A standard piece of security advice is to reduce the size of your container images, usually by using statically compiled binaries in a scratch or distroless container. However, that complicates container vulnerability scanning, because it becomes impossible to determine the versions of software installed in a container image. Fortunately, if you’re using Trivy, a popular open source scanner, a couple of useful features can help solve this problem.
Golang binary scanning
The first option is to use Trivy’s Golang binary scanning feature. This enables Trivy to look inside compiled Golang programs and extract module information, which then allows for vulnerability analysis to take place.
Trivy takes advantage of the fact that, by default, the Golang compiler will embed module information into its binaries.
As an example of this scanning, a container image with several Golang programs will produce output like this:
trivy i raesene/alpine-containertools
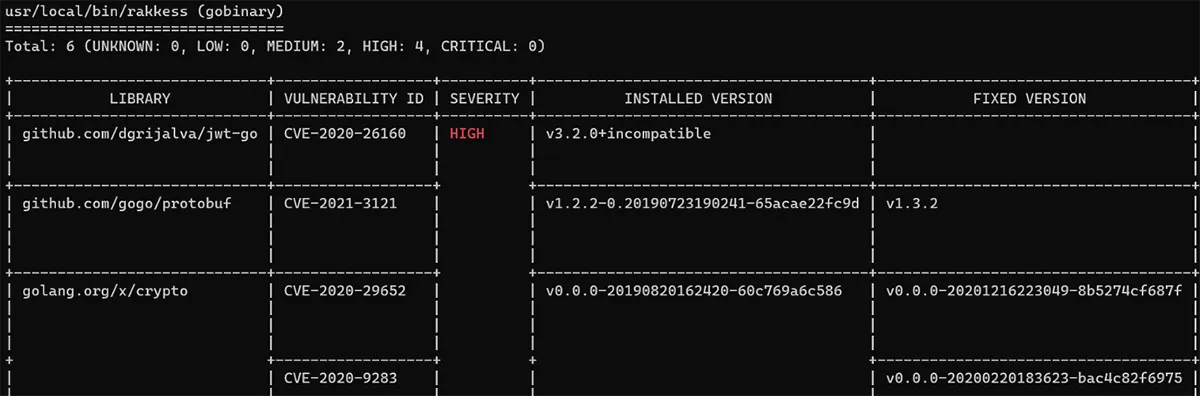
This shows the location of the binary scanned and the resulting vulnerability information.
Of course, there are times when compiled binaries won’t provide the information we need. For example, the Caddy project strips module information from their released binaries, so if we scan their container image, we’ll get something like this:
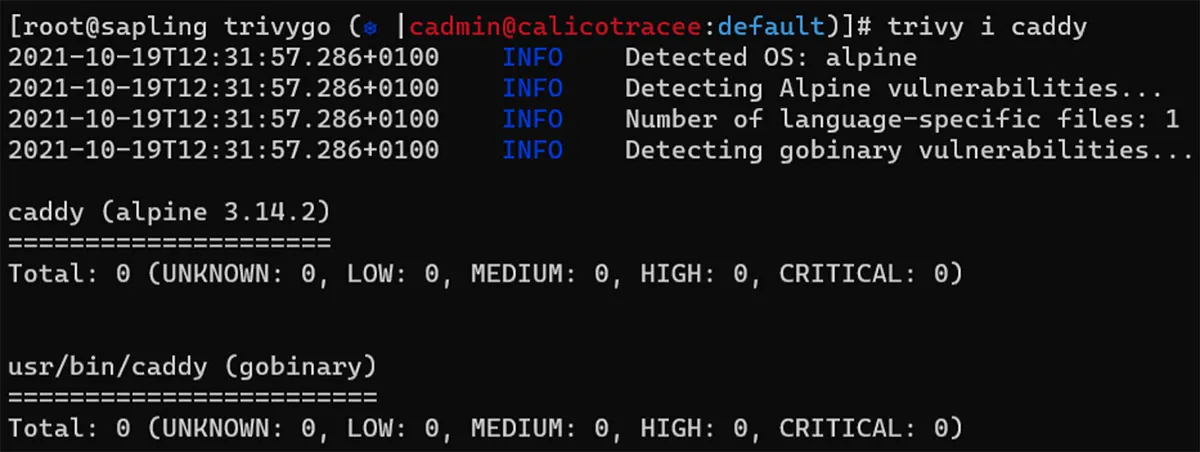
In cases like this, we need another approach.
Scanning GitHub repositories
When it’s not possible to scan binary programs, but the source code is available online, you can use Trivy to scan the repository to get a view of vulnerable library versions. For the Caddy project, this would look like this:
trivy repo https://github.com/caddyserver/caddy
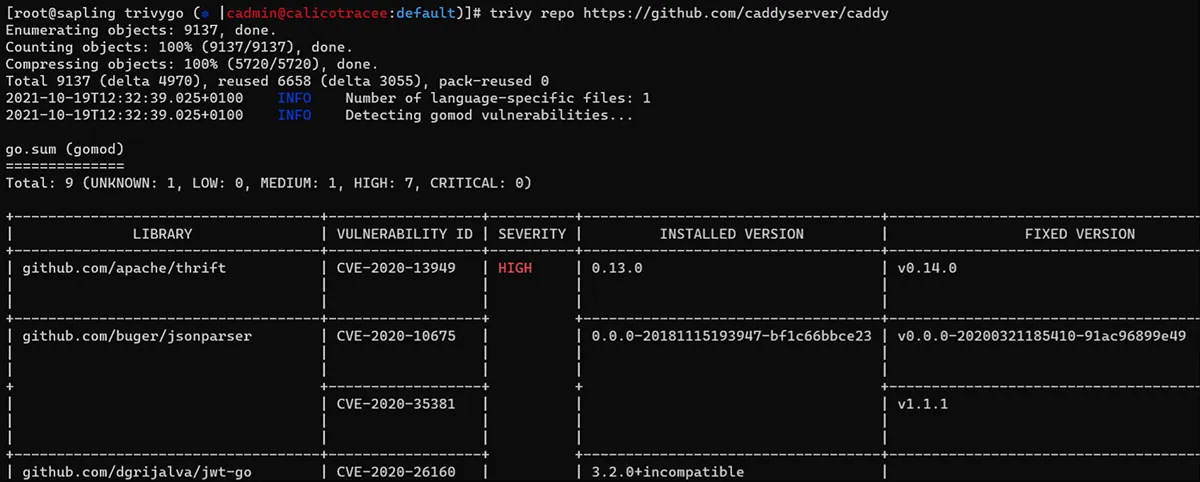
This approach is scanning the go.sum file found in the repository and looking at the version information there.
Summary
When implementing security measures like minimizing the size of container images, it’s always important to consider the trade-offs. In some cases, it may be necessary to change the approach to vulnerability scanning to ensure that vulnerabilities are still detected appropriately. As we saw, with Trivy, this process is easy to handle.

