While more and more companies are moving to a cloud native technologies to manage their workloads and infrastructure, Virtual Machines (VMs) remain a staple infrastructure that powers many existing organizations and applications. Trivy, the all-in-one open-source security scanner, already scans most of the cloud native stack including containers, clusters, and clouds. Today, we are announcing that Trivy can also scan Virtual Machine Instances on AWS for security issues.
In this blog, we showcase the architecture behind VM scanning and how to perform different kinds VM scans in AWS with Trivy.
Trivy VM scanning is now available under the ‘trivy vm’ command. Currently, there are two main use cases supported:
- Scanning VM images – from AWS AMI
- Scanning VM filesystem volumes – from AWS EBS
Further use cases are provided in the Trivy documentation.
Scanning raw images
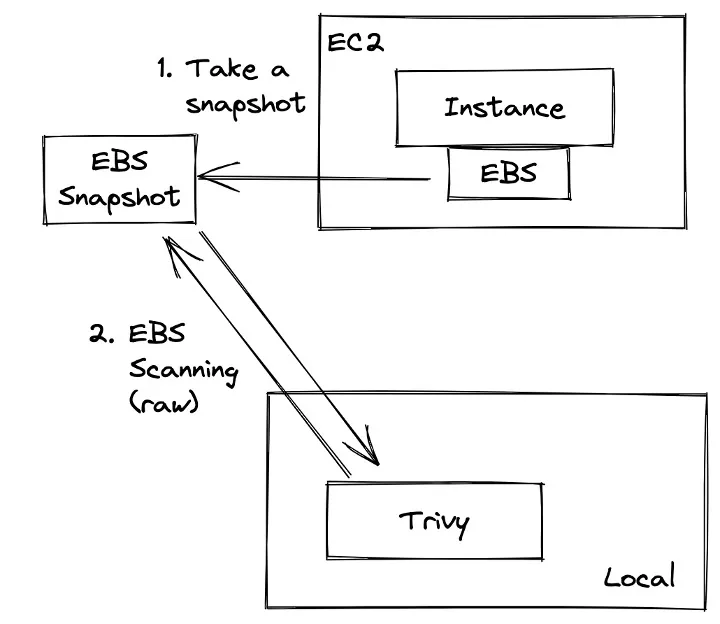
If you wanted to scan Virtual Machines Images with existing tools, you probably had to start a new VM instance with the target volume attached and then install a scanning agent inside of the VM so that it can have access to the filesystem contents. This practice is very popular and has been adopted across tools.
Trivy, on the other hand, takes a cleaner approach in analyzing the raw VM image at rest through EBS volumes.
This provides us with several benefits including:
- Trivy is easier to install and use across your environments. Trivy does not have to run an EC2 instance to attach and scan your volume. Instead, you merely need to provide the AMI or EBS ID to your Trivy command, and Trivy can perform the VM scan. This is a very user-friendly approach without creating any downsides.
- The Trivy VM scan is more secure since it requires the least permission to your resources. Starting an instance requires excessive permissions just for a scan (access to volume, permission to start instance, ssh into instance, fs permission to read the entire fs). In comparison, Trivy only needs read-only access to the EBS blob.
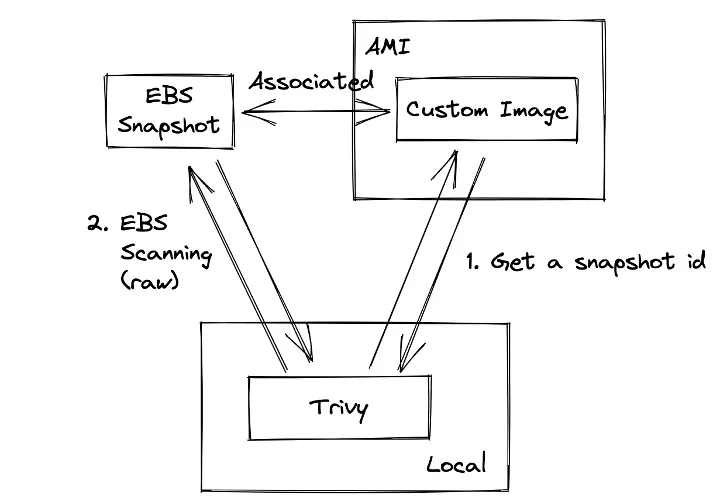
AMI Scanning
Trivy can analyze VMDK image files, compressed or uncompressed. However, the process for exporting and downloading the VMDK image in AWS is complex. Instead, Trivy makes it possible to scan the AMI image directly by providing the AMI ID to the scan. AMI images use EBS snapshots under the hood. This way, Trivy can find the snapshot through the AMI without requiring the VMDK.
Amazon Elastic Block Store (EBS) scanning
Trivy can also analyze AWS EBS volumes directly through the EBS volume ID. Trivy is optimized to identify which blocks contain valuable information for the security scan so that it is as efficient and quick as possible. Upon analyzing a block, Trivy checks which files are needed for vulnerability scanning. The downloaded blocks contain file paths and permissions, not file contents. When the file content is required, Trivy downloads the according block.
For instance, for a RHEL 8 snapshot with 10GB and 20480 blocks, Trivy only downloads 716MB with 1432 blocks for vulnerability scanning. It’s much faster than downloading the entire EBS snapshot. Note that Secret and Misconfiguration scanning will download a lot more blocks since more files would be required.
Tutorial
In this section, we will showcase the two different types of VM scanning with Trivy discussed above. Trivy makes it possible to scan virtual machines in your Amazon account directly through the Trivy CLI without pulling the VM image or running it locally.
Prerequisites
To follow the tutorial, make sure to either upgrade the Trivy CLI to the latest version or to install the CLI. All installation options are listed in the documentation.
Additionally, ensure that you are connected to your Amazon account through the CLI.
Command
The trivy vm command follows the standard trivy convention. You can find all the options and examples by running trivy vm in your terminal:
$ trivy vm
Scan a virtual machine image
Usage:
trivy vm [flags] VM_IMAGE
Examples:
# Scan your virtual machine image
$ trivy vm export-ami.vmdk
# Scan your AWS EBS snapshot
$ trivy vm ebs:${your_ebs_snapshot_id}
# Scan your raw disk image
$ trivy vm snapshot_id.img
.
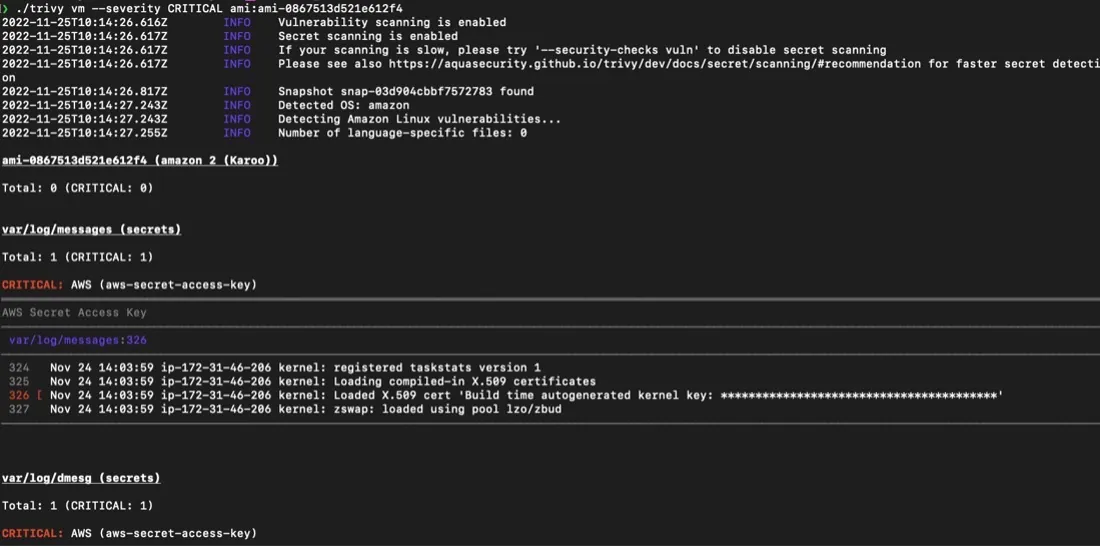
Custom AMI Scanning
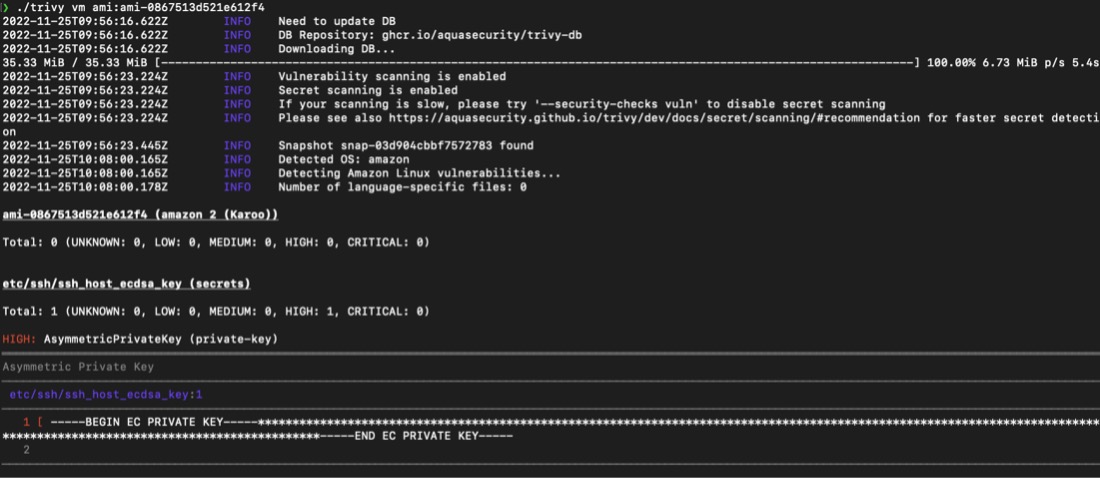
This will provide us with a long list of security issues. Like other Trivy commands, you can now narrow down the scan result through additional flags such as –severity CRITICAL.
Amazon
You can also scan snapshots of virtual machines in your Amazon account.
List all the snapshots of your volumes:
aws ec2 describe-snapshots
Then, you can scan a specific volume by passing the Snapshot ID into the Trivy CLI:
trivy vm ebs:${SNAPSHOT_ID}
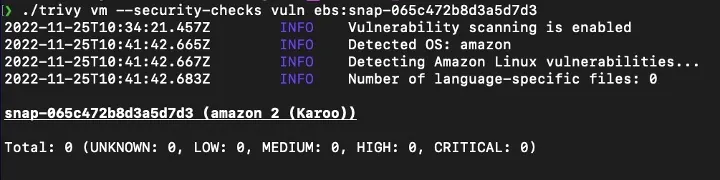
This will show us any security issues, including vulnerabilities, exposed secrets, and misconfiguration:
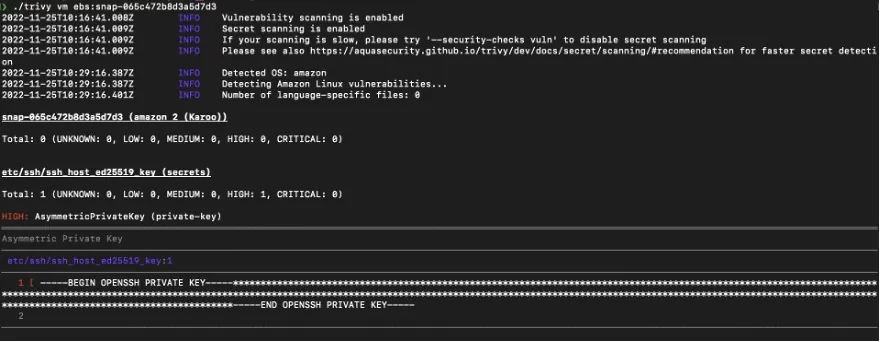
Additionally, we can filter the scan to just check for vulnerabilities in the EBS snapshot with the additional flag --security-checks vuln:
trivy vm --security-checks vuln ebs:${SNAPSHOT_ID}
Get involved
In this blog, we showcased the new Trivy VM scanning capabilities after providing an overview of its architecture.
If you are completely new to Trivy, have a look at its other functionality – and if you like what you see, give us a Star on GitHub ⭐
Additionally, join the Slack community if you have any questions.