Cloud Native Security for Red Hat OpenShift
Aqua provides a full-stack security solution for enterprises using Red Hat OpenShift to deploy their cloud native applications, extending OpenShift's native capabilities to provide runtime protection and secure secrets delivery.
A certified container security platform for Red Hat OpenShift and an OpenShift Primed partner, the Aqua Container Security Platform is deployed natively on Red Hat OpenShift for both Linux (using Docker or CRI-O runtimes) and Windows containers, offering image assurance, runtime controls, protection against attacks, as well as increased visibility and compliance for containerized applications.
Maximize security across all phases and layers
Keep your development pipeline and production environments safe by ensuring the use of trust images, monitoring hosts, controlling network traffic, and safeguarding secrets.
Protect OpenShift application workloads in real time
Continuously monitor running containers to detect and automatically block unauthorized container activity, protecting applications against privileged user errors and 0-day attacks.
Accelerate risk analysis and remediation
Get granular visibility at any time, and perform instant impact analysis for compliance auditing, event forensics, or remediation of vulnerable images, packages and hosts.
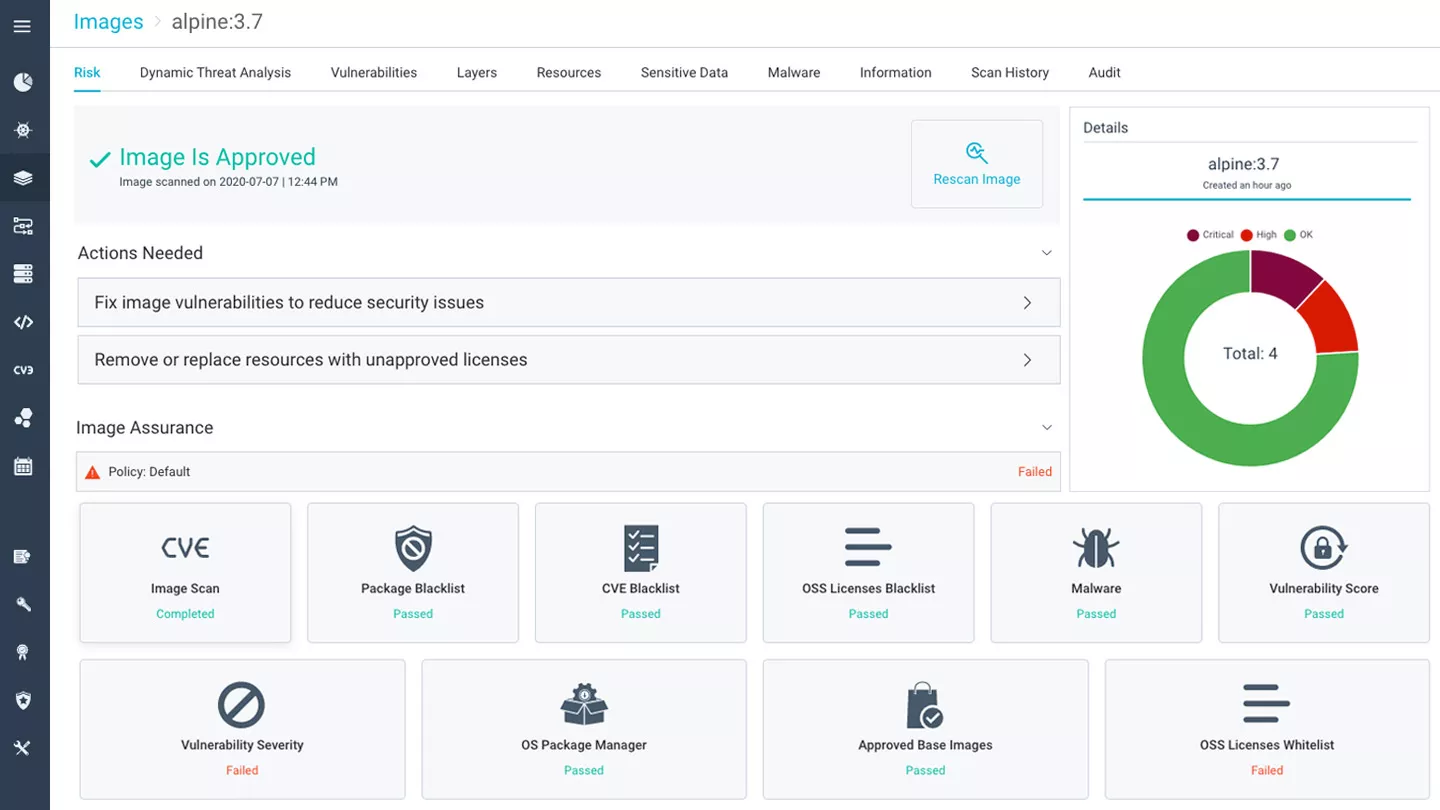
Manage Risk in the Container Development Pipeline
Continuously scan the Red Hat OpenShift Registry to verify that DevOps teams do not introduce vulnerabilities, bad configurations, and secrets into container images, and prevent unauthorized images from running in Red Hat OpenShift Container Platform environments.
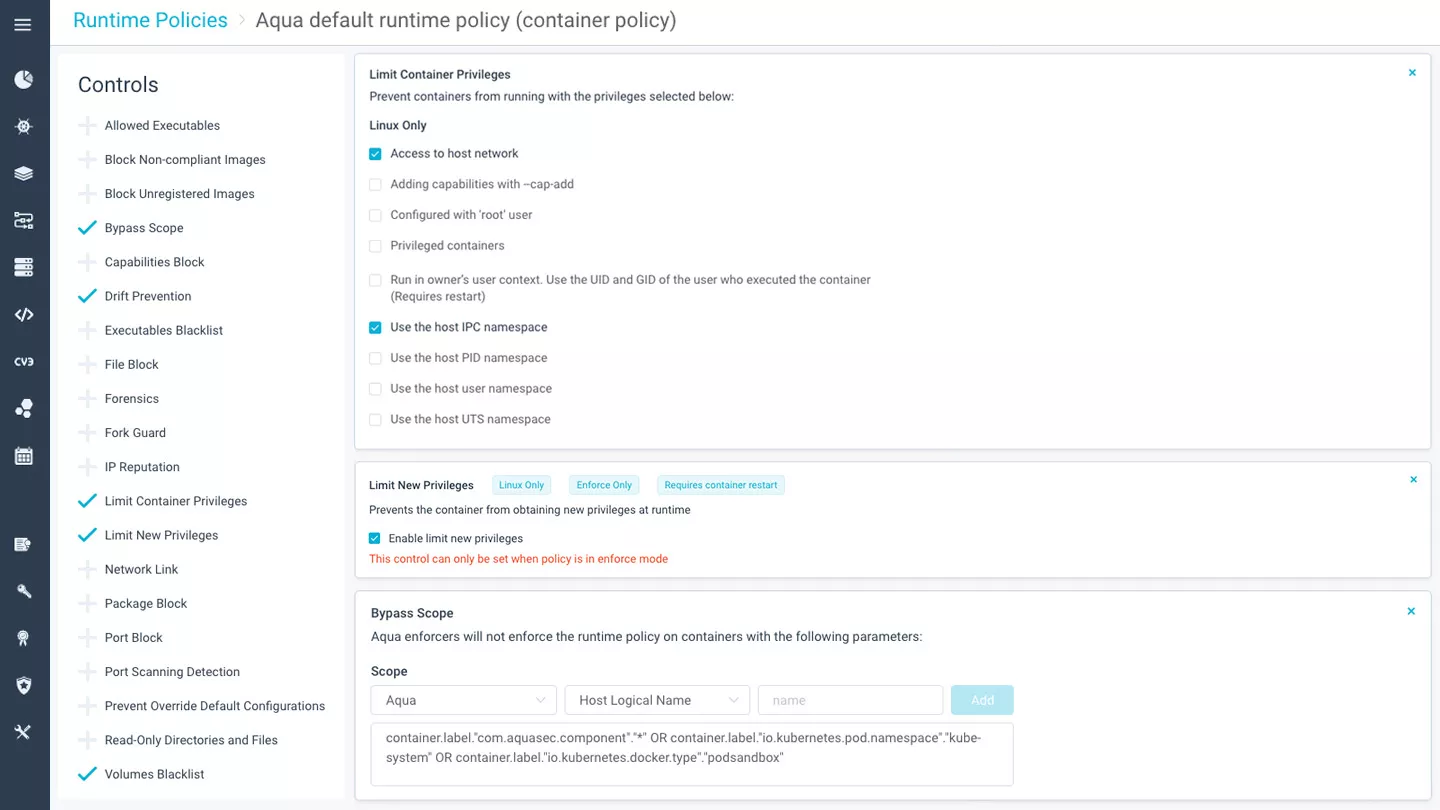
Protect Applications in Runtime
Ensure that containers only do what they are supposed to do in the application context, by leveraging machine learning to whitelist normal container behavior. Get alerts on and automatically prevent policy violations around usage of host resources, role-based user access, and network activity. Defend against specific attack vectors targeting containerized applications.
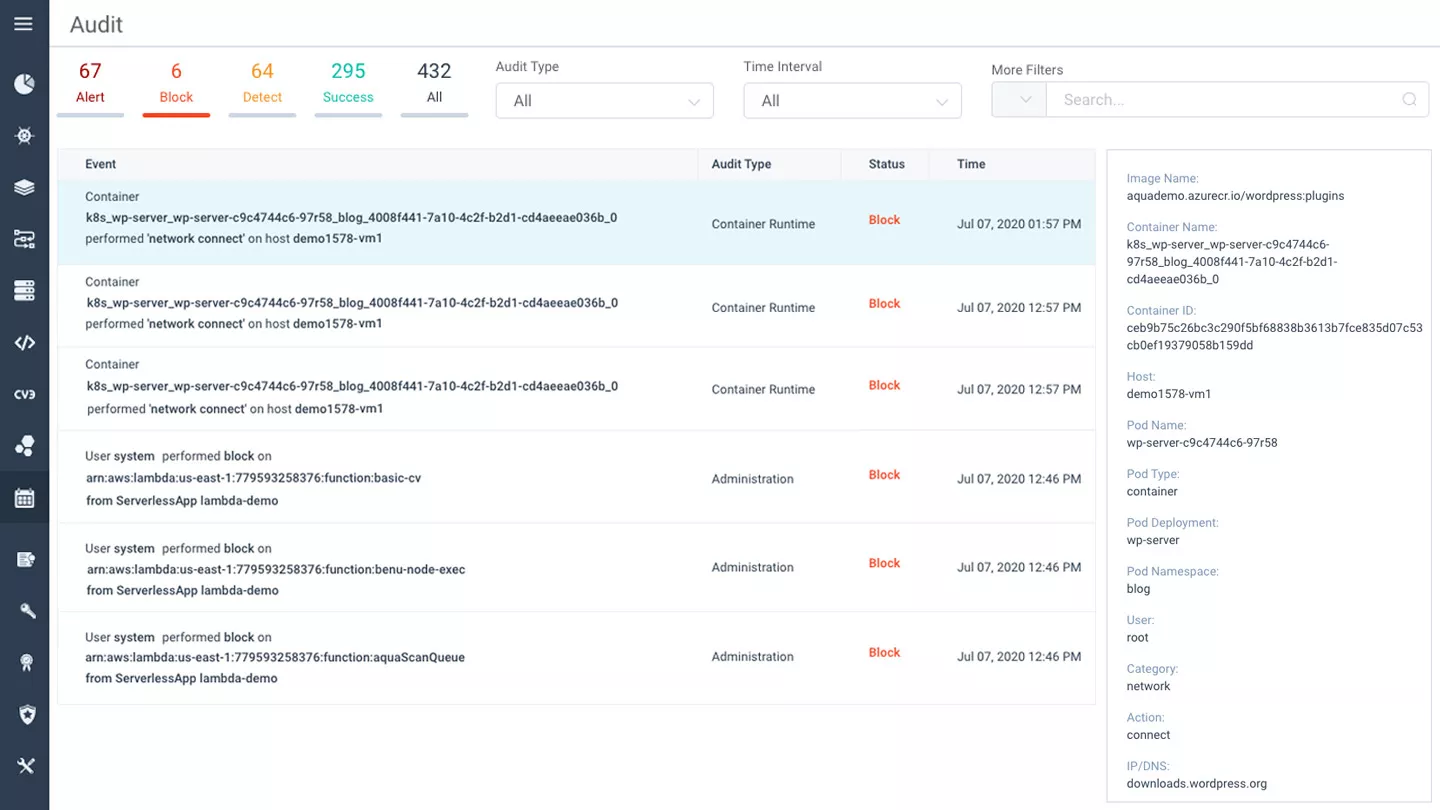
Achieve Visibility and Compliance
Monitor container activity in real-time, gain full visibility and audit trail into containers deployed in Red Hat OpenShift Container Platform. Log events, such as access attempts, network access, running executables, privilege escalations and more, and produce reports for regulatory compliance requirements, such as PCI DSS, HIPAA, and GDPR.
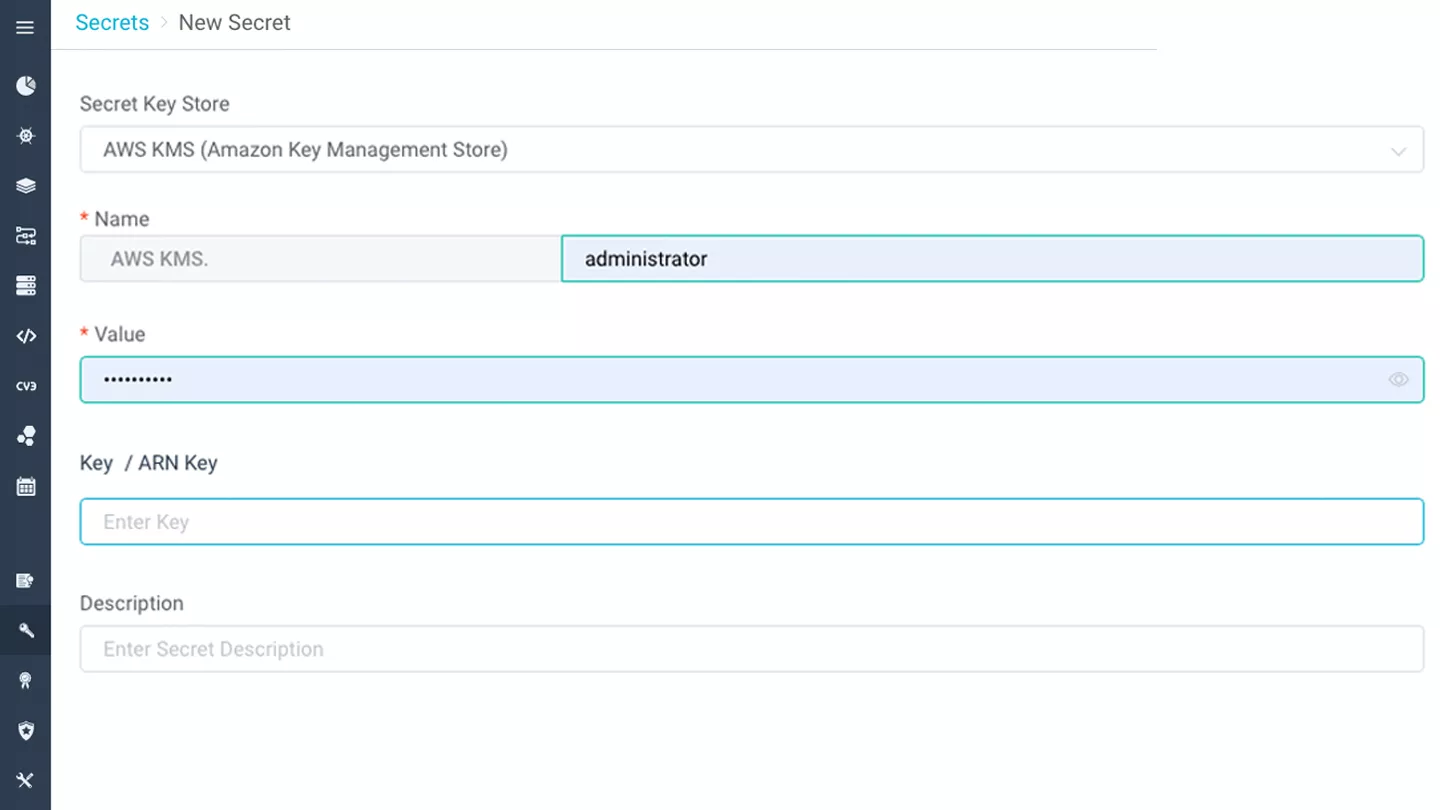
Securely Inject Secrets into Containers
Securely inject secrets, such as passwords, keys and tokens, into containers in runtime, with no container downtime. Leverage your existing enterprise secrets stores, such as HashiCorp Vault and CyberArk Enterprise Password Vault, and easily manage, rotate, and revoke secrets in containers, running only in memory with no persistent storage on disk.
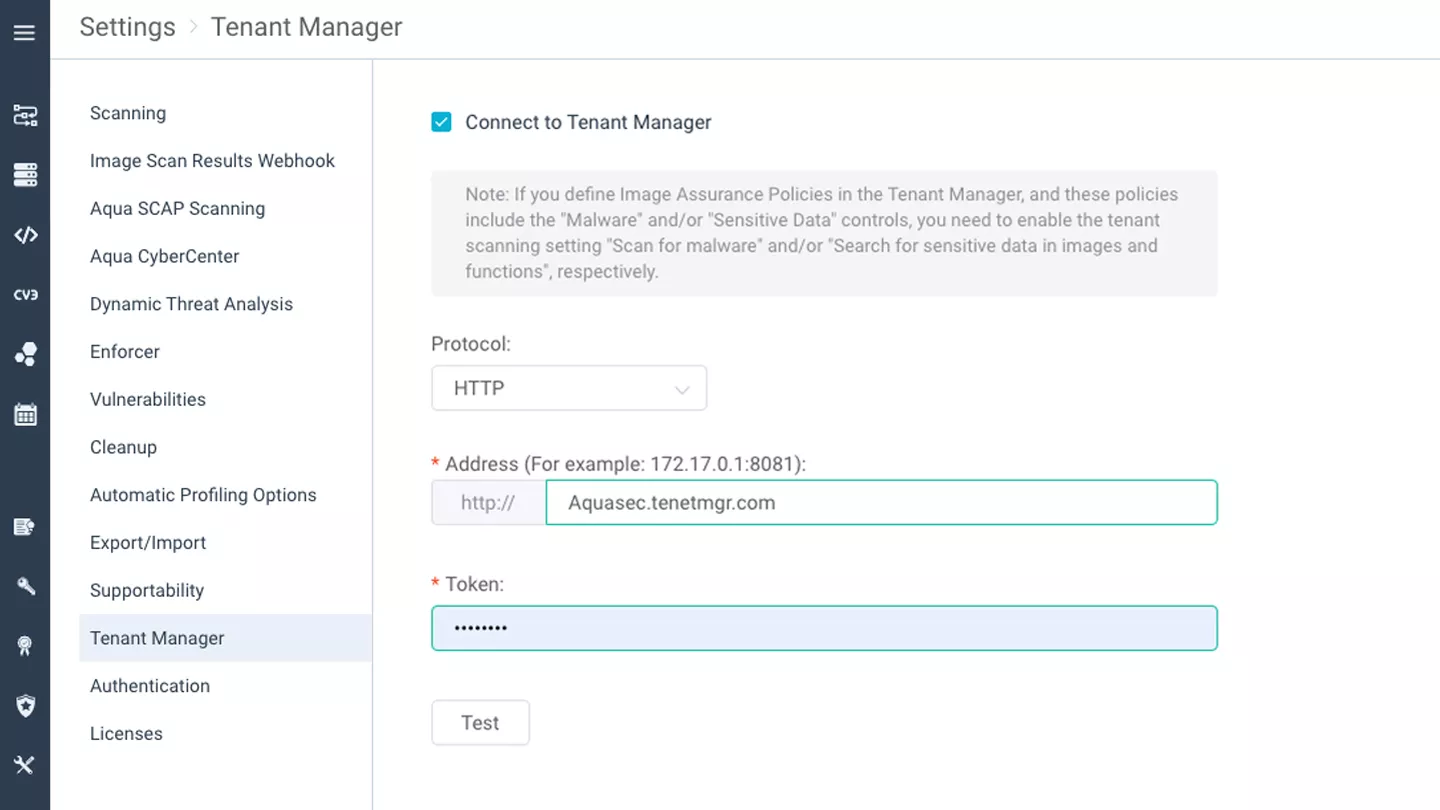
Multi-Tenancy Management
Support multiple tenancies through delegation of management capabilities, such as image security assurance policies, container runtime policies, etc.
Data and reports from the tenant levels roll up to the top level, allowing admins to monitor and enforce policies on a global level.