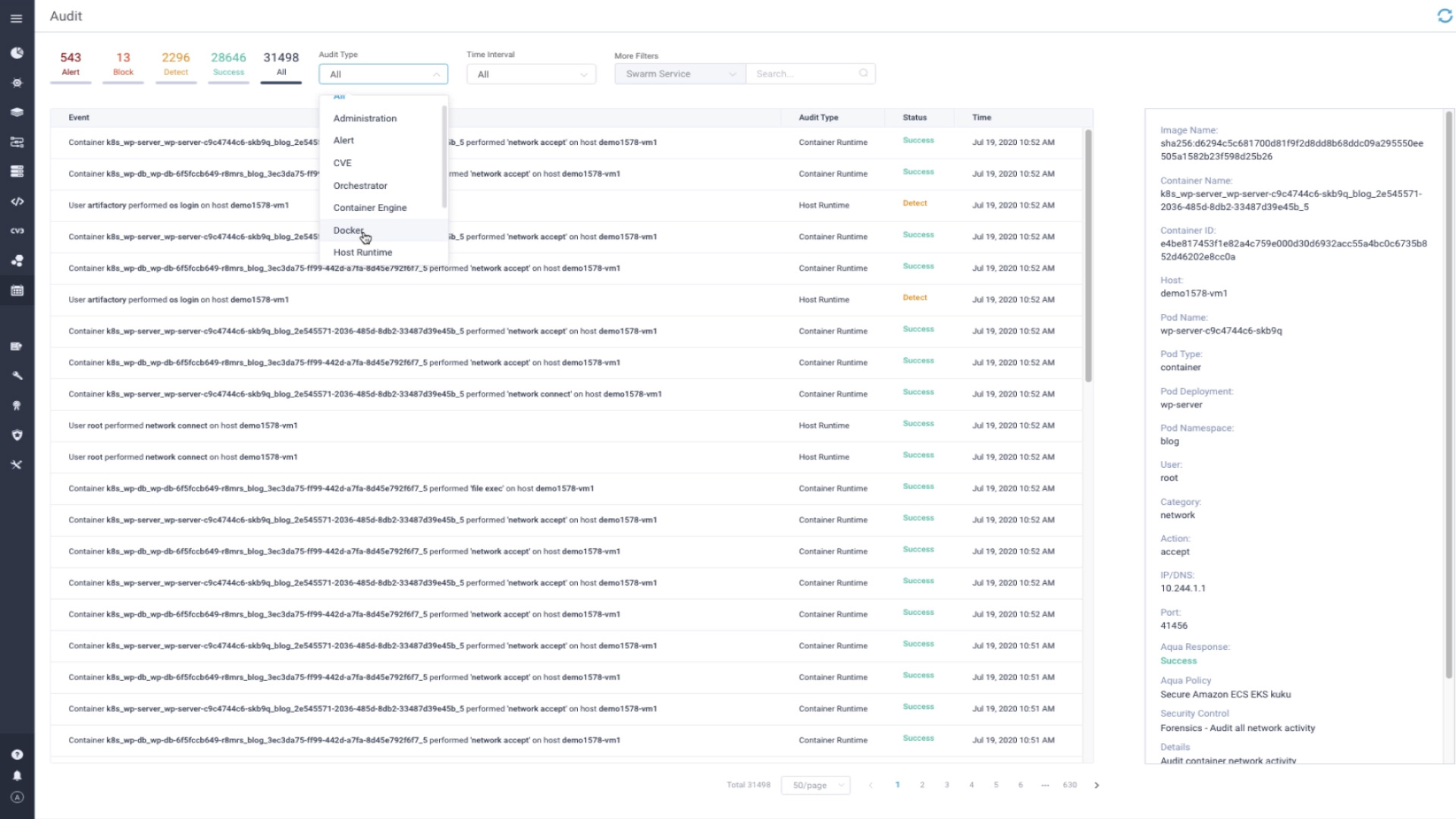
Granular Security Events Auditing
Aqua provides a detailed event stream of all Docker-related commands, such as start/stop of containers, user ID changes, and container security policy violations. This data can easily be transferred to a cloud monitoring, log management or SIEM tool of your choice, such as Splunk, ArcSight, Datadog or Sumologic.