Layered, Full Lifecycle Security for Enterprise PKS - Now part of VMware Tanzu
Aqua natively protects applications deployed on VMware Enterprise PKS and Pivotal Container Service (Now Tanzu Kubernetes Grid Integrated)
Aqua for VMware TanzuFull lifecycle security for your PKS environment, from CI/CD to runtime protection. Gain visibility into the security posture of your entire pipeline, with granular threat detection and mitigation controls that prevent attacks and ensure compliance.
Defense in Depth for Enterprise PKS
Complement PKS security features with preventative as well as attack detection and response features, avoiding a single point of failure while enforcing segregation of duties.
Trusted for PKS Security
Aqua is VMware Partner Ready for PKS, verified to work on both VMware Enterprise PKS and Enterprise Pivotal Container Service.
Aqua Security for PKS protects your enterprise clusters against configuration drift, administrator errors, and malicious attacks.
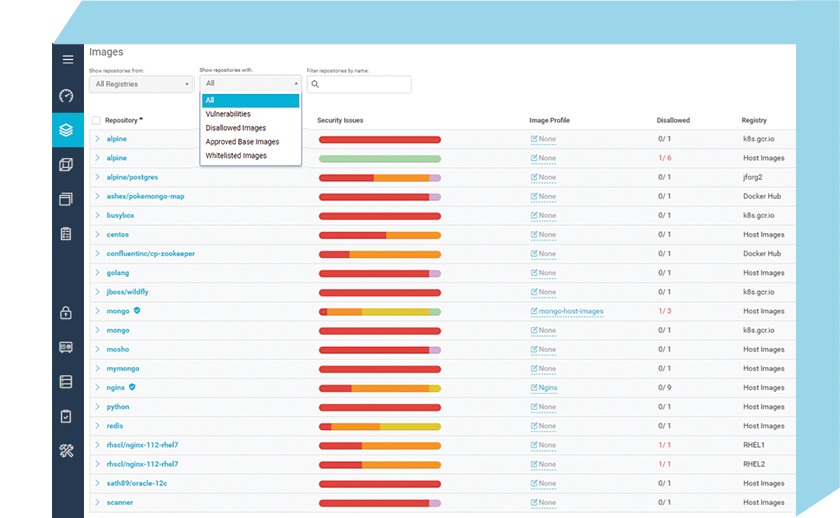
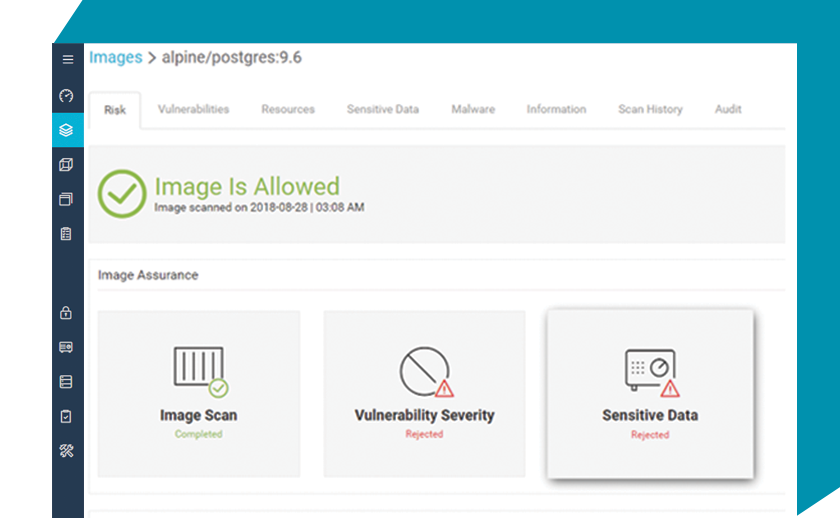
Manage Risk in the Container Development Pipeline
Scan images in your CI/CD pipeline, as they are pushed into your Harbor Registry, to verify that DevOps teams do not introduce vulnerabilities, bad configurations, and secrets into container images. This prevents unauthorized images from running anywhere across your PKS clusters.
Protect Applications in Runtime
Ensure that containers and pods only do what they are supposed to do in the application context, by leveraging machine learning to whitelist normal container behavior. Get alerts on and automatically prevent policy violations around usage of host resources, privilege escalation, network traversal, and code injection attempts. Defend against specific attack vectors targeting containerized applications.
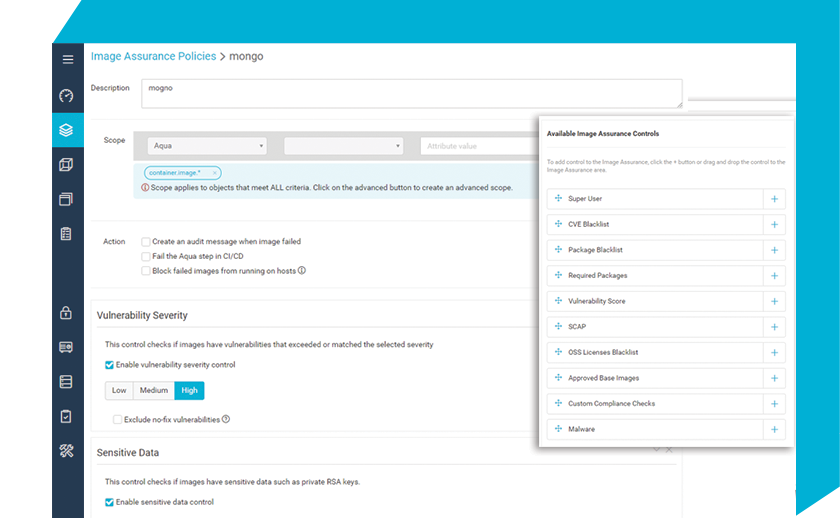
Automated Compliance Checks
Perform custom compliance checks to identify security and compliance violations of regulatory requirements for PCI, HIPAA, GDPR, and more, enforcing compliance policies in your application development and delivery pipeline.
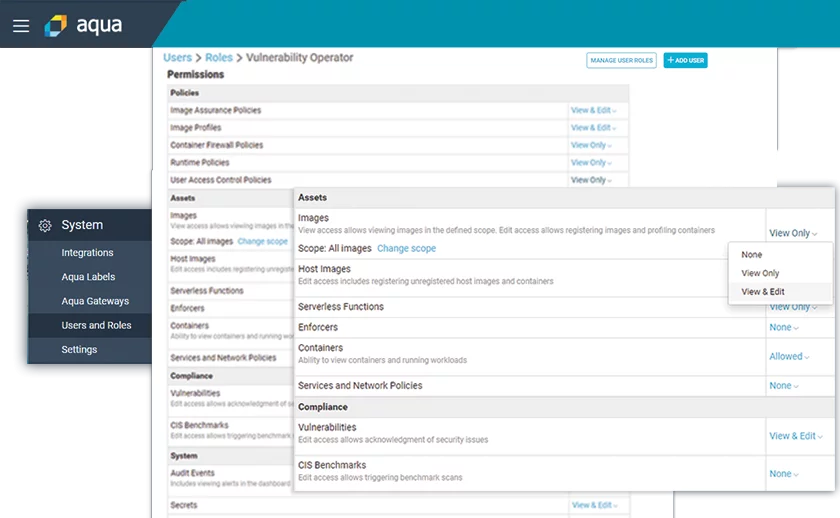
Enable Multi-Tenant Security Governance Across Teams and Roles
Make DevSecOps a reality by allowing stakeholders to define policies, monitor security posture, audit security events, and remediate issues according to their roles and required privileges, while maintaining strict segregation of duties and governance.
Aqua Security has validated its Cloud Native Security Platform for VMware Enterprise PKS. This signifies to customers that Aqua Security can be deployed with the knowledge and reassurance that Aqua fully supports the specified versions and configurations on VMware Enterprise PKS.
 Pat Lee
Pat LeeVice President, Emerging ISVs & Solutions, VMware
